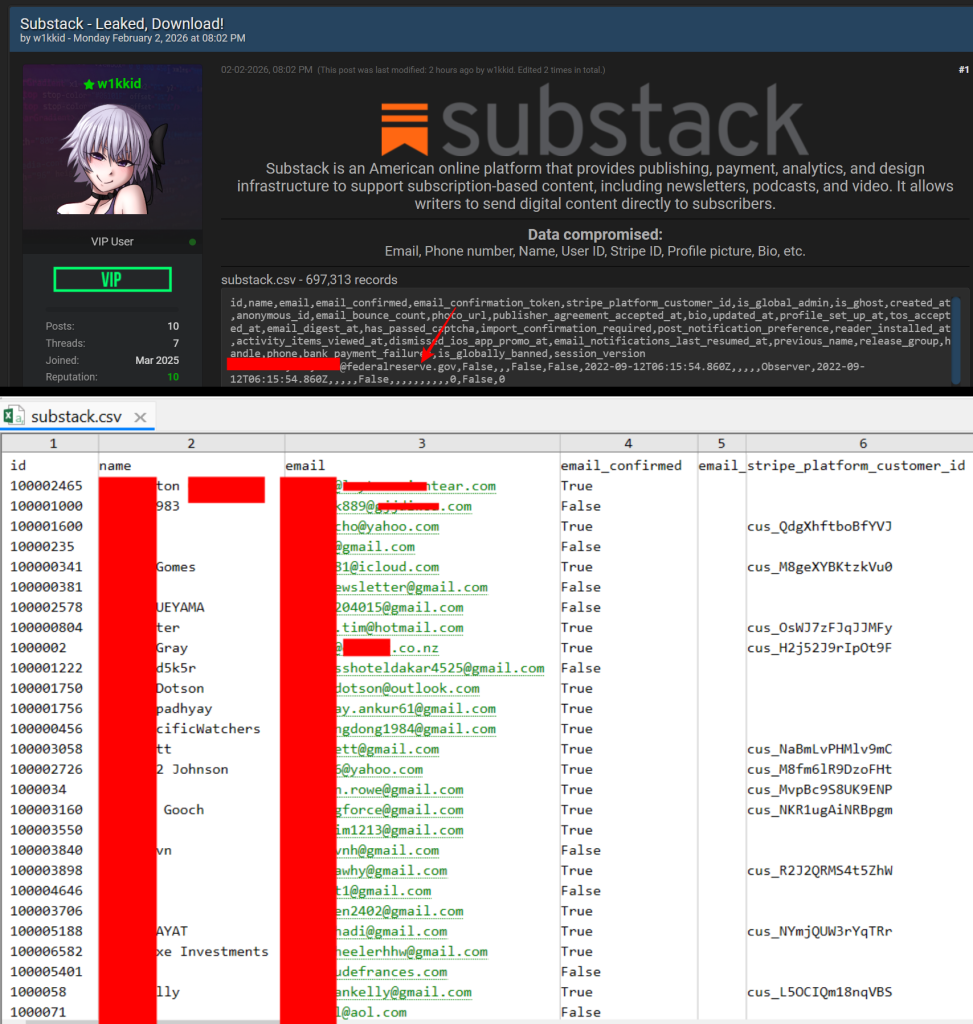
Three days earlier than Substack advised customers a few safety incident, a really totally different model of the story was already circulating in underground cyber crime boards. On February 2, 2026, a BreachForums person utilizing the alias “w1kkid” claimed to have scraped Substack and extracted near 700,000 (662,752) person data. By February 5, Substack’s CEO confirmed that person knowledge had been accessed with out permission, setting off questions on scale, timing, and what was actually taken.
Substack’s notification to customers described a system subject that allowed an unauthorized third occasion to entry restricted person knowledge. The corporate stated it recognized the issue on February 3 and traced the unauthorized entry again to October 2025. In keeping with the e-mail, uncovered knowledge included e-mail addresses, cellphone numbers, and inside metadata, whereas passwords and monetary data weren’t accessed.
What the Uncovered Substack Information Exhibits
Nonetheless, the information shared on BreachForums reveals a extra detailed image of what that entry could have regarded like. Pattern rows present what look like full person account data, every linked to a singular numeric ID and account creation dates, replace timestamps, notification preferences, and moderation flags. These should not the sorts of fields seen on public profile pages.
After indepth analyssi of the complete database Hackread discovered that a number of data belong to energetic publishers reasonably than passive readers. Writer settlement acceptance timestamps seem within the knowledge, together with e-newsletter handles, biographies, and profile photos hosted on Substack’s personal S3 buckets. This means that creator accounts, together with these linked to monetized publications, have been a part of the uncovered dataset.
Stripe platform buyer IDs seem throughout a number of entries. Whereas these identifiers don’t expose fee card particulars, they instantly hyperlink Substack accounts to Stripe buyer objects. From a safety perspective, that connection will increase the sensitivity of the information as a result of it permits correlation between id data and fee methods.
Telephone numbers are additionally current for customers in a number of international locations, alongside verified e-mail addresses and lengthy account histories. Some accounts date again to 2018, whereas others present updates as late as 2025. This combine suggests a broad snapshot of person knowledge reasonably than selective assortment of latest or public profiles.
The inner nature of the fields included is troublesome to reconcile with a easy scrape. Flags reminiscent of is_global_admin, is_ghost, is_globally_banned, session_version, and has_passed_captcha are backend indicators utilized by the platform itself. Their presence suggests entry to inside methods or knowledge exports reasonably than harvesting via public interfaces.
No Proof of Information Abuse So Far?
Substack stated it has no proof that the information is being misused and that it has mounted the underlying subject. In breach investigations, that normally means no confirmed abuse has been detected but. Datasets of this sort usually flow into privately earlier than getting used for phishing, impersonation, or focused social engineering. Hackread.com can verify that this particular Substack is now circulating on a number of Russian talking cyber crime discussion board as we effectively exchanged on Telegram.
For impacted customers, the principle threat now could be focused phishing. Emails or textual content messages could arrive that reference your Substack account, e-newsletter title, bio, or signup historical past to seem reputable. Don’t click on hyperlinks, obtain attachments, or reply to messages claiming to be from Substack, Stripe, or subscribers asking for verification or fee particulars.
Entry your account solely by typing the official website handle instantly into your browser, and ignore messages that create urgency or request one-time codes, password resets, or account affirmation. In case you use the identical e-mail or cellphone quantity on different companies, look ahead to related messages there as effectively.