Govt Abstract
The Black Lotus Labs workforce at Lumen Applied sciences has uncovered new infrastructure behind the “SystemBC” botnet, a community composed of over 80 C2s with a each day common of 1,500 victims, almost 80% of that are compromised VPS programs from a number of giant industrial suppliers. The victims are made into proxies that allow excessive volumes of malicious site visitors to be used by a bunch of legal menace teams. By manipulating VPS programs as a substitute of units in residential IP house as is typical in malware-based proxy networks, SystemBC can supply proxies with large quantities of quantity for longer durations of time. Comparable, high-bandwidth proxies in residential IP house would alert and disrupt customers of smaller, decrease bandwidth units.
Black Lotus Labs has noticed these proxies in use by a number of networks within the legal ecosystem; together with a minimum of two completely different Russia-based proxy companies, one Vietnamese proxy service, and a Russian parsing service. Whereas promoting the identical bots on a number of platforms, the service generates very giant quantities of site visitors with out regard to the eye it attracts – almost 100% of the bots are finally listed on “block record” websites for mass scanning, exploitation, and brute forcing.
One major person of the SystemBC botnet is an attention-grabbing proxy community referred to as “REM Proxy,” which gives roughly 80% of the SystemBC community to their customers. REM Proxy is a sizeable community, which additionally markets a pool of 20,000 Mikrotik routers and a wide range of open proxies it finds freely obtainable on-line. This service has been a favourite for a number of actors resembling these behind TransferLoader, which has ties to the Morpheus ransomware group. REM Proxy is marketed in a devoted legal discussion board created for it and 4 different companies that supply extra supporting capabilities for attackers.
Lumen Applied sciences has blocked all site visitors throughout our world community, to or from the devoted infrastructure related to the SystemBC and REM Proxy botnet. We’re releasing indicators of compromise (IoCs) to assist others establish and take defensive measures, disrupt this operation, and influence the bigger cybercrime ecosystem.
Black Lotus Labs want to thank our companions at Spur, Infoblox and others all through the trade for his or her contribution to our efforts to trace and mitigate this menace.
Introduction
A serious concern for any menace actor is to cover their on-line exercise lengthy sufficient to conduct their plans with out alerting victims or regulation enforcement. Providers like TOR supply levels of anonymity; nonetheless, there are downsides like low bandwidth speeds and stability points. Devoted options like VPNs include a price and threat {that a} VPN supplier might disript or intervene”with menace actor exercise. Menace actors proceed to maneuver in the direction of proxy companies resembling NSOCKS and ProxyAM, providing 1000’s and even tens of millions of residential units by way of which to cross site visitors in almost any bodily location on the planet. Some proxy swimming pools, just like the pair talked about above in addition to TheMoon, are created solely from different botnets. Black Lotus Labs tracked the SystemBC community for a number of months, because it fed immediately into a number of different companies now we have noticed over the identical time.
Whereas we couldn’t decide the preliminary entry vector utilized by SystemBC operators, our analysis revealed that, on common, every sufferer exhibits 20 unpatched CVEs and a minimum of one crucial CVE – with one tackle proven as having over 160 unpatched vulnerabilities.
The SystemBC malware was initially documented in 2019 by Proofpoint. It’s commoditized in underground boards and often utilized by a wide range of legal menace teams. Its core design is to open proxy performance on victims and will be configured to allow the retrieval and execution of extra malware. SystemBC has been extraordinarily efficient over its lifetime, gaining the eye of regulation enforcement throughout Operation Endgame given its capacity to facilitate the deployment of ransomware. This well-rounded community has been used along with infamous entities resembling IcedID and Trickbot.
Malware Evaluation
The samples we examined, together with these talked about by Polyswarm, don’t seem to have any extra performance apart from proxying site visitors. The primary pattern, 1c74b1195250632f2f1d1a9066f07f6e0a8c12dff40aeb3c1fe22440c97bc8ee, is a Linux variant of the SystemBC malware. The malware first decrypts and connects to the C2 contained within the embedded config. The config is XOR encoded utilizing a hardcoded 40-byte key.
Determine 1: Decoding configuration
It then creates a payload composed of the composed of the 40-byte key, 10-bytes of padding, after which an encrypted beacon consisting of 0xffff adopted by forty-eight 0x00 bytes.
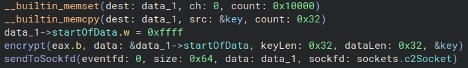
Determine 2: Encryption course of
The beacon is encrypted by first XORing the beacon with the important thing (as above), RC4 encrypting with stated key, after which XORing as soon as once more with the identical key.
Determine 3: C2 response and directions
The response from the C2 will embody a 4-byte header which is decrypted in the identical method that the preliminary payload was encrypted: XOR, RC4, XOR. The header accommodates the sort (new proxy (0), extra knowledge for an already open proxy (1), or exit execution (0xff).
World Telemetry
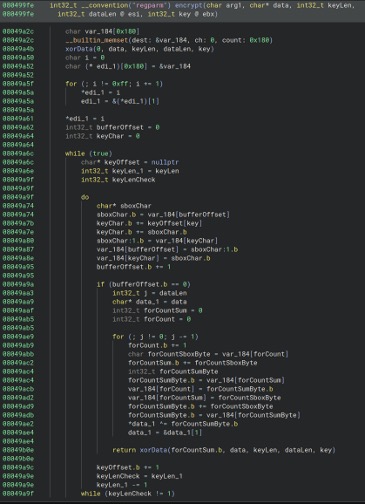
Customers of the proxy community attain out to SystemBC C2s on excessive numbered ports, which then sends the person by way of to one of many victims. This sample is proven within the picture under:
Determine 4: SystemBC proxy pipeline
Sufferer Evaluation
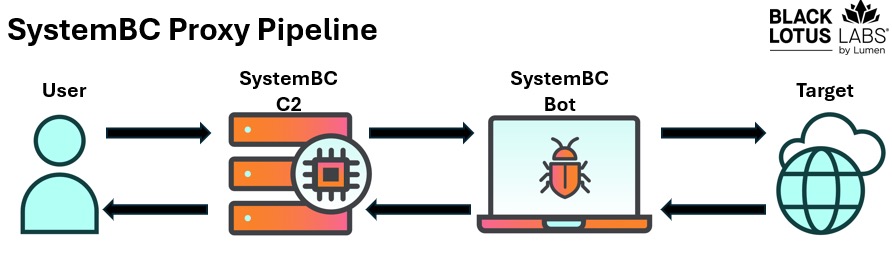
The pool of victims revealed that not like most botnets and proxy associated companies, the first targets had been VPS servers as a substitute of residential customers. Over a interval of examine lasting a number of months, SystemBC maintained a each day common of 1,500 bots, together with 300 which might be part of the GoBrut botnet.
Determine 5: Sufferer areas of the contaminated SystemBC bots
Of these 1,500 each day bots, near 80% got here from simply 5 giant industrial VPS suppliers. Provided that the victims are primarily VPSs, we additionally see extraordinarily lengthy common an infection lifetimes, the place near 40% keep contaminated for effectively over a month.
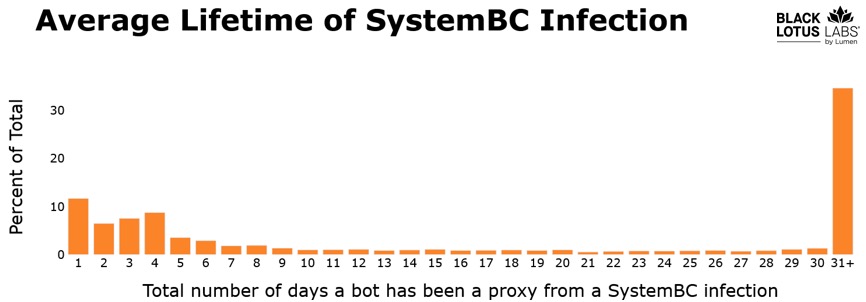
Determine 6: Exhibits the an infection lifespan for this SystemBC botnet. Near 40% of those infections final over a month
We couldn’t discover proof of particular concentrating on of VPS suppliers, nonetheless, we found that almost all victimized servers seemed to be riddled with simple to use vulnerabilities such because the one under which, in keeping with Censys, has over 160 unpatched CVEs.
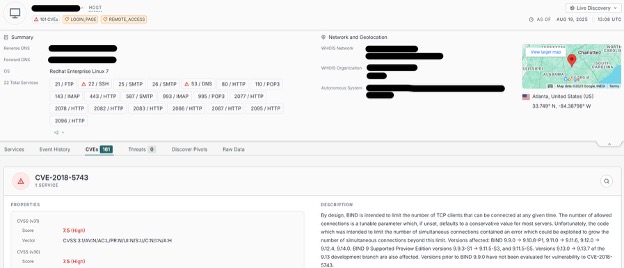
Determine 7: Instance of VPS sufferer within the SystemBC botnet with over 160 vulnerabilities
Evaluation of our world IP telemetry revealed that 104.250.164[.]214 seems to be the supply of assaults to recruit potential victims, in addition to the only real host of the SystemBC malware samples. Preliminary entry makes an attempt are despatched on port 443, and, if profitable, the brand new bot will name again on port 80 to obtain a shell script (with Russian feedback) that forces the obtain over 180 samples of the SystemBC malware. The script can even direct the sufferer to run each pattern concurrently, with every pattern beneath a separate file title. A picture displaying the method is under:
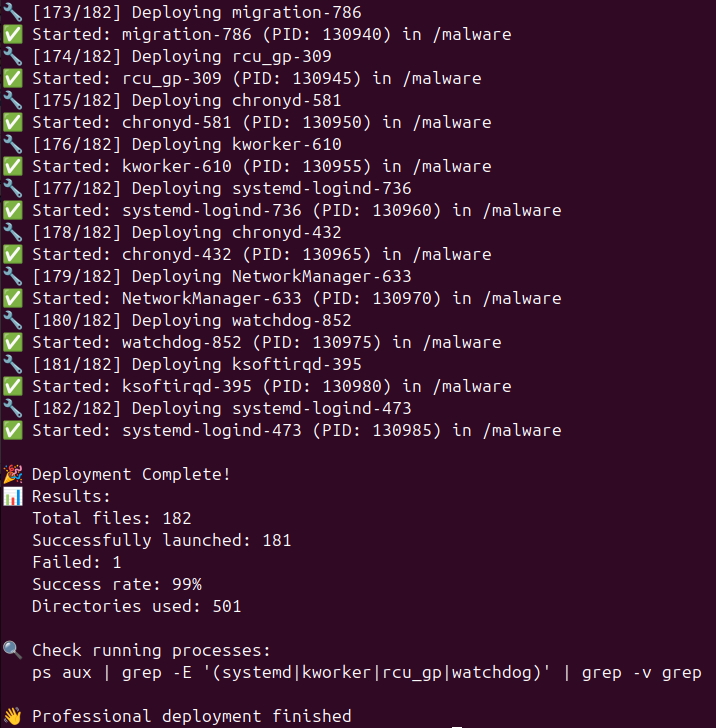
Determine 8: Instance of malware obtain from SystemBC host
When dissecting the C2 infrastructure we discovered that every one the SystemBC C2s had been operated beneath a single Autonomous System (AS). This AS is sufficiently small that the 80 C2s make up roughly 10% of their community.
Proxy Evaluation
Most proxy companies supply modest site visitors volumes per proxy, seldom reaching gigabyte-scale knowledge transfers regularly. This restraint is often attributed to the residential units that represent these networks, resembling Web of Issues (IoT) endpoints or legacy routers. Extreme site visitors routed by way of such units not solely dangers community instability resulting in potential discovery but in addition will increase the likelihood of the host’s IP tackle being blacklisted. Our evaluation means that the operators and clients of this botnet have little concern for evasion or stealth. For instance, the bots’ IP addresses are neither obfuscated nor systematically rotated to keep away from detection. Quantity appears to be the one concern; for one 24-hour window we noticed a selected IP tackle generate an extra of 16 gigabytes of proxy knowledge, which we confirmed by observing the malware in a simulated surroundings. This quantity of knowledge is an order of magnitude higher than what is usually noticed in typical proxy networks.
Our evaluation of netflow revealed a number of distinguished crime teams utilizing SystemBC victims as proxies and certain extra we didn’t discover. When grouping the person teams collectively it turns into clear how the victimized proxies can generate a lot malicious site visitors:
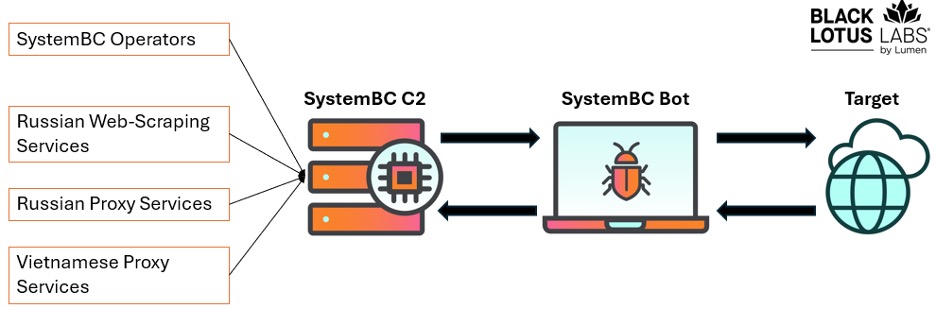
Determine 9: Recognized customers of the SystemBC botnet
The biggest use of the botnet is by the SystemBC operators themselves, utilizing their very own community to brute pressure WordPress credentials, then possible promoting the harvested credentials to brokers who inject the websites with malicious code.
The following largest person by quantity was a really giant Russian web-scraping service. Based mostly on site visitors evaluation, we noticed a direct connection between this companies’ structure and the SystemBC C2s on the person entry ports. This parsing service gives the choice of selecting between common and premium proxies. The SystemBC proxies are possible bought alongside their common proxies, as they market to customers who don’t care about IP high quality, or IPs which might be blacklisted or may get blocked simply.
We additionally noticed the Vietnamese-based VN5Socks (a.ok.a. Shopsocks5) proxy service providing these IPs of their service, just like their use of Ngioweb bots acquired by way of NSOCKS. It seems that after the Ngioweb takedown, VN5Socks diversified their sources and began shopping for from the actor behind this SystemBC botnet.
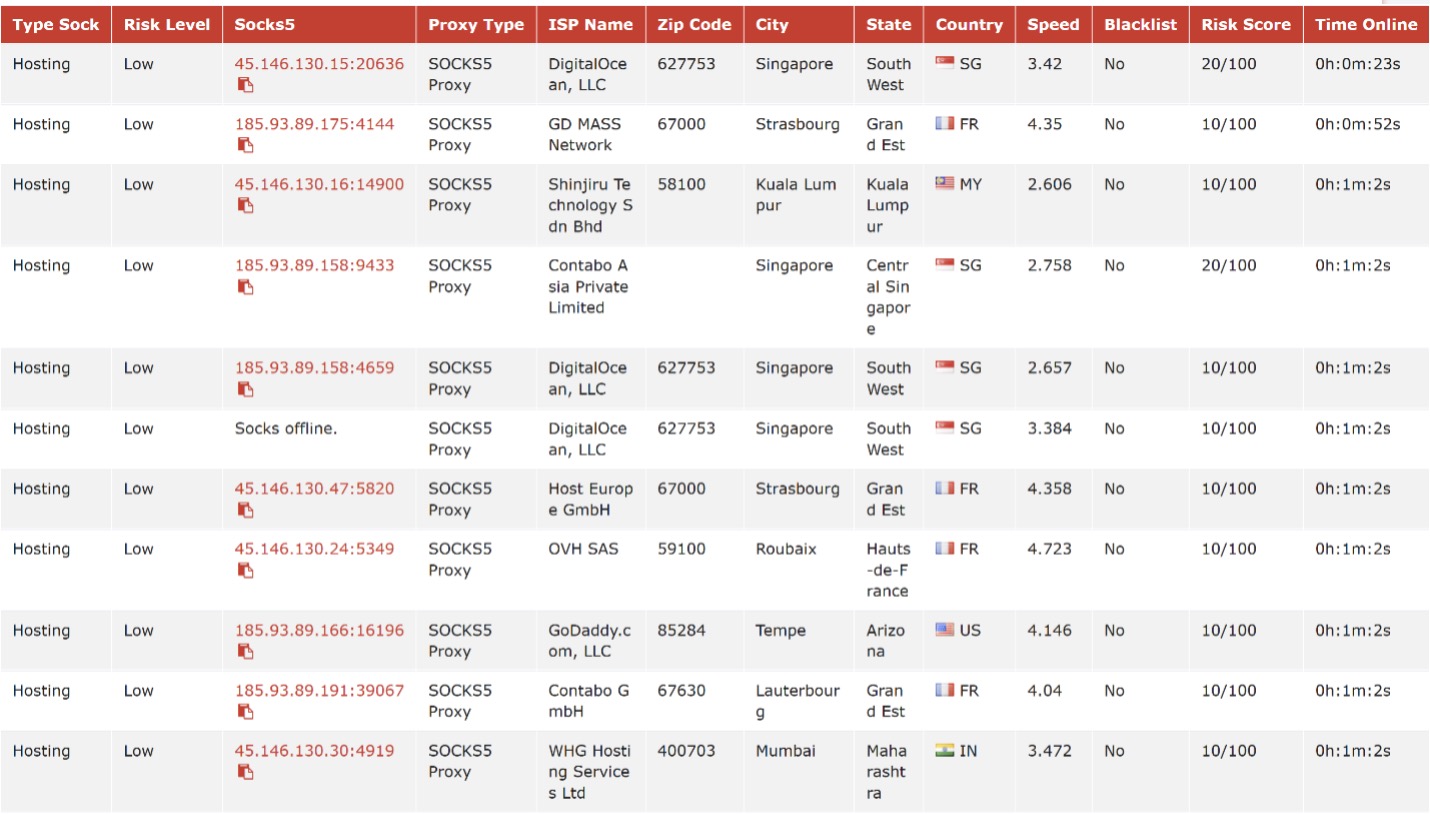
Determine 10: VN5Socks record of proxies which might be utilizing ports on our recognized SystemBC C2s
Cue the Remix
This brings us to REM (Remix) Proxy, essentially the most attention-grabbing service utilizing the SystemBC community. REM Proxy is a proxy service that has been leveraged by ransomware menace actors for a number of sides of their operations, together with the preliminary distribution of phishing emails, interplay with exfiltration servers, and entry to sufferer knowledge.

Determine 11: REM Proxy homepage
Evaluation has revealed connections between REM Proxy structure and ransomware actors courting again to a minimum of 2022, particularly involving the AvosLocker ransomware-as-a-service group, and extra not too long ago the Morpheus ransomware group. Over time, now we have noticed a number of distinct ransomware actors and menace teams incorporate REM Proxy into their knowledge switch pipelines. Again in January 2025, Infoblox wrote about an unknown Russian botnet powered by Mikrotik units. Black Lotus Labs labored with Infoblox and was in a position to assess with excessive confidence the botnet they got here throughout was actually REM Proxy. With their assist we had been capable of finding a 50% overlap between the IPs they noticed in earlier campaigns and ones we discovered as half of the present make-up of REM Proxy.
Based on analysis from Proofpoint, REM Proxy makes use of a base of compromised Mikrotik units, nonetheless, these units characterize solely a part of REM Proxy’s operational construction, which gives three distinct tiers of packages, every offering various capabilities and assets to its customers.
Their high-end tier is named “Combine-Velocity,” and gives proxies with very low detection charges, largely drawn from the pool of Mikrotik units and contains a few of the open proxies. These bots are nearly solely in residential IP house and look like ignored by most safety options. Additionally they specify that port 25 is left open, which is uncommon for proxy companies. That is helpful for menace actors centered on phishing and spamming e-mails; nonetheless, most main US residential ISPs block outbound site visitors on port 25 for that reason.
On their low-end tier (“Combine-Financial system”), they market proxies in the identical vein because the aforementioned parsing service, described as helpful for individuals who “aren’t demanding on the proxy high quality.” Virtually all proxies on this “Financial system” bundle look like these with excessive detection scores.
The excessive detection charges of the “Combine-Financial system” proxies may not pose a priority for a well-monitored community; nonetheless, they’re helpful in different phases of a malicious actor’s pipeline. For instance, actors might use “Combine-Financial system” IPs for brute pressure and credential harvesting, then transfer to the upper finish “Combine-Velocity” IPs to execute focused assaults with decrease visibility, utilizing info they acquired from the preliminary part of the operation.
Rounding out the REM proxy choices is a center tier known as “Combine-Combine,” which seems manufactured from random bots taken from each the high- and low-end tiers. This tier appears to combine economic system and pace for normal objective use.
REM Proxy World Telemetry
Evaluation of Lumen’s world netflow permits us to watch components of this community from the portal that customers work together with, by way of to the tip use of a given proxy. It doesn’t matter what tier a person buys, they seem to get bots from all three sources, based mostly on detection charges and high quality. In different phrases, the uncommon SystemBC sufferer with a low detection price, might be a part of the upper “Combine-Velocity” tier.
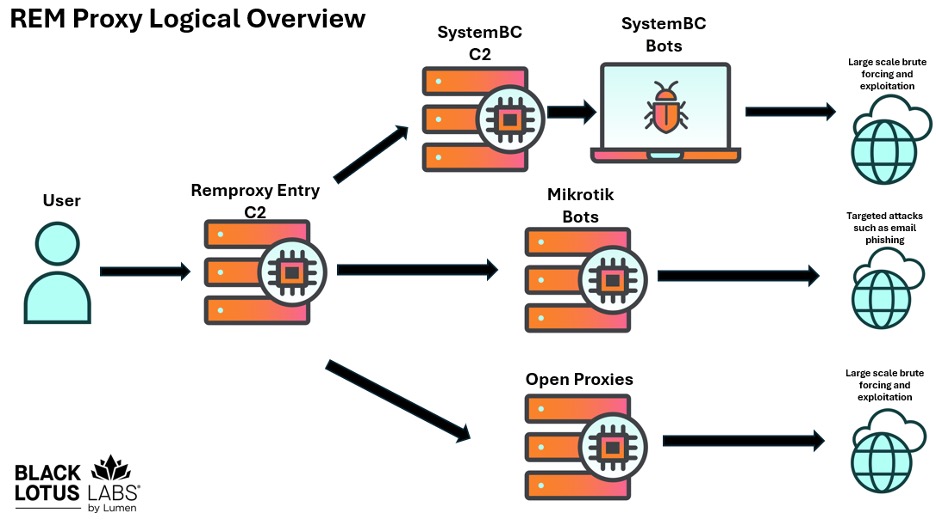
Determine 12: REM Proxy system overview.
When a person buys a REM Proxy subscription, they transfer to a display with a hyperlink to a “Proxy record URL” which supplies the person a menu for various proxies (or “threads”) to which they will join. An instance is proven under:
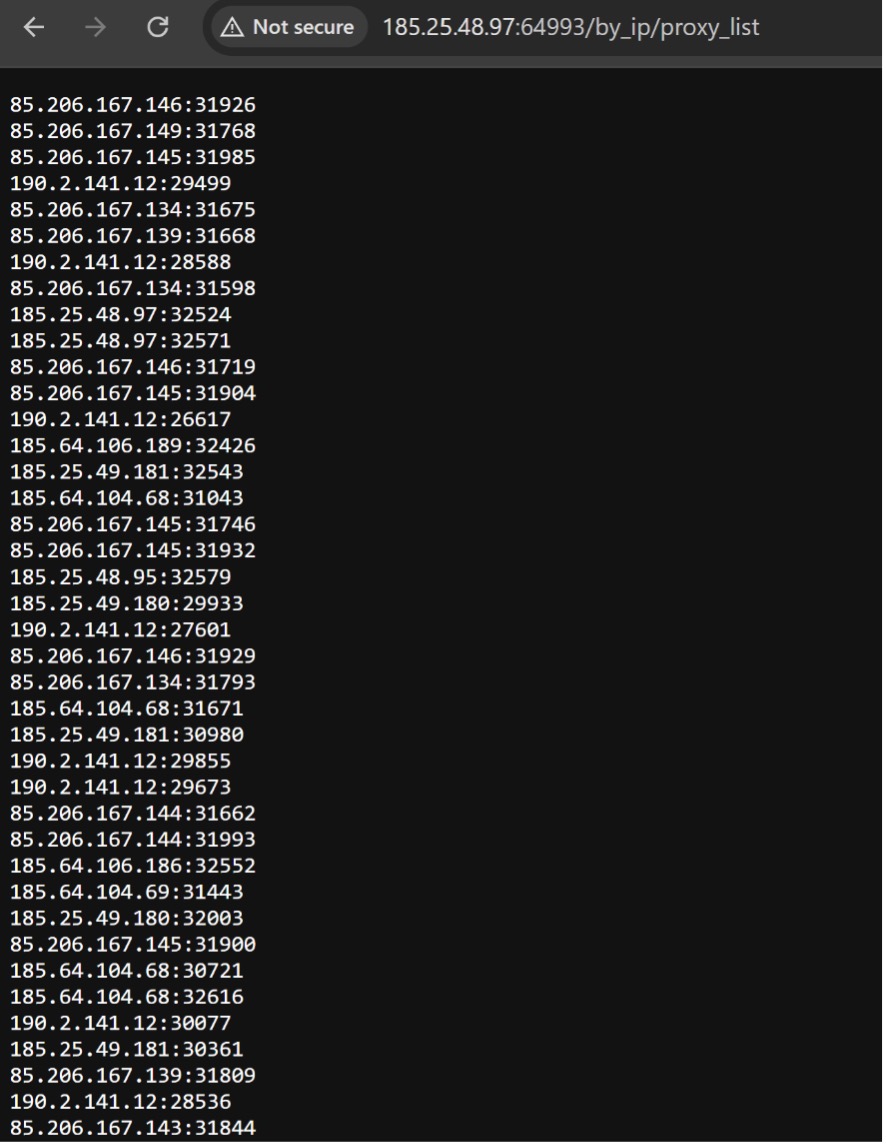
Determine 13: Checklist of IP and port combos obtainable to proxy site visitors
REM Proxy has shut to at least one hundred C2s obtainable for person connections. In our examine, the C2 connection was to 185.25.48[.]97, and our netflow revealed customers contacting REM Proxy C2s on random ports. Site visitors from those self same C2s then connects to: Mikrotik units on SSH port 51922, together with SystemBC C2s on the person entry ports, and lots of open proxies on ports resembling 1080, 8989 and comparable.
REM Proxy presents a singular case examine, each in its operational mechanics and in person interplay patterns throughout the community. Victimized units are introduced into the system by way of an alternate area, honipsiops[.]in, which seems to perform as a screening mechanism—permitting REM Proxy to establish new, accessible IP addresses and confirm their standing. Every day, roughly 3,000 IP addresses contact this web site, with an estimated 2,500 attributed to REM Proxy-related infections.
Lastly, when customers authenticate into the proxy service, they’re redirected to a cybercrime discussion board providing 5 distinct complimentary companies. REM Proxy is featured alongside options that embody electronic mail validation instruments and mechanisms for circumventing blacklists, amongst others:
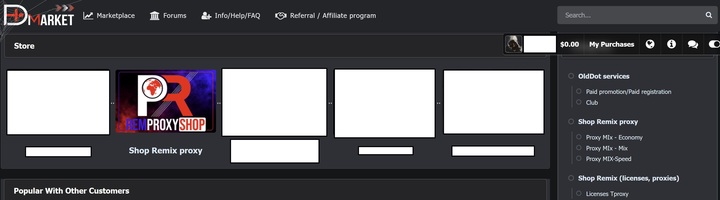
Determine 14: discussion board that includes REM Proxy alongside ancillary companies
Conclusion
SystemBC has exhibited sustained exercise and operational resilience throughout a number of years, establishing itself as a persistent vector throughout the cyber menace panorama. Initially utilized by menace actors to allow ransomware campaigns, the platform has advanced to supply the meeting and sale of bespoke botnets. In contrast to conventional SOHO-based botnets that supply nice measurement or stealth, SystemBC’s use of VPSs is geared towards quantity and brute pressure.
Their mannequin gives appreciable benefits: it permits the execution of widespread reconnaissance, spam dissemination, and associated actions, permitting an attacker to order extra selective proxy assets for focused assaults knowledgeable by prior intelligence gathering. Business proxy suppliers resembling REM Proxy have tailored to this mannequin by introducing tiered service packages, supporting the total spectrum of malicious operations, from preliminary reconnaissance to lively exploitation.
Alone or collectively, these two entities exhibit a few of the adaptive methods of each menace actors and supporting service suppliers throughout the cybercriminal ecosystem. Black Lotus Labs continues to observe and observe giant scale botnets resembling these, to assist shield and higher safe the web as a complete. To that finish, now we have blocked site visitors throughout the Lumen world spine to all of the structure associated to the SystemBC and REM Proxy botnets. Now we have added the indications of compromise (IoCs) from this marketing campaign into the menace intelligence feed that fuels the Lumen Related Safety portfolio. We are going to proceed to observe new infrastructure, concentrating on exercise, and increasing TTPs; and collaborate with the safety analysis group to share findings associated to this exercise.
Now we have an inventory of IoCs obtainable on our GitHub, and encourage the group to observe for and alert on these and any comparable IoCs
Company Community Defenders:
- Proceed to search for assaults on weak credentials and suspicious login makes an attempt, even after they originate from residential IP addresses which bypass geofencing and ASN-based blocking.
- Defend cloud property from speaking with bots that try to carry out password spraying assaults and start blocking IoCs with Internet Utility Firewalls.
- Examine the IP tackle of any bought VPS towards companies like Censys, or public block lists.
Shoppers with SOHO routers:
- Customers ought to comply with greatest practices of often rebooting routers and putting in safety updates and patches. For steerage on find out how to carry out these actions, please see the “greatest practices” doc ready by Canadian Centre for Cybersecurity.
- For Organizations that handle SOHO routers: be sure units don’t depend on frequent default passwords. They need to additionally make sure that the administration interfaces are correctly secured and never accessible through the web. For extra info on securing administration interfaces, please see DHS’ CISA BoD 23-02 on securing networking gear.
- We additionally advocate changing units as soon as they attain their producer finish of life and are not supported.
Evaluation of SystemBC and REM Proxy was carried out by Chris Formosa and Steve Rudd. Technical enhancing by Ryan English.
Submit Views: 2

