Menace actors are more and more weaponizing trusted administrative software program to bypass safety defenses.
By exploiting reputable software program, cybercriminals achieve persistent, hands-on-keyboard (HOK) entry whereas hiding inside regular community exercise.
Preliminary Entry and Assault Strategies
RMM compromises sometimes start with focused social engineering and phishing campaigns.
Attackers trick staff into downloading a malicious RMM agent disguised as routine enterprise information, granting the attacker fast entry with out triggering endpoint detection and response (EDR) alerts.
For the reason that RMM binary is a legitimate administrative instrument, it doesn’t seem malicious to conventional safety programs searching for identified unhealthy signatures like ransomware or distant entry trojans.
In response to the Huntress 2026 Cyber Menace Report, analyzed by Beth Robinson, the abuse of Distant Monitoring and Administration (RMM) instruments surged by an alarming 277% in 2025.
As soon as inside, adversaries use these trusted instruments to maneuver laterally, automate duties, and deploy harmful payloads somewhat than writing customized malware from scratch.
When attackers compromise an RMM answer managed by a Managed Service Supplier (MSP), they’ll instantly entry a number of downstream prospects in an enormous provide chain assault.
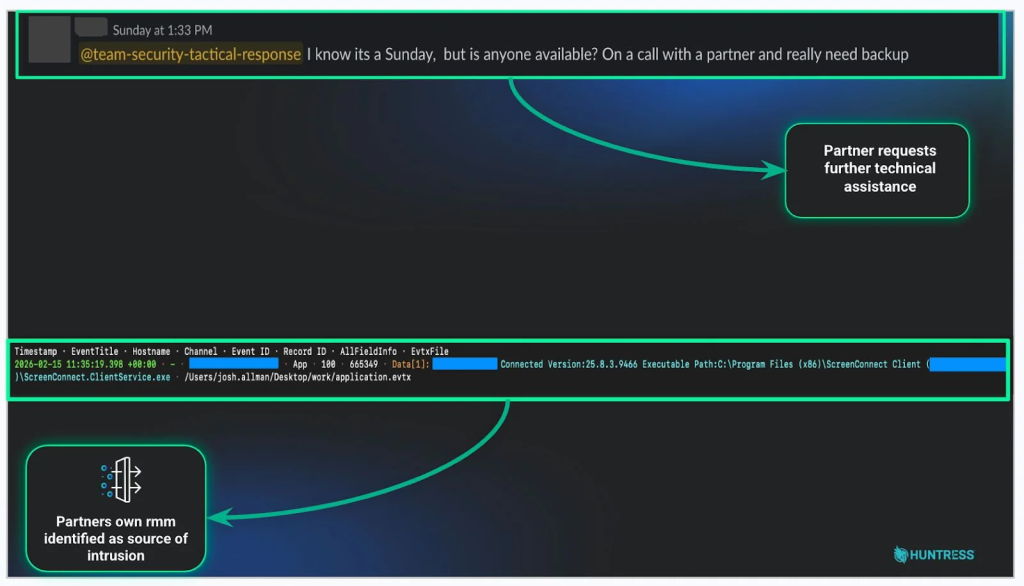
The Huntress report notes that over 50% of incidents involving suspicious Atera RMM exercise are immediately linked to ransomware, which might unfold and execute in as little as an hour.
In 2025, attackers relied closely on particular phishing lures to deploy these brokers:
- E-signature requests (14.2%): Disguised doc hyperlinks seamlessly set up an RMM agent within the background.
- Bill notifications (7.8%): Pretend billing paperwork immediate the person to authorize malicious downloads.
- Voicemail notifications (7.5%): Audio alerts redirect victims to attacker-controlled payloads.
- File shares (6.8%): Bogus shared drive hyperlinks grant fast atmosphere entry upon clicking.
Protection and Mitigation Methods
To fight this rising menace, organizations should shift from merely trusting permitted software program to actively verifying person habits.
Safety groups ought to outline a strict baseline of regular IT operations to determine anomalies, corresponding to surprising script execution at uncommon hours.
If a instrument is permitted however behaves irregularly, it warrants fast investigation earlier than it escalates into information exfiltration.
A proactive protection requires steady fingerprinting of the digital atmosphere. IT directors should observe permitted RMM executable hashes, monitor particular connection URLs, and deal with any unverified distant entry instrument as a possible intrusion.
By sustaining a strict stock and specific allowlist, safety groups can quickly block unapproved RMM variants and connections to unknown servers.
Lastly, the human ingredient stays a important protection layer in opposition to these misleading ways. Implementing complete Safety Consciousness Coaching (SAT) teaches employees to identify sneaky phishing and social engineering makes an attempt earlier than granting entry.
Fostering a “see one thing, say one thing” tradition ensures that suspicious habits is reported and investigated instantly, closing the damaging hole between preliminary an infection and detection.
Comply with us on Google Information, LinkedIn, and X to Get On the spot Updates and Set GBH as a Most well-liked Supply in Google.

