Since its normal availability in 2024, Amazon Q Enterprise (Amazon Q) has enabled unbiased software program distributors (ISVs) to reinforce their Software program as a Service (SaaS) options by way of safe entry to clients’ enterprise information by turning into Amazon Q Enterprise information accessor. To search out out extra on information accessor, see this web page. The info accessor now helps trusted id propagation. With trusted token issuer (TTI) authorization assist, ISVs as information accessor can combine with Amazon Q index whereas sustaining enterprise-grade safety requirements for his or her software-as-a-service (SaaS) options.
Previous to TTI assist, information accessors wanted to implement authorization code movement with AWS IAM Identification Heart integration when accessing the Amazon Q index. With TTI assist for information accessors, ISVs can now use their very own OpenID Supplier to authenticate enterprise customers, assuaging the necessity for double authentication whereas sustaining safety requirements.
On this weblog put up, we present you tips on how to implement TTI authorization for information accessors, evaluate authentication choices, and supply step-by-step steerage for each ISVs and enterprises.
Conditions
Earlier than you start, be sure to have the next necessities:
- An AWS account with administrator entry
- Entry to Amazon Q Enterprise
- For ISVs:
- An OpenID Join (OIDC) suitable authorization server
- For enterprises:
- Amazon Q Enterprise administrator entry
- Permission to create trusted token issuers
Resolution Overview
This answer demonstrates tips on how to implement TTI authentication for Amazon Q Enterprise information accessors. The next diagram illustrates the general movement between totally different assets, from ISV turning into a knowledge accessor, buyer enabling ISV information accessor, to ISV accessing buyer’s Amazon Q index:
Understanding Trusted Token Issuer Authentication
Trusted Token Issuer represents a complicated id integration functionality for Amazon Q. At its core, TTI is a token trade API that propagates id data into IAM position classes, enabling AWS providers to make authorization choices primarily based on the precise finish person’s id and group memberships. This mechanism permits AWS providers to use authorization and safety controls primarily based on the authenticated person context. The TTI assist simplifies the id integration course of whereas sustaining sturdy safety requirements, making it attainable for organizations to make sure that entry to Amazon Q respects user-level permissions and group memberships. This allows fine-grained entry management and maintains correct safety governance inside Amazon Q implementations.
Trusted Token Issuer authentication simplifies the id integration course of for Amazon Q by enabling the propagation of person id data into AWS IAM position classes. Every token trade permits AWS providers to make authorization choices primarily based on the authenticated person’s id and group memberships. The TTI assist streamlines the combination course of whereas sustaining sturdy safety requirements, enabling organizations to implement acceptable entry controls inside their Amazon Q implementations.
Understanding Information Accessors
A knowledge accessor is an ISV that has registered with AWS and is allowed to make use of their clients’ Amazon Q index for the ISV’s Giant Language Mannequin (LLM) answer. The method begins with ISV registration, the place they supply configuration data together with show identify, enterprise brand, and OpenID Join (OIDC) configuration particulars for TTI assist.
Throughout ISV registration, suppliers should specify their tenantId configuration – a novel identifier for his or her software tenant. This identifier could be identified by totally different names in numerous functions (comparable to Workspace ID in Slack or Area ID in Asana) and is required for correct buyer isolation in multi-tenant environments.
Amazon Q clients then add the ISV as a knowledge accessor to their atmosphere, granting entry to their Amazon Q index primarily based on particular permissions and information supply choices. As soon as licensed, the ISV can question the purchasers’ index by way of API requests utilizing their TTI authentication movement, making a safe and managed pathway for accessing buyer information.
Implementing TTI Authentication for Amazon Q index Entry
This part explains tips on how to implement TTI authentication for accessing the Amazon Q index. The implementation entails preliminary setup by the client and subsequent authentication movement carried out by information accessors for person entry.
TTI offers capabilities that allow identity-enhanced IAM position classes by way of Trusted Identification Propagation (TIP), permitting AWS providers to make authorization choices primarily based on authenticated person identities and group memberships. Right here’s the way it works:
To allow information accessor entry to a buyer’s Amazon Q index by way of TTI, clients should carry out an preliminary one-time setup by including a knowledge accessor on Amazon Q Enterprise software. Throughout setup, a TTI with the information accessor’s id supplier data is created within the buyer’s AWS IAM Identification Heart, permitting the information accessor’s id supplier to authenticate entry to the client’s Amazon Q index.
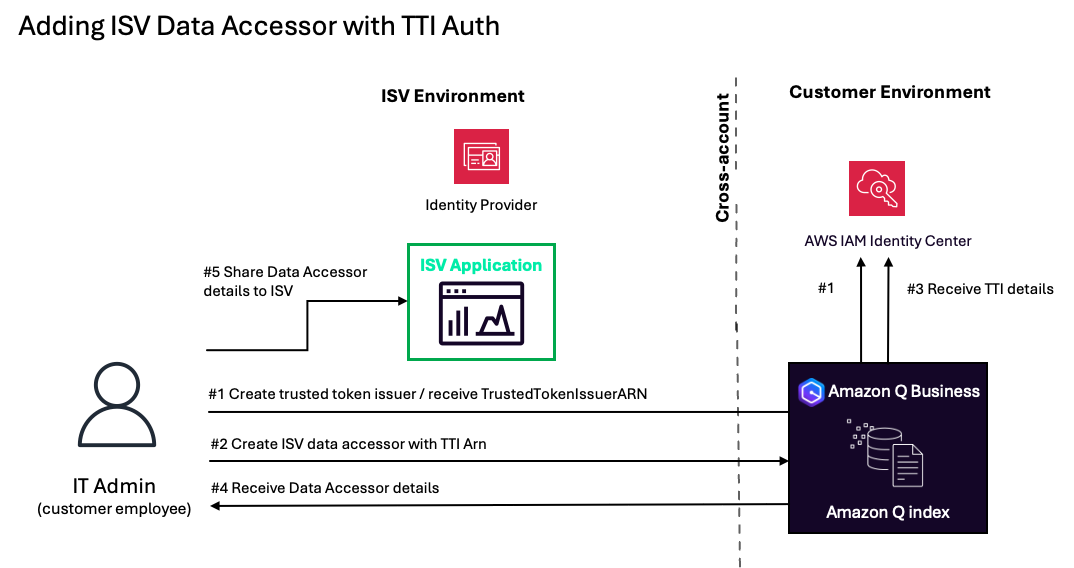
The method to arrange an ISV information accessor with TTI authentication consists of the next steps:
- The shopper’s IT administrator accesses their Amazon Q Enterprise software and creates a trusted token issuer with the ISV’s OAuth data. This returns a TrustedTokenIssuer (TTI) Amazon Useful resource Title (ARN).
- The IT administrator creates an ISV information accessor with the TTI ARN acquired in Step 1.
- Amazon Q Enterprise confirms the supplied TTI ARN with AWS IAM Identification Heart and creates a knowledge accessor software.
- Upon profitable creation of the ISV information accessor, the IT administrator receives information accessor particulars to share with the ISV.
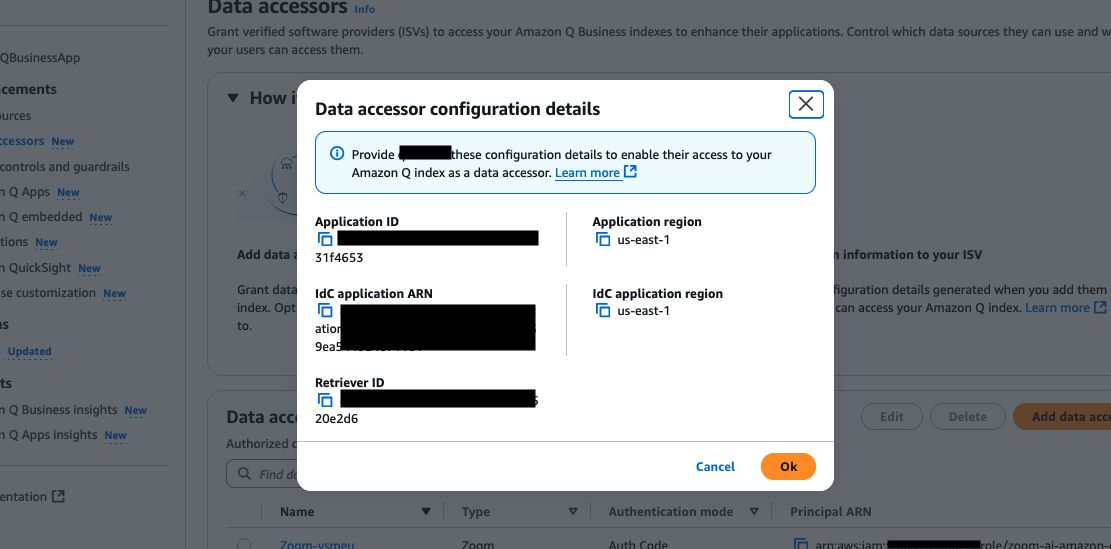
- The IT administrator offers these particulars to the ISV software.
As soon as the information accessor setup is full within the buyer’s Amazon Q atmosphere, customers can entry the Amazon Q index by way of the ISV software by authenticating solely in opposition to the information accessor’s id supplier.
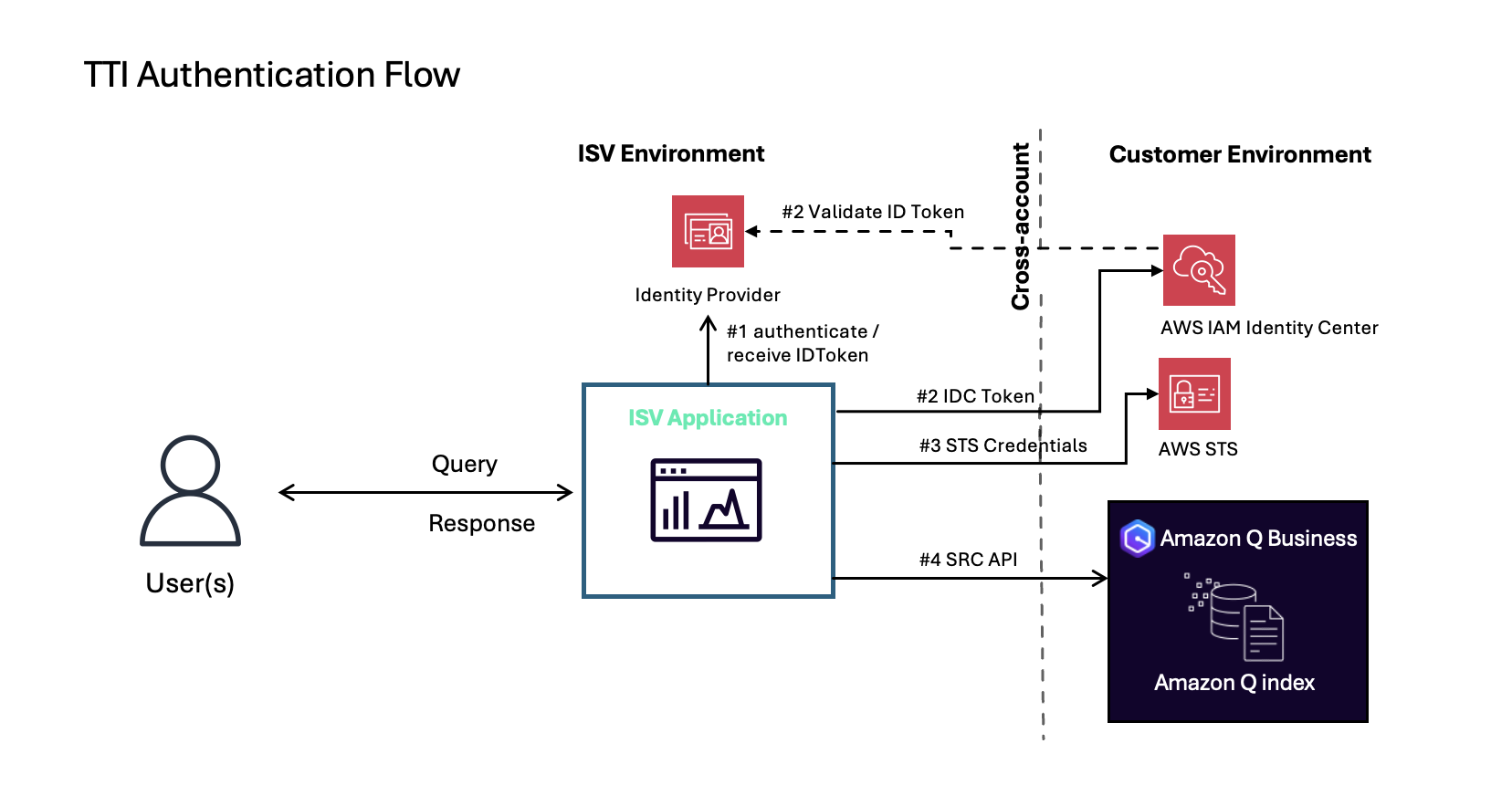
The authentication movement proceeds as follows:
- A person authenticates in opposition to the information accessor’s id supplier by way of the ISV software. The ISV software receives an ID token for that person, generated from the ISV’s id supplier with the identical consumer ID registered on their information accessor.
- The ISV software wants to make use of the AWS Identification and Entry Administration (IAM) position that they created throughout the information accessor onboarding course of by calling AssumeRole API, then make CreateTokenWithIAM API request to the client’s AWS IAM Identification Heart with the ID token. AWS IAM Identification Heart validates the ID token with the ISV’s id supplier and returns an IAM Identification Heart token.
- The ISV software requests an AssumeRole API with: IAM Identification Heart token, extracted id context, and tenantId. The tenantId is a safety management collectively established between the ISV and their buyer, with the client sustaining management over the way it’s used of their belief relationships. This mixture facilitates safe entry to the proper buyer atmosphere.
- The ISV software calls the SearchRelevantContent API with the session credentials and receives related content material from the client’s Amazon Q index.
When implementing Amazon Q integration, ISVs want to think about two approaches, every with its personal advantages and concerns:
| Trusted Token Issuer | Authorization Code | |
| Benefits | Single authentication on the ISV system | Enhanced safety by way of necessary person initiation for every session |
| Permits backend-only entry to SearchRelevantContent API with out person interplay | ||
| Concerns | Some enterprises could want authentication flows that require express person consent for every session, offering extra management over API entry timing and period | Requires double authentication on the ISV system |
| Requires ISVs to host and keep OpenID Supplier |
TTI excels in offering a seamless person expertise by way of single authentication on the ISV system and permits backend-only implementations for SearchRelevantContent API entry with out requiring direct person interplay. Nonetheless, this strategy requires ISVs to take care of their very own OIDC authorization server, which can current implementation challenges for some organizations. Moreover, some enterprises may need issues about ISVs having persistent capability to make API requests on behalf of their customers with out express per-session authorization.
Subsequent Steps
For ISVs: Turning into a Information Accessor with TTI Authentication
Getting began on Amazon Q information accessor registration course of with TTI authentication is easy. If you have already got an OIDC suitable authorization server on your software’s authentication, you’re a lot of the means there.
To start the registration course of, you’ll want to offer the next data:
- Show identify and enterprise brand that can be displayed on AWS Administration Console
- OIDC configuration particulars (OIDC ClientId and discovery endpoint URL)
- TenantID configuration particulars that specify how your software identifies totally different buyer environments
For particulars, see Data to be supplied to the Amazon Q Enterprise crew.
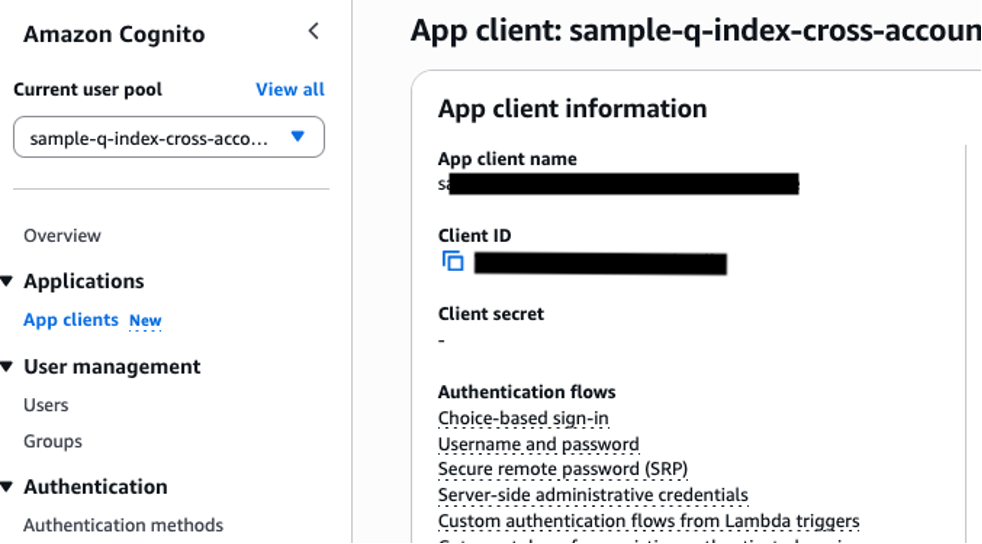
For ISVs utilizing Amazon Cognito as their OIDC authorization server, right here’s tips on how to retrieve the required OIDC configuration particulars:
- To get the OIDC ClientId:- Navigate to the Amazon Cognito console- Choose your Consumer Pool- Go to “Functions” > “App shoppers”- The ClientId is listed below “Consumer ID” on your app consumer
 To get the invention endpoint URL:- The URL follows this format:
To get the invention endpoint URL:- The URL follows this format:https://cognito-idp.{area}.amazonaws.com/{userPoolId}/.well-known/openid-configuration– Change {area} along with your AWS area (e.g., us-east-1)- Change {userPoolId} along with your Cognito Consumer Pool IDFor instance, in case your Consumer Pool is in us-east-1 with ID ‘us-east-1_abcd1234’, your discovery endpoint URL can be:https://cognito-idp.us-east-1.amazonaws.com/us-east-1_abcd1234/.well-known/openid-configuration
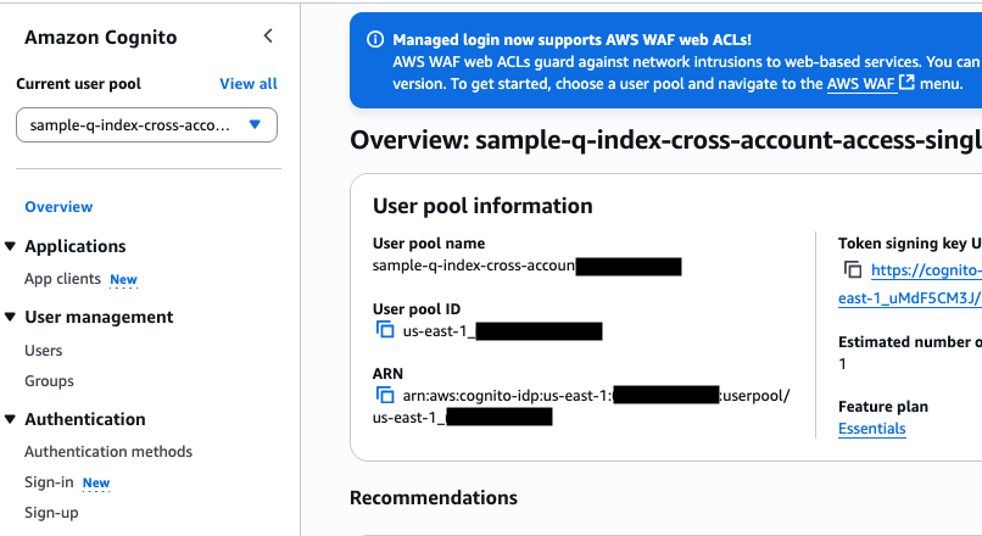
Observe: Whereas this instance makes use of Amazon Cognito, the method will range relying in your OIDC supplier. Frequent suppliers like Auth0, Okta, or customized implementations could have their very own strategies for accessing these configuration particulars.
As soon as registered, you’ll be able to improve your generative AI software with the highly effective capabilities of Amazon Q, permitting your clients to entry their enterprise information base by way of your acquainted interface. AWS offers complete documentation and assist that can assist you implement the authentication movement and API integration effectively.
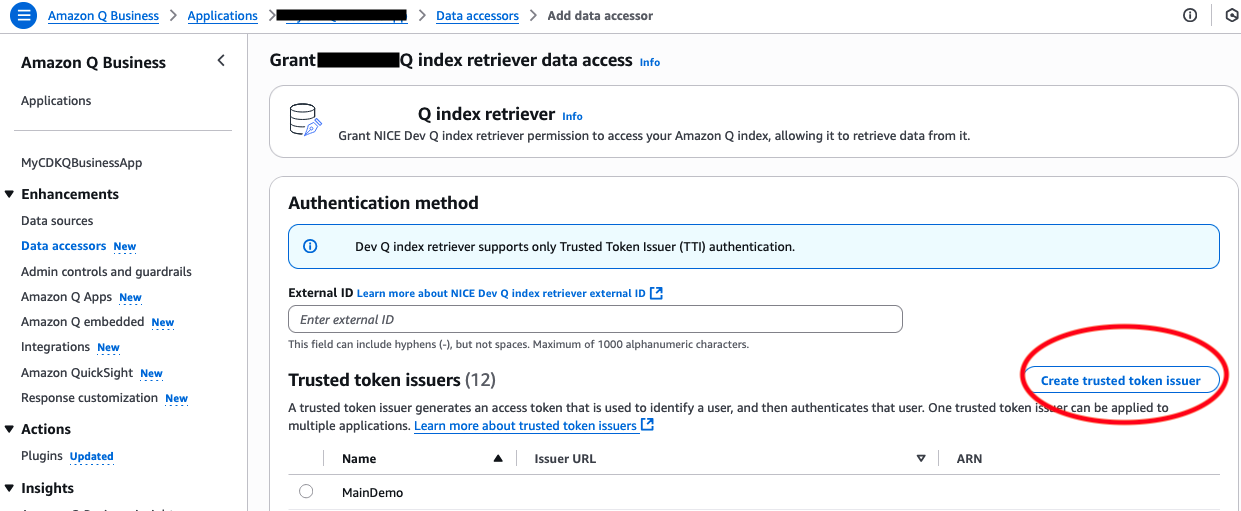
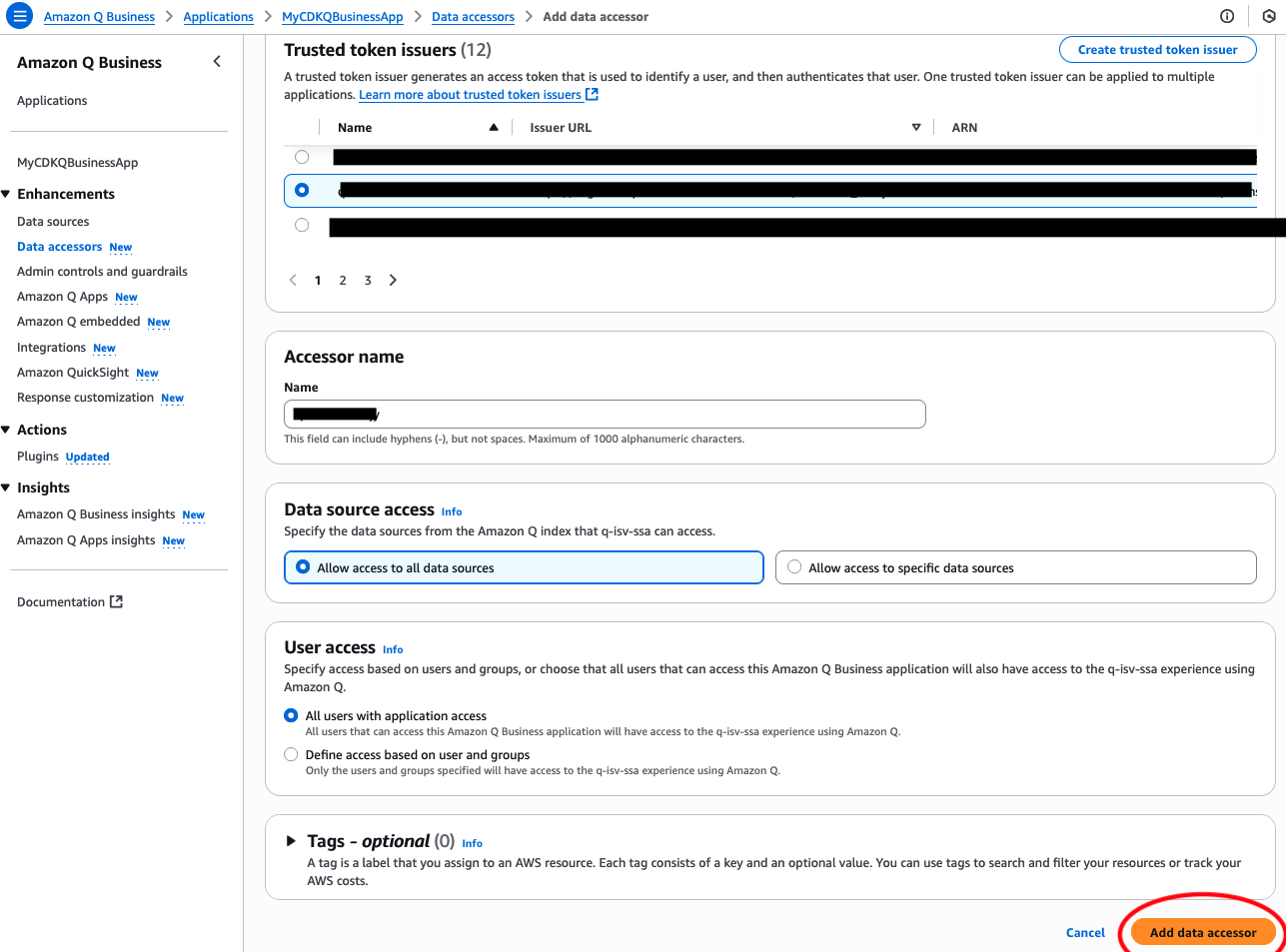
For Enterprises: Enabling TTI-authenticated Information Accessor
To allow a TTI-authenticated information accessor, your IT administrator wants to finish the next steps within the Amazon Q console:
- Create a trusted token issuer utilizing the ISV’s OAuth data
- Arrange the information accessor with the generated TTI ARN
- Configure acceptable information supply entry permissions
This streamlined setup permits your customers to entry Amazon Q index by way of the ISV’s software utilizing their present ISV software credentials, assuaging the necessity for a number of logins whereas sustaining safety controls over your enterprise information.
Each ISVs and enterprises profit from AWS’s complete documentation and assist all through the implementation course of, facilitating a easy and safe integration expertise.
Clear up assets
To keep away from unused assets, observe these steps when you now not want the information accessor:
- Delete the information accessor:
- On the Amazon Q Enterprise console, select Information accessors within the navigation pane
- Choose your information accessor and select Delete.
- Delete the TTI:
- On the IAM Identification Heart console, select Trusted Token Issuers within the navigation pane.
- Choose the related issuer and select Delete.
Conclusion
The introduction of Trusted Token Issuer (TTI) authentication for Amazon Q information accessors marks a major development in how ISVs combine with Amazon Q Enterprise. By enabling information accessors to make use of their present OIDC infrastructure, we’ve alleviated the necessity for double authentication whereas sustaining enterprise-grade safety requirements by way of TTI’s sturdy tenant isolation mechanisms and safe multi-tenant entry controls, ensuring every buyer’s information stays protected inside their devoted atmosphere. This streamlined strategy not solely enhances the end-user expertise but in addition simplifies the combination course of for ISVs constructing generative AI options.
On this put up, we confirmed tips on how to implement TTI authentication for Amazon Q information accessors. We coated the setup course of for each ISVs and enterprises and demonstrated how TTI authentication simplifies the person expertise whereas sustaining safety requirements.
To be taught extra about Amazon Q Enterprise and information accessor integration, seek advice from Share your enterprise information with information accessors utilizing Amazon Q index and Data to be supplied to the Amazon Q Enterprise crew. You may also contact your AWS account crew for customized steerage. Go to the Amazon Q Enterprise console to start utilizing these enhanced authentication capabilities as we speak.
Concerning the Authors
 Takeshi Kobayashi is a Senior AI/ML Options Architect inside the Amazon Q Enterprise crew, chargeable for creating superior AI/ML options for enterprise clients. With over 14 years of expertise at Amazon in AWS, AI/ML, and expertise, Takeshi is devoted to leveraging generative AI and AWS providers to construct modern options that deal with buyer wants. Based mostly in Seattle, WA, Takeshi is obsessed with pushing the boundaries of synthetic intelligence and machine studying applied sciences.
Takeshi Kobayashi is a Senior AI/ML Options Architect inside the Amazon Q Enterprise crew, chargeable for creating superior AI/ML options for enterprise clients. With over 14 years of expertise at Amazon in AWS, AI/ML, and expertise, Takeshi is devoted to leveraging generative AI and AWS providers to construct modern options that deal with buyer wants. Based mostly in Seattle, WA, Takeshi is obsessed with pushing the boundaries of synthetic intelligence and machine studying applied sciences.
 Siddhant Gupta is a Software program Improvement Supervisor on the Amazon Q crew primarily based in Seattle, WA. He’s driving innovation and improvement in cutting-edge AI-powered options.
Siddhant Gupta is a Software program Improvement Supervisor on the Amazon Q crew primarily based in Seattle, WA. He’s driving innovation and improvement in cutting-edge AI-powered options.
 Akhilesh Amara is a Software program Improvement Engineer on the Amazon Q crew primarily based in Seattle, WA. He’s contributing to the event and enhancement of clever and modern AI instruments.
Akhilesh Amara is a Software program Improvement Engineer on the Amazon Q crew primarily based in Seattle, WA. He’s contributing to the event and enhancement of clever and modern AI instruments.

