GrayCharlie is abusing compromised WordPress websites to silently load malicious JavaScript that pushes NetSupport RAT, usually adopted by Stealc and SectopRAT, by way of faux browser updates and ClickFix lures.
Insikt Group tracks GrayCharlie as a financially motivated menace actor overlapping with SmartApeSG, energetic since mid‑2023, and specializing in turning legit WordPress websites into malware-delivery factors.
The actor injects hyperlinks to externally hosted JavaScript into compromised pages, which then redirect guests to faux browser-update pages or ClickFix-style social engineering flows that finally ship the NetSupport RAT.
As soon as NetSupport is put in and linked to attacker‑managed C2 servers, GrayCharlie operators achieve distant entry for surveillance, file operations, and comply with‑on payload supply, together with infostealer Stealc and distant entry malware SectopRAT.
Insikt Group stories that GrayCharlie operates a large, layered infrastructure footprint, closely focused on suppliers MivoCloud and HZ Internet hosting Ltd.
This contains devoted NetSupport RAT C2 servers, staging servers internet hosting the malicious JavaScript templates, and better‑tier techniques used to manage campaigns, usually accessed by way of proxy providers.
The group’s exercise stays constant throughout campaigns, with recurring use of the identical an infection chains, license keys, and TLS certificates patterns on its C2 infrastructure.
Pretend Updates, ClickFix, and Regulation Agency
Initially, GrayCharlie relied totally on faux browser replace overlays, which seem tailor-made to Chrome, Edge, or Firefox and immediate customers to obtain a supposed replace bundle that’s really a JavaScript pushed NetSupport installer.
The IP addresses related to the staging infrastructure are linked to web sites impersonating “Wiser College” a fictional entity used to display Wiser, a free Bootstrap HTML5 schooling.
The loader script launches by way of WScript, phases PowerShell, downloads and extracts the NetSupport consumer into places resembling %AppData%, provides Registry Run keys for persistence, after which beaconing to GrayCharlie‑managed C2 servers.
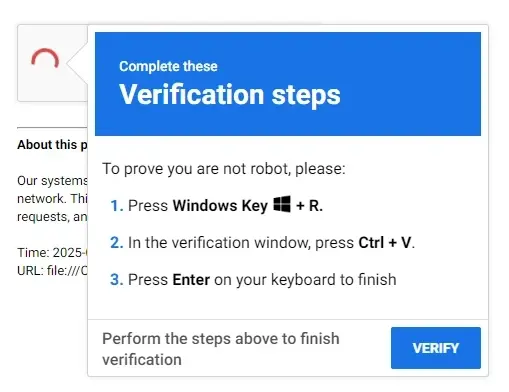
In 2025, the actor expanded to a ClickFix move, the place compromised WordPress pages show a faux CAPTCHA that copies a PowerShell‑primarily based command to the clipboard and instructs customers to execute it utilizing the Home windows Run dialog, once more leading to NetSupport RAT set up and persistence.
Most sufferer websites seem opportunistically compromised throughout many sectors, however Insikt Group additionally highlights a notable cluster of US legislation agency WordPress websites that started loading malicious JavaScript from GrayCharlie‑managed infrastructure round November 2025.
Proof suggests these legislation agency websites might have been compromised by way of a provide‑chain vector involving a shared IT or advertising supplier, with SMB Crew cited as a probable avenue on account of its branding and shared credentials surfacing across the time the malicious infrastructure grew to become energetic.

Whereas GrayCharlie’s final targets stay unclear, present telemetry factors to information theft, monetary achieve, and probably promoting or sharing entry with different menace actors, underlining the chance to authorized and different excessive‑worth targets.
Mitigations
Insikt Group advises defenders to aggressively block IP addresses and domains tied to NetSupport RAT, Stealc, SectopRAT, and different instruments utilized in GrayCharlie operations, and to deal with site visitors to identified‑compromised WordPress websites as excessive‑danger till remediated.
The web page presents a faux CAPTCHA that quietly copies a malicious command to the person’s clipboard and instructs them to stick it into the Home windows Run dialog (Win+R).
Safety groups ought to deploy up to date YARA, Snort, and Sigma guidelines to detect NetSupport parts, ClickFix‑model instructions, and GrayCharlie’s JavaScript and PowerShell loader patterns, together with in historic logs.
Extra beneficial controls embrace tightening e mail and net filtering, monitoring for suspicious information exfiltration to identified malicious infrastructure, and constantly ingesting new GrayCharlie menace intelligence sources to maintain detection and blocking insurance policies present.
Observe us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most popular Supply in Google.

