Cybersecurity researchers at Varonis Risk Labs have recognized a brand new platform named 1Campaign, designed particularly to assist hackers and scammers trick Google’s safety methods, or no less than try to take action.
This service permits criminals to run fraudulent commercials that keep on-line for for much longer than typical by hiding their true intent from security checkers. The platform has been lively for over three years, managed by a developer referred to as DuppyMeister, who even gives devoted assist desk help for customers.
How It Works
The principle characteristic of 1Campaign is a method referred to as cloaking. This entails exhibiting two totally different variations of an internet site. When a Google reviewer or a safety bot checks the hyperlink, they see a superbly protected white web page. Nevertheless, when an everyday individual clicks the identical advert, they’re redirected to a harmful website designed to steal cryptocurrency or login particulars.
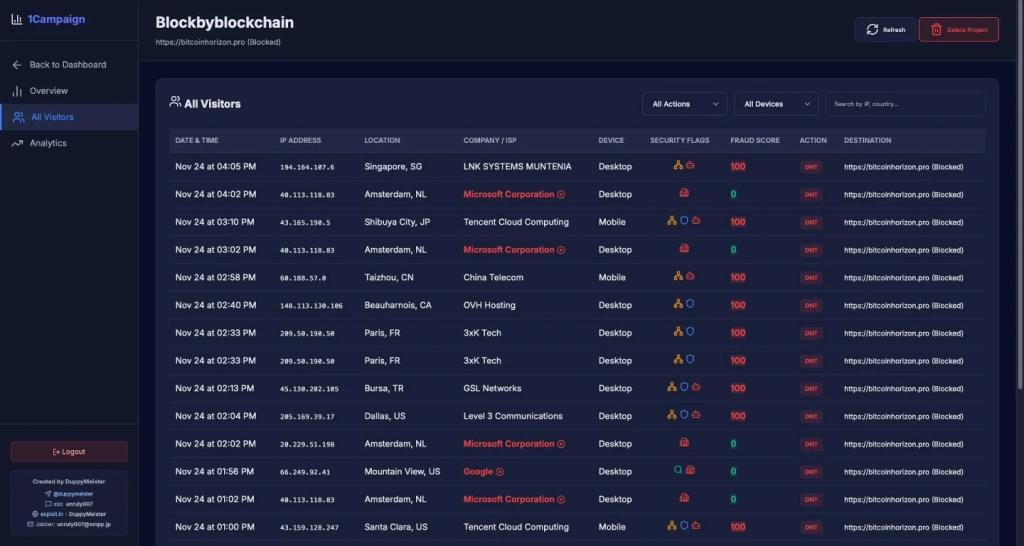
Additional investigation by Varonis’ risk analysts revealed that the software is extremely efficient at recognizing pretend guests. It makes use of a fraud rating from 0 to 100 to rank each one who clicks, and if the system detects a customer from a tech firm like Microsoft, Google, or Tencent, or somebody utilizing a VPN, it mechanically blocks them. It’s value noting that in a single analysed marketing campaign referred to as Blockbyblockchain, which focused the positioning bitcoinhorizon.professional, the system blocked 99.4% of 1,676 guests, permitting solely 10 actual potential victims by.
Focused Assaults and World Attain
In keeping with researchers, 1Campaign is a part of a worrying rise in user-friendly hacking toolkits. Whereas different toolkits like Spiderman or FishXProxy give attention to focusing on banks or avoiding takedowns, 1Campaign is exclusive as a result of it particularly focuses on abusing Google Advertisements. This technique, referred to as malvertising, permits attackers to purchase professional advert house to unfold malware or pretend software program.
The analysis signifies that these toolkits make it simpler than ever for individuals with out technical expertise to launch high-level scams. 1Campaign even features a particular launcher that helps attackers bypass strict guidelines and create adverts utilizing any textual content or phrases, making it simple to impersonate well-known manufacturers. As Daniel Kelley, a researcher concerned within the examine, defined within the weblog submit shared with Hackread.com:
“1Campaign stands out as a result of it takes many tried-and-true hacker instruments and methods, packages them collectively, and goals them immediately on the greatest on-line advertiser on the earth.”
Researchers additionally highlighted the worldwide scale of those operations, with visitors being tracked throughout the UK, the US, the Netherlands, China, and Germany. By the point a rip-off is manually reported and brought down, the attackers have usually already prompted vital monetary harm.
To remain protected, it’s best to deal with promoted search outcomes with warning and at all times double-check the net deal with earlier than getting into any private knowledge.

