If a wierd e mail a few “fee element request” or “signed financial institution doc” lands in your inbox, your finest guess is to delete it instantly. A contemporary investigation by Fortinet’s FortiGuard Labs warns that scammers are utilizing these mundane enterprise themes to contaminate Home windows PCs with XWorm malware.
XWorm is a Distant Entry Trojan (RAT), which is a instrument able to giving a hacker full distant management of compromised Home windows techniques. Whereas the virus has been round since 2022, this newest model (XWorm 7.2) is a way more superior breed that surfaced on Telegram marketplaces as lately as late 2025 and early 2026.
How the Lure is Set
As we all know it, attackers depend on social engineering to make a faux e mail really feel pressing. Researchers discovered a number of e mail themes written in numerous languages. Largely these lure emails have been disguised as:
- Normal enterprise queries.
- Cost evaluations or buy orders.
- Signed financial institution paperwork for shipments.
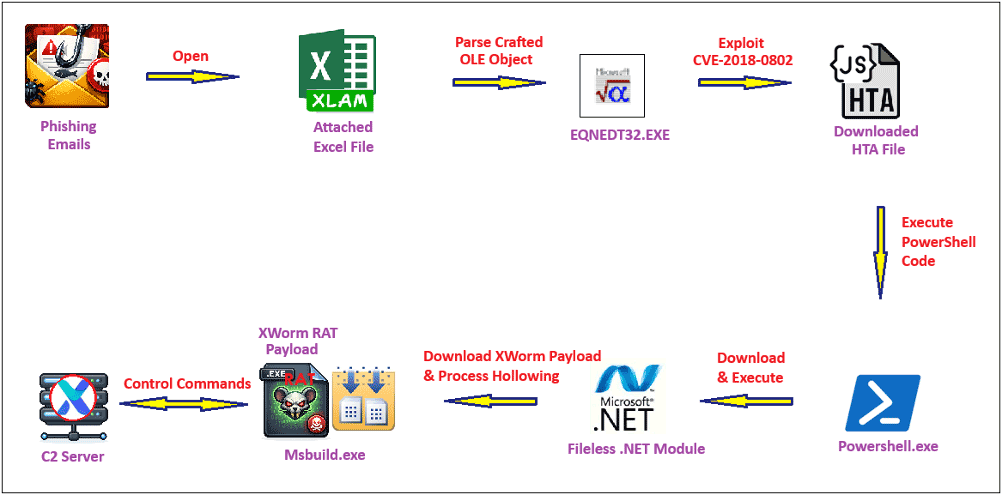
These emails normally include an Excel attachment; when opened, the file exploits an previous safety vulnerability tracked as CVE-2018-0802. This triggers a domino impact, operating a hidden script (an HTA file) which makes use of PowerShell to obtain what appears to be like like a traditional JPEG picture. Nevertheless, tucked inside that picture, between markers labelled BaseStart and BaseEnd, is the precise malware.
The Invisible An infection
Probably the most worrying a part of this marketing campaign is a trick referred to as course of hollowing. In line with researchers, the malware begins a respectable Home windows program (Msbuild.exe) however instantly pauses it and erases its inner code. It then replaces that code with the XWorm virus.
To your antivirus software program, it appears to be like like a trusted system instrument is operating, however in actuality, a hacker is now within the driving seat. The malware then connects to a management server at berlin101.com utilizing port 6000 and AES encryption to lock up and conceal any information it steals.
Why XWorm is Harmful
FortiGuard researchers clarify within the weblog publish that XWorm is very harmful as a result of it makes use of a modular setup, so hackers can add over 50 totally different plugins to broaden its attain. Presently, it will possibly steal all the things from Wi-Fi keys and passwords to browser cookies. It may well even spy on you by way of your webcam or log each single key you press.
Moreover, the malware even has built-in options for ransomware and launching DDoS assaults to crash web sites. Researchers famous that since XWorm “hides so nicely within the system registry,” it’s extremely tough to take away as soon as it takes maintain. The perfect defence stays conserving your software program up to date and staying cautious of sudden attachments.
Specialists Insights:
Sharing their ideas with Hackread.com, business specialists counsel that the hazard lies in how nicely these previous tips are put collectively.
Shane Barney, Chief Data Safety Officerat Keeper Safety, famous that whereas the strategies aren’t model new, they’re efficient. “This marketing campaign is hanging in its ordinariness. There’s no breakthrough approach right here,” Barney stated. “It’s a clear execution chain constructed from elements we’ve all seen earlier than. The sophistication isn’t within the novelty. It’s within the meeting.” He warned that as a result of XWorm is offered brazenly, “enterprise-grade intrusion functionality” is now out there to nearly anybody.
Jason Soroko, Senior Fellow at Sectigo, identified that the hackers are assured that “legacy Workplace exploit paths nonetheless convert at scale.” Soroko defined that the selection to cover inside Msbuild.exe is a deliberate transfer to “mix in” through the use of a respectable Home windows file. In line with Soroko, XWorm has change into so superior that merely calling it a “RAT” is perhaps an understatement. “AES-encrypted C2 packets and a broad plugin ecosystem push XWorm firmly right into a mature, modular platform class the place ‘RAT’ understates the chance,” he famous.