A vulnerability affecting the Mitsubishi Electrical Iconics Suite, a broadly deployed supervisory management and knowledge acquisition (SCADA) system used throughout industrial sectors, together with automotive, power, and manufacturing.
The flaw, tracked as CVE-2025-0921, carries a CVSS rating of 6.5 (Medium severity) and allows attackers to set off denial-of-service (DoS) circumstances on affected methods, compromising operational availability.
Vulnerability Overview
| CVE Identifier | Vulnerability Description | CVSS Rating |
|---|---|---|
| CVE-2025-0921 | Execution with pointless privileges vulnerability in a number of providers of Mitsubishi Electrical Iconics Digital Options GENESIS64 | 6.5 – Medium |
In keeping with Paloalto Community, the vulnerability stems from privileged file system operations inside the Iconics Suite’s AlarmWorX64 MMX Pager Agent element.
When exploited, attackers with native non-administrative entry can manipulate essential system binaries, resulting in system corruption and rendering industrial management methods inoperable.
The flaw impacts Microsoft Home windows variations 10.97.2 and earlier of the Iconics Suite.
CVE-2025-0921 permits menace actors to misuse privileged file system operations by manipulating the SMSLogFile configuration path saved within the IcoSetup64.ini file.
Attackers can create symbolic hyperlinks redirecting logging operations to essential Home windows drivers equivalent to cng.sys, which offers cryptographic providers important for system boot processes.
The exploitation turns into significantly efficient when mixed with CVE-2024-7587, a separate vulnerability within the GenBroker32 installer that grants extreme file permissions to the C:ProgramDataICONICS listing.
This permission misconfiguration permits any native person to switch configuration recordsdata that ought to be restricted to directors.
Assault Methodology
In a proof-of-concept demonstration, researchers confirmed how an attacker with non-privileged entry might redirect SMS logging operations to overwrite the cng.sys driver.
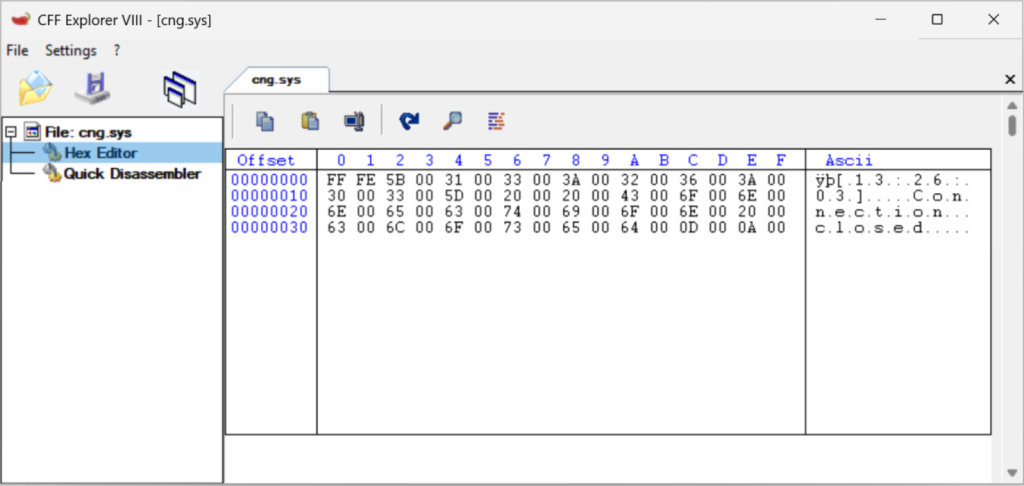
By making a symbolic hyperlink from the configured SMSLogFile path to C:WindowsSystem32cng.sys, subsequent SMS alert operations corrupt the motive force file with log knowledge as an alternative of legitimate binary code.
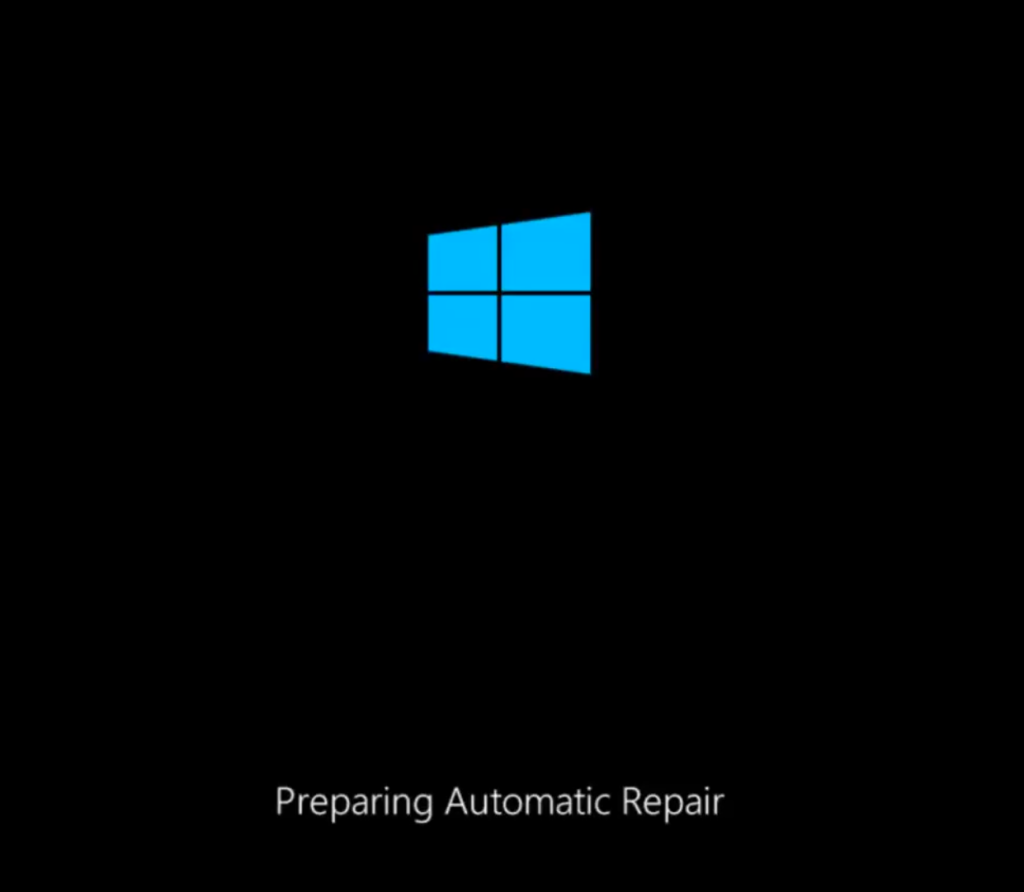
Upon system reboot, Home windows makes an attempt to load the corrupted driver, leading to boot failure and an infinite restore loop.
This creates a persistent DoS situation on essential operational expertise (OT) engineering workstations, probably disrupting industrial monitoring and management operations.
Mitsubishi Electrical has launched a safety advisory detailing remediation measures for CVE-2025-0921.
System directors ought to instantly apply the really helpful workarounds, which deal with all vulnerabilities recognized within the Iconics Suite evaluation.
Industrial organizations working Iconics Suite variations 10.97.2 and earlier ought to prioritize patching and implement the vendor-recommended safety controls to stop potential service disruptions.
The vulnerability highlights the essential significance of correct entry controls and privilege administration in industrial management system environments the place availability is paramount.
Comply with us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most well-liked Supply in Google.

