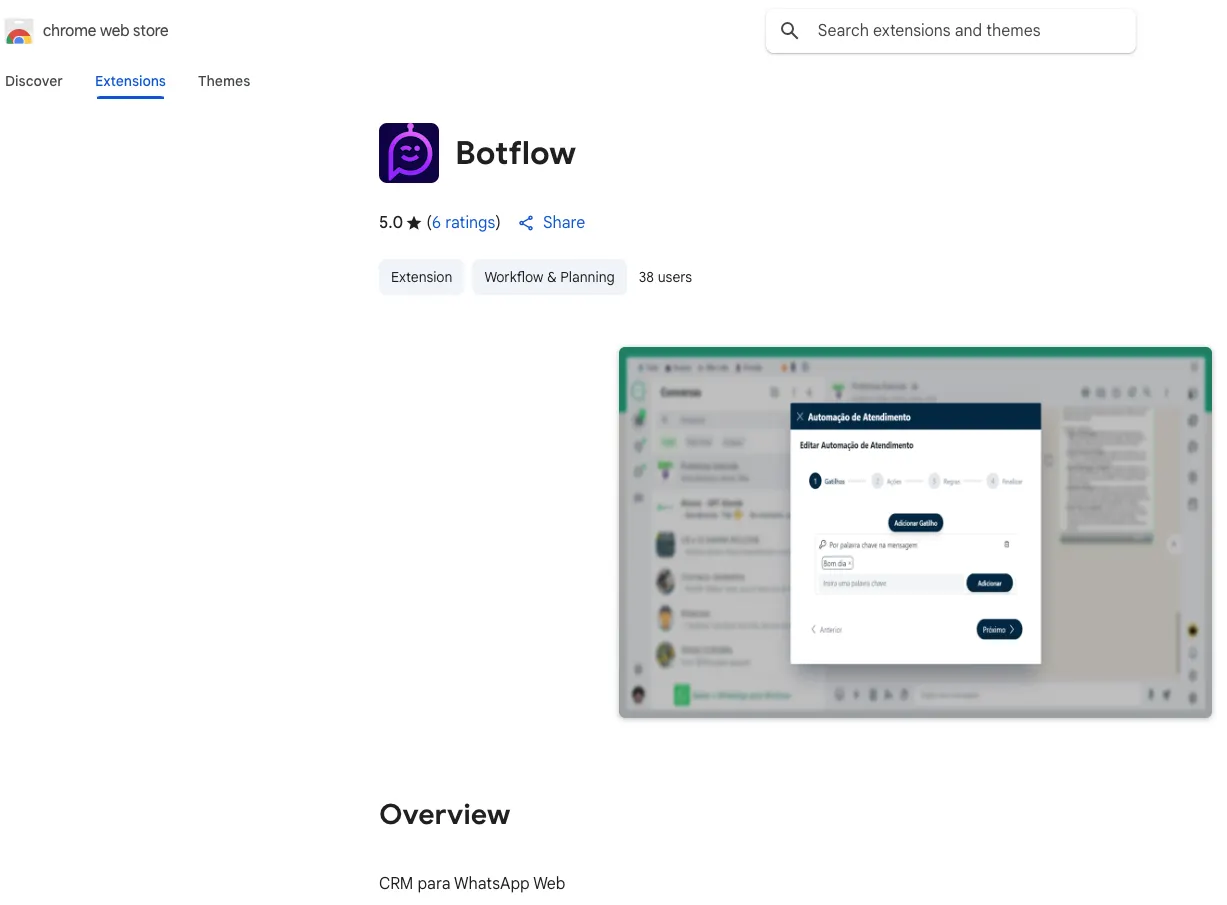
A brand new wave of spamware focusing on WhatsApp Net customers has emerged, because the Socket Risk Analysis Workforce revealed the invention of 131 malicious Chrome extensions actively flooding the Chrome Net Retailer.
These extensions are usually not standard malware, however perform as high-risk automation instruments, systematically violating platform insurance policies to facilitate large-scale spam campaigns, primarily focusing on Brazilian customers.
Reseller Mannequin Creates Clone Flood
On the core of this operation lies a single WhatsApp Net automation device, cloned and rebranded into 131 distinct extensions. Regardless of sporting distinctive names, logos, and advertising and marketing websites, all clones share the identical codebase, design patterns, and backend infrastructure.
Branding variations masks the underlying actuality: over 80 of those extensions sport the label “WL Extensão” or a near-identical variant, however all have been revealed by simply two developer accounts linked to the Brazilian firm DBX Tecnologia and its affiliate, Grupo OPT.
Key traits of the operation embrace:
- 131 rebranded clones of a single WhatsApp Net automation device.
- All extensions share equivalent codebase and infrastructure.
- Printed by means of solely two developer accounts: suporte@grupoopt.com.br and kaio.feitosa@grupoopt.com.br.
- Extensions branded below WL Extensão and WLExtensao labels throughout 83 listings.
- Marketing campaign has been working for at the very least 9 months with common updates by means of 2025.
This construction mimics a franchise enterprise mannequin. For a licensing price, resellers obtain a customizable construct—brand, identify, and interface tweaks included however the backend and core code stay unchanged and managed centrally.
DBX Tecnologia advertises the enterprise as a profitable “white-label partnership,” promising recurring income streams and wholesome margins for resellers.
The consequence is a multi-pronged operation, with resellers publishing near-identical instruments and flooding the market by means of advertising and marketing websites, YouTube, LinkedIn, and different channels.
Bypassing Insurance policies and Focusing on Customers
The aim of those extensions is obvious: automate bulk messaging by way of WhatsApp Net, together with scheduling and template options that evade WhatsApp’s anti-spam algorithms.
The software program injects code straight into the WhatsApp Net web page, orchestrating unsolicited outreach in bulk, all whereas working alongside legit WhatsApp scripts.
Promotion supplies and tutorials spotlight methods to tweak message intervals and supply patterns particularly to bypass detection techniques.
Coverage violations and technical mechanisms:
- Code injection straight into WhatsApp Net pages alongside legit scripts.
- Automated bulk messaging and scheduling techniques designed to bypass anti-spam controls.
- Violation of Chrome Net Retailer insurance policies prohibiting duplicate extensions and spam.
- Circumvention of WhatsApp’s Enterprise Messaging coverage requiring specific opt-in.
- Advertising supplies falsely declare Chrome Net Retailer presence ensures safety audits.
Claims that Chrome Net Retailer presence ensures rigorous code audits or privateness compliance are deceptive.
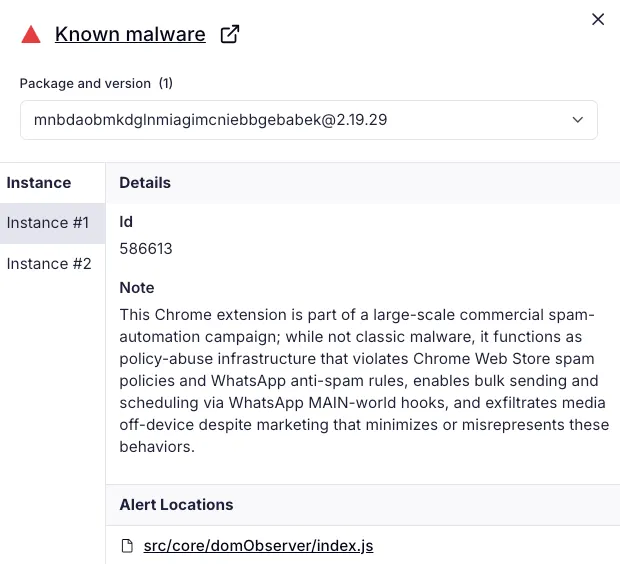
Precise abuse of the Chrome Net Retailer’s insurance policies is central to the operation: Google explicitly forbids duplicate extensions, mass spam, and sending messages with out consumer consent.
In the meantime, WhatsApp’s Enterprise Messaging coverage calls for specific opt-in and speedy honoring of block requests — necessities systematically skirted by this marketing campaign.
Broad Affect, Ongoing Risk
Collectively, these 131 extensions account for at the very least 20,905 lively customers. Socket’s AI safety evaluation flagged examples like “Arrange-C” for direct coverage violations. At time of publication, all extensions stay stay, although takedown requests have been submitted.
For customers and organizations, this marketing campaign underscores the pressing want for safety controls: restrict Chrome extension installations to trusted sources, use stock and permission evaluation instruments, and carefully monitor for suspicious behaviors.
With bulk messaging spam on the rise, strong countermeasures are a should for anybody counting on WhatsApp for enterprise or private communication.
Comply with us on Google Information, LinkedIn, and X to Get On the spot Updates and Set GBH as a Most popular Supply in Google.

