A widespread ransomware marketing campaign focusing on misconfigured MongoDB databases continues to compromise hundreds of servers worldwide, with attackers exploiting internet-exposed cases that lack fundamental authentication controls.
Current analysis reveals that opportunistic menace actors are leveraging automated scripts to wipe databases and demand Bitcoin ransoms, turning configuration negligence right into a scalable extortion operation.
Assault Resurfaces After Years of Silence
Between 2017 and 2021, MongoDB ransomware campaigns affected hundreds of organizations globally.
Whereas public reporting declined in subsequent years, latest investigations exhibit the menace by no means disappeared.
In late 2025, safety researchers deployed honeypot infrastructure exposing MongoDB cases with out authentication throughout a number of geolocations.
Inside days, all honeypot servers acquired ransom notes demanding roughly $500 USD in Bitcoin, confirming the assault sample stays lively and automatic.
The resurgence was additional highlighted by penetration testing that exposed two compromised MongoDB cases at a small-to-medium-sized enterprise, each containing ransom notes.
This discovery prompted a deeper investigation into the present menace panorama, uncovering proof that insecure deployment practices persist throughout tutorials, container photos, and infrastructure templates.
The MongoDB ransomware assault exploits a easy but vital vulnerability: internet-exposed databases deployed with out authentication.
Automated scanning instruments establish MongoDB companies listening on port 27017 that settle for connections from any IP handle. As soon as found, attackers execute a simple four-step course of.
First, menace actors find susceptible MongoDB cases by mass web scanning. Second, they export or copy database contents to their very own programs.
Third, all collections and databases on the sufferer server are fully wiped. Lastly, attackers insert a brand new assortment containing a ransom notice demanding cost in Bitcoin inside 48 hours, threatening everlasting knowledge loss if the sufferer fails to conform.
Safety consultants strongly advise in opposition to paying ransoms, as victims who complied incessantly reported receiving nothing in return.
In lots of instances, attackers by no means really retained copies of the stolen knowledge, making restoration unattainable no matter cost.
Huge Publicity Revealed By Web Scanning
Evaluation utilizing Shodan, an internet-connected gadget search engine, recognized over 200,000 publicly discoverable MongoDB servers.
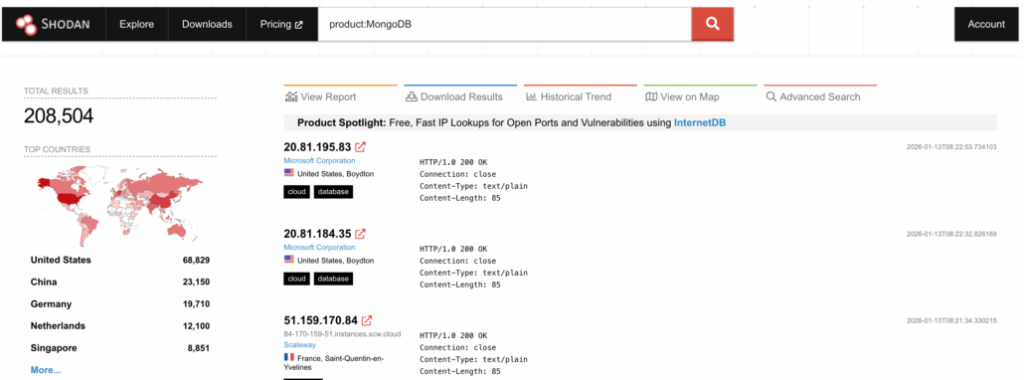
Of those, greater than 100,000 cases disclosed operational data, whereas 3,100 servers have been totally uncovered with out entry restrictions or authentication necessities.
| Metric | Rely | Proportion |
|---|---|---|
| Complete MongoDB servers found | 200,000+ | – |
| Servers with operational data | 100,000+ | – |
| Totally uncovered cases (no authentication) | 3,100 | 100% |
| Compromised cases (wiped with ransom) | 1,416 | 45.6% |
| Servers with not less than one vulnerability | 95,000 | 46.3% |
Among the many 3,100 totally uncovered servers, 1,416 cases (45.6%) had already been compromised, with databases wiped and changed by ransom notes. Almost all incidents demanded roughly $500 USD in Bitcoin.
Considerably, solely 5 distinct Bitcoin wallets have been noticed throughout all assaults, with a single pockets handle (bc1qe2l4ffmsqfdu43d7n76hp2ksmhclt5g9krx3du) current in over 98% of instances, strongly suggesting a single dominant menace actor.
The discrepancy between uncovered servers and compromised cases raises questions in regards to the remaining 1,684 programs.
Some might symbolize check environments or programs which have been taken offline. In distinction, others might have paid the ransom, leaving no seen proof of compromise.
Even when solely a portion is paid, the marketing campaign’s income might vary from zero to roughly $842,000 USD.
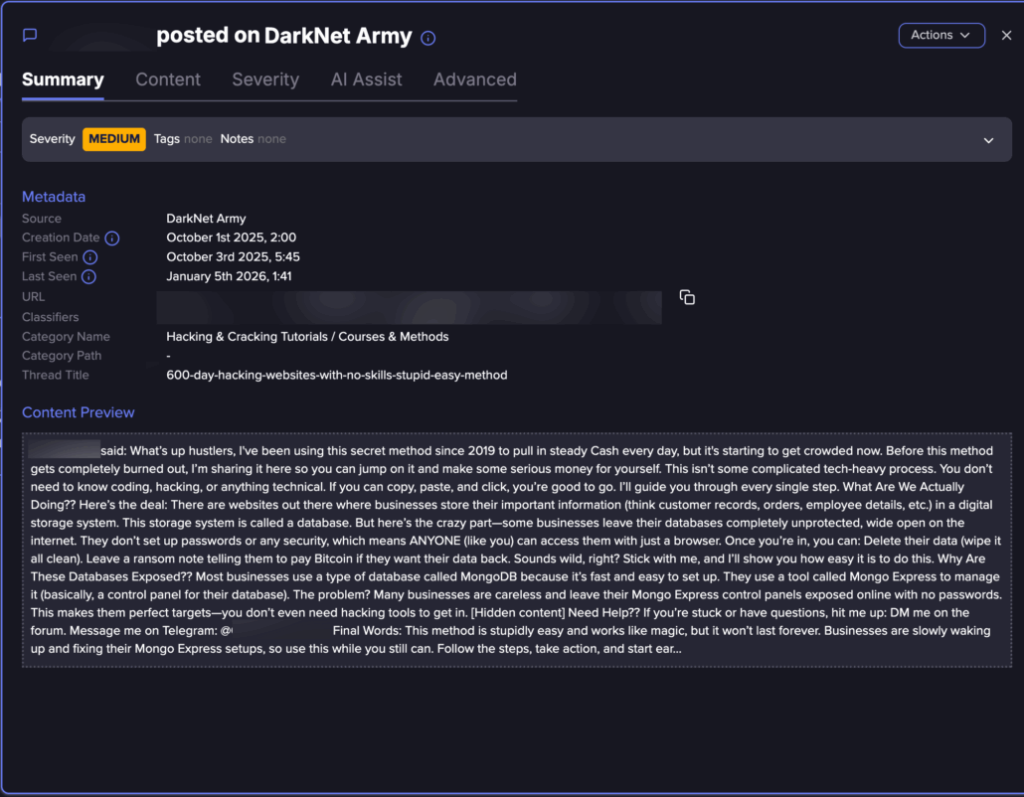
Menace intelligence gathering revealed lively MongoDB ransom tutorials circulating on darkish internet boards and Tor web sites.
One tutorial found in 2025 explicitly marketed the assault technique as requiring no technical experience, claiming attackers might “pull in regular money day-after-day” by focusing on uncovered databases.
The tutorial supplied step-by-step directions describing how companies typically go away MongoDB and its administration interface, Mongo Specific, uncovered on-line with out passwords.
The information emphasised that the strategy required solely fundamental laptop abilities “should you can copy, paste, and click on, you’re good to go” reducing the barrier to entry for aspiring cybercriminals.
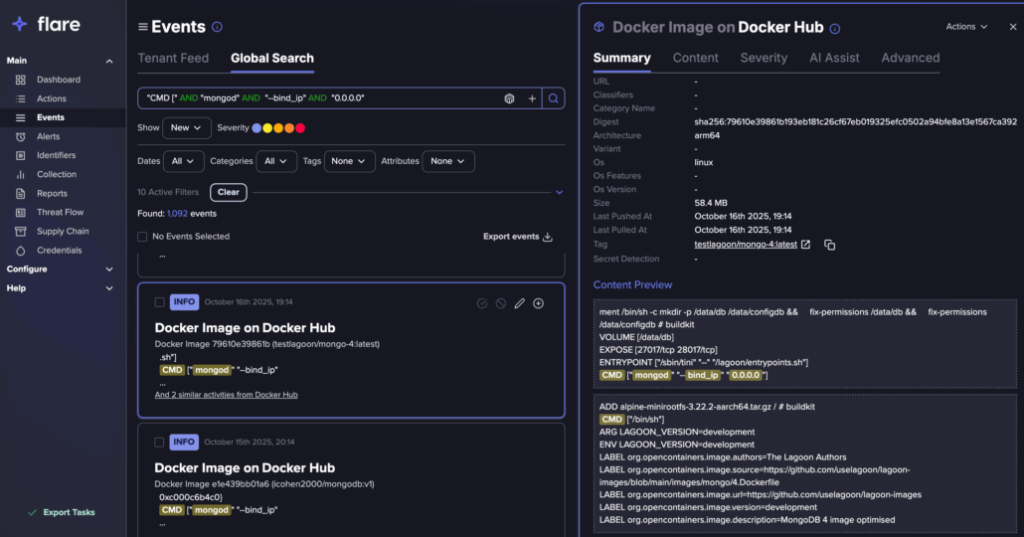
Safety researchers from Flare additionally analysed Docker Hub and GitHub repositories, figuring out 763 container photos containing insecure MongoDB configurations that bind the database to all community interfaces (0.0.0.0) with out authentication.
These photos spanned 30 distinct namespaces over three months, with two widely-used tasks every exceeding 15,000 pulls.
This distribution mechanism allows insecure configurations to propagate quickly by copy-paste deployment practices.

Moreover, searches for uncovered MongoDB credentials yielded 17,909 potential outcomes, of which roughly half have been validated as practical credentials that attackers might exploit.
These credentials appeared throughout coding repositories (GitHub, Docker Hub), darkish internet boards, paste websites, and breach databases.
MITRE ATT&CK Framework Mapping
The MongoDB ransom marketing campaign demonstrates an entire assault lifecycle aligned with the MITRE ATT&CK framework, regardless of its technical simplicity.
| Tactic | Method ID | Method Title | Description |
|---|---|---|---|
| Preliminary Entry | T1190 | Exploit Public-Going through Utility | Connect with uncovered MongoDB with out authentication |
| Discovery | T1046 | Community Service Discovery | Scan IP ranges for open MongoDB port 27017 |
| Discovery | T1087 | Account Discovery | Enumerate databases and collections |
| Assortment | T1213 | Information from Data Repositories | Dump databases to evaluate worth |
| Affect | T1485 | Information Destruction | Drop/wipe collections and databases |
| Affect | T1489 | Service Disruption | Disrupt enterprise operations |
| Affect | T1657 | Extortion | Insert ransom notice demanding Bitcoin cost |
Notably, the assault requires no privilege escalation, lateral motion, or malware deployment.
Attackers function fully inside permissions granted by insecure default configurations, making detection difficult and favoring reactive responses over preventative measures.
Comply with us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most popular Supply in Google.

