The North Korean state-sponsored Lazarus hacking group has launched a classy cyberespionage marketing campaign focusing on European protection contractors concerned in uncrewed aerial automobile (UAV) manufacturing.
The assaults seem straight linked to North Korea’s efforts to speed up its home drone manufacturing capabilities by industrial espionage.
The focused organizations embrace a steel engineering agency, an plane element producer, and a specialised protection firm, with at the least two closely concerned in UAV expertise improvement and manufacturing.
The marketing campaign represents a brand new wave of Operation DreamJob, Lazarus’s signature social engineering operation that makes use of faux job provides at prestigious firms as bait.
Beginning in late March 2025, ESET recognized a number of assaults focusing on three defense-sector firms throughout Southeastern and Central Europe.
Victims obtain fraudulent job descriptions alongside trojanized PDF readers, which ship malware when executed. This misleading tactic has confirmed remarkably efficient regardless of widespread safety consciousness campaigns.
The attackers deployed ScoringMathTea, a classy distant entry trojan (RAT) that has served as Lazarus’s payload of alternative for 3 years.
BinMergeLoader leverages the Microsoft Graph API and makes use of Microsoft API tokens for authentication.
First noticed in October 2022, ScoringMathTea helps roughly 40 instructions, enabling attackers to govern information and processes, gather system data, set up TCP connections, and execute downloaded payloads.
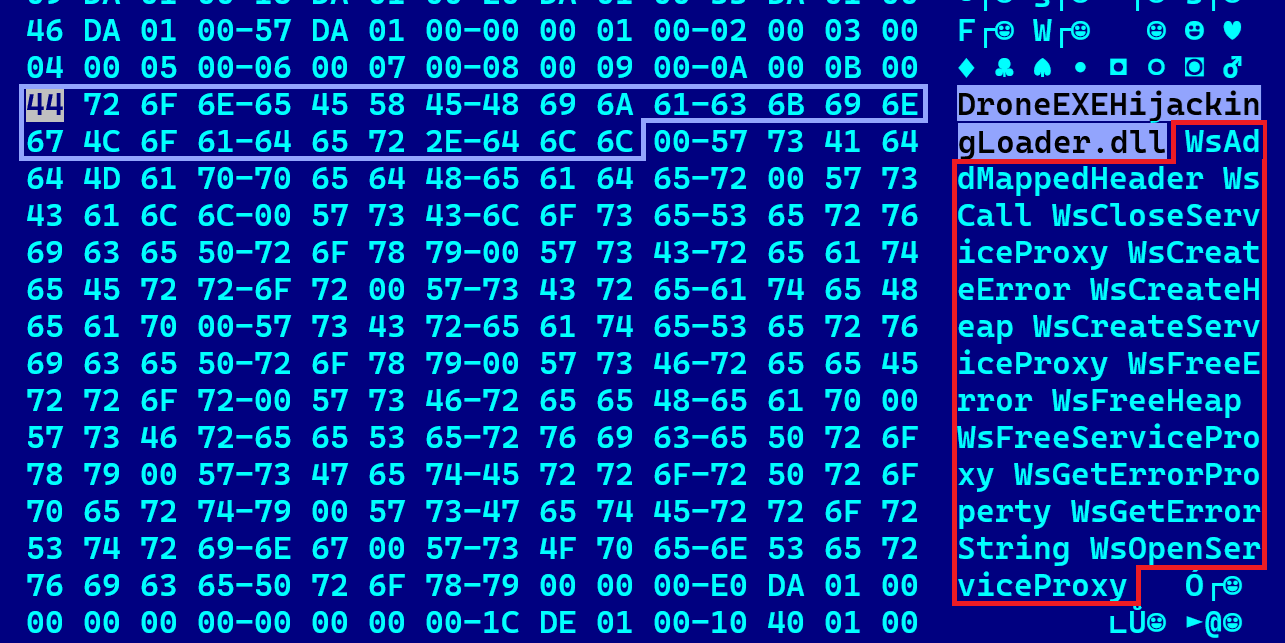
One dropper pattern found by researchers contained the interior title “DroneEXEHijackingLoader.dll,” offering a direct hyperlink to the marketing campaign’s give attention to UAV expertise theft.
The malware leverages DLL side-loading methods and trojanizes professional open-source initiatives from GitHub together with TightVNC Viewer, MuPDF reader, and plugins for Notepad++ and WinMerge to evade detection.
ESET researchers famous vital evolution within the group’s ways, together with new DLL proxying libraries and improved number of open-source initiatives for trojanization.
The malware makes use of compromised WordPress servers for command-and-control communication, usually storing server parts inside theme or plugin directories.
The timing and goal choice strongly recommend the marketing campaign goals to steal proprietary UAV designs, manufacturing processes, and industrial know-how.
North Korea has invested closely in home drone capabilities, with current studies indicating Pyongyang is creating low-cost assault UAVs for potential export to African and Center Jap markets. Russia is reportedly aiding North Korea in producing knockoff Iranian Shahed suicide drones.
North Korea’s flagship reconnaissance drone, the Saetbyol-4, seems as a carbon copy of the Northrop Grumman RQ-4 World Hawk, whereas the Saetbyol-9 fight drone intently resembles Common Atomics’ MQ-9 Reaper.
These designs show North Korea’s reliance on reverse engineering and mental property theft to advance its navy capabilities.
No less than one focused firm manufactures vital parts for UAV fashions at the moment deployed in Ukraine, which North Korean forces could have encountered on the frontline in Russia’s Kursk area, the place North Korean troops had been deployed in 2025.
Moreover, the corporate is concerned in superior single-rotor drone improvement unmanned helicopter expertise that Pyongyang is actively creating however has not efficiently militarized.
Attribution and Broader Context
ESET attributed the assaults to Lazarus with excessive confidence based mostly on a number of indicators: the social engineering methodology, trojanization of GitHub open-source initiatives for DLL side-loading, deployment of ScoringMathTea, and focusing on of European aerospace and protection sectors.
Lazarus, also referred to as HIDDEN COBRA, is a complicated persistent risk (APT) group linked to North Korean intelligence companies and lively since at the least 2009.
The group is liable for high-profile incidents together with the 2016 Sony Footage Leisure hack, tens-of-millions-of-dollar cyberheists, the 2017 WannaCry ransomware outbreak, and ongoing assaults towards South Korean infrastructure.
Safety consultants advocate protection contractors implement rigorous worker coaching on social engineering ways, notably faux recruitment lures.
Organizations ought to scrutinize job provides from surprising sources, confirm executable information earlier than opening, and deploy superior endpoint detection options able to figuring out trojanized professional software program.
Community segmentation and privileged entry administration can restrict lateral motion if preliminary compromise happens.
IoCs
| SHA-1 | Filename | Detection | Description |
|---|---|---|---|
| 28978E987BC59E75CA22562924EAB93355CF679E | TSMSISrv.dll | Win64/NukeSped.TL | QuanPinLoader. |
| 5E5BBA521F0034D342CC26DB8BCFECE57DBD4616 | libmupdf.dll | Win64/NukeSped.TE | A loader disguised as a MuPDF rendering library v3.3.3. |
| B12EEB595FEEC2CFBF9A60E1CC21A14CE8873539 | radcui.dll | Win64/NukeSped.TO | A dropper disguised as a RemoteApp and Desktop Connection UI Part library. |
| 26AA2643B07C48CB6943150ADE541580279E8E0E | HideFirstLetter.DLL | Win64/NukeSped.TO | BinMergeLoader. |
| 0CB73D70FD4132A4FF5493DAA84AAE839F6329D5 | libpcre.dll | Win64/NukeSped.TP | A loader that may be a trojanized libpcre library. |
| 03D9B8F0FCF9173D2964CE7173D21E681DFA8DA4 | webservices.dll | Win64/NukeSped.RN | A dropper disguised as a Microsoft Net Companies Runtime library. |
| 71D0DDB7C6CAC4BA2BDE679941FA92A31FBEC1FF | N/A | Win64/NukeSped.RN | ScoringMathTea. |
| 87B2DF764455164C6982BA9700F27EA34D3565DF | webservices.dll | Win64/NukeSped.RW | A dropper disguised as a Microsoft Net Companies Runtime library. |
| E670C4275EC24D403E0D4DE7135CBCF1D54FF09C | N/A | Win64/NukeSped.RW | ScoringMathTea. |
| B6D8D8F5E0864F5DA788F96BE085ABECF3581CCE | radcui.dll | Win64/NukeSped.TF | A loader disguised as a RemoteApp and Desktop Connection UI Part library. |
| 5B85DD485FD516AA1F4412801897A40A9BE31837 | RCX1A07.tmp | Win64/NukeSped.TH | A loader of an encrypted ScoringMathTea. |
| B68C49841DC48E3672031795D85ED24F9F619782 | TSMSISrv.dll | Win64/NukeSped.TL | QuanPinLoader. |
| AC16B1BAEDE349E4824335E0993533BF5FC116B3 | cache.dat | Win64/NukeSped.QK | A decrypted ScoringMathTea RAT. |
| 2AA341B03FAC3054C57640122EA849BC0C2B6AF6 | msadomr.dll | Win64/NukeSped.SP | A loader disguised as a Microsoft DirectInput library. |
| CB7834BE7DE07F89352080654F7FEB574B42A2B8 | ComparePlus.dll | Win64/NukeSped.SJ | A trojanized Notepad++ plugin disguised as a Microsoft Net Companies Runtime library. A dropper from VirusTotal. |
| 262B4ED6AC6A977135DECA5B0872B7D6D676083A | tzautosync.dat | Win64/NukeSped.RW | A decrypted ScoringMathTea, saved encrypted on the disk. |
| 086816466D9D9C12FCADA1C872B8C0FF0A5FC611 | N/A | Win64/NukeSped.RN | ScoringMathTea. |
| 2A2B20FDDD65BA28E7C57AC97A158C9F15A61B05 | cache.dat | Win64/NukeSped.SN | A downloader just like BinMergeLoader constructed as a trojanized NPPHexEditor plugin. |
Observe us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most well-liked Supply in Google.

