North Korea’s Crypto Theft Operations: The Function of Lazarus Group in State-Sponsored Monetary Warfare
Lazarus Group cyberattack on Bitrefill highlights how North Korean hackers exploit crypto platforms by way of credentials and human error for theft.
The newest Bitrefill cyberattack affords a revealing look into how state-sponsored cybercrime has advanced right into a strategic monetary weapon. The most recent improvement revolves across the risk actor Lazarus Group, a hacking collective broadly attributed to the DPRK (North Korea), whose operations have blurred the road between cyber espionage and financial warfare.
What makes this breach notable is not only the theft itself, however how methodically it displays the broader sample of Lazarus Group crypto assaults and the rising risk of North Korean hackers’ cryptocurrency operations. Bitrefill, a Sweden-based cryptocurrency present card platform, disclosed that attackers had infiltrated its methods on March 1, 2026.
The breach led to drained crypto wallets and unauthorized entry to roughly 18,500 buyer buy information.
A Breach That Began with a Laptop computer
The preliminary compromise didn’t depend on zero-day exploits or unique vulnerabilities. As an alternative, it adopted a sample that has grow to be virtually attribute of North Korean hackers’ cryptocurrency campaigns: exploiting human error.
In accordance with Bitrefill’s inside investigation, attackers gained entry by a compromised worker’s laptop computer. From there, they extracted a legacy credential, an missed however nonetheless legitimate key; that opened the door to a snapshot containing manufacturing secrets and techniques. This foothold allowed them to escalate privileges and transfer laterally throughout the corporate’s infrastructure.
This technique highlights a recurring reality in cybersecurity: attackers usually desire the best path. Within the case of the Lazarus Group, social engineering and credential abuse persistently outperform extra advanced technical exploits.
Contained in the Bitrefill Cyberattack
As soon as inside, the attackers began understanding the operational mannequin. Fairly than instantly exfiltrating giant datasets, they probed the surroundings fastidiously. Logs point out they executed a restricted variety of database queries, more likely to establish high-value belongings corresponding to cryptocurrency wallets and present card stock.
The breach was finally detected by anomalies in buying conduct. Suspicious transactions involving suppliers revealed that the attackers had been exploiting Bitrefill’s present card provide chain whereas concurrently draining funds from its sizzling wallets, cryptocurrency wallets linked to the web for lively transactions.
Bitrefill responded by taking its complete system offline, a transfer that, whereas disruptive, probably prevented additional losses. Given the corporate’s international footprint, spanning a number of suppliers, merchandise, and fee methods, this shutdown was removed from trivial.
Information Publicity: Restricted however Important
Though the attackers didn’t extract the complete database, they accessed round 18,500 buy information. These included e mail addresses, crypto fee addresses, and metadata corresponding to IP addresses.
For roughly 1,000 transactions, encrypted buyer names had been additionally in danger. Bitrefill acknowledged that if encryption keys had been compromised, this knowledge may doubtlessly be uncovered. The affected customers had been notified immediately.
Importantly, Bitrefill emphasised that buyer knowledge was not the first goal. The attackers’ conduct suggests a deal with monetary achieve somewhat than large-scale knowledge harvesting, a trademark of Lazarus Group crypto assaults.
Attribution to Lazarus Group and DPRK
Bitrefill attributed the assault to actors linked to the Lazarus Group, citing a number of indicators: malware similarities, reused IP addresses, e mail patterns, and blockchain tracing. These components intently match earlier campaigns related to each Lazarus and its financially motivated subgroup, Bluenoroff.
This attribution aligns with broader intelligence assessments. The DPRK has relied on cyber operations to generate income, significantly in response to worldwide sanctions. Cryptocurrency platforms have grow to be prime targets on account of their liquidity and relative anonymity.
In 2025 alone, blockchain evaluation companies estimated that North Korea-linked actors stole roughly $2.02 billion in cryptocurrency, accounting for a large portion of world crypto theft. This contains high-profile incidents such because the $1.5 billion Bybit change hack, additionally attributed to the Lazarus Group.
Cyble’s Monitoring of Lazarus Group and DPRK Cyber Operations
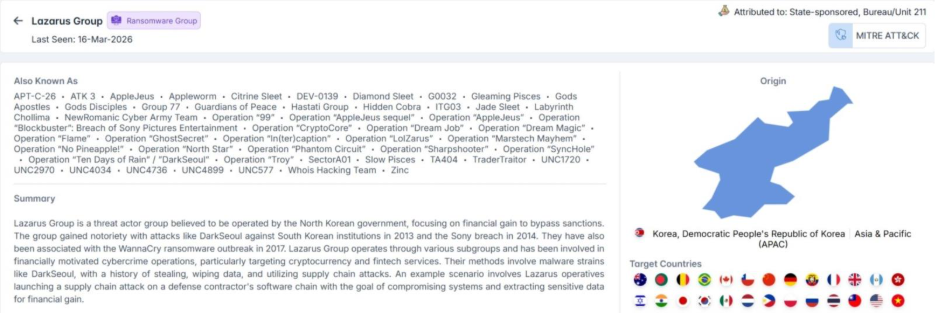
Cyble has lengthy tracked the Lazarus Group, figuring out it as probably the most persistent state-sponsored risk actors working underneath the umbrella of the DPRK (North Korea). Their evaluation frames the group not as a single unit, however as a distributed ecosystem of sub-clusters that perform financially motivated and espionage-driven operations.
The group has amassed a variety of aliases through the years, together with APT-C-26, Hidden Cobra, TraderTraitor, and Diamond Sleet. The geographic breadth of North Korean hackers’ cryptocurrency operations spanned nations corresponding to america, Japan, India, Germany, South Korea, and Australia, alongside sectors like banking, aerospace, healthcare, power, and telecommunications. Nonetheless, in recent times, the monetary and crypto sectors have grow to be disproportionately affected on account of their excessive liquidity and cross-border transaction flows.
From a tactical standpoint, Cyble’s mapping of Lazarus Group crypto assaults exhibits a constant reliance on multi-stage intrusion chains. These usually start with spearphishing campaigns, transfer into malware deployment, and finish with long-term persistence inside compromised networks.
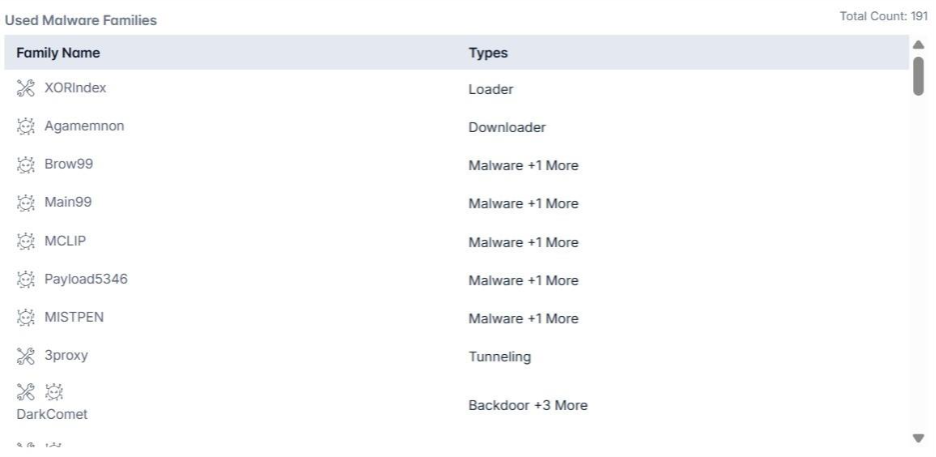
Instruments corresponding to credential stealers (for instance, Mimikatz), distant entry trojans, and customized loaders continuously seem throughout campaigns.
One in all the key observations is that Lazarus operations are not often purely opportunistic. As an alternative, they’re structured, iterative, and adaptive. The group refines its intrusion strategies primarily based on defensive responses noticed in earlier campaigns, usually reusing infrastructure parts corresponding to IP ranges, e mail patterns, and malware variants with slight modifications to keep away from detection.
Why Cryptocurrency Platforms Are Prime Targets
The Bitrefill cyberattack reinforces a bigger development: cryptocurrency ecosystems are uniquely susceptible to state-sponsored exploitation.
Not like conventional monetary methods, crypto platforms usually prioritize velocity and accessibility, generally on the expense of layered safety controls. Sizzling wallets, specifically, current a pretty goal as a result of they preserve instant liquidity.
Moreover, providers like Bitrefill introduce hybrid use circumstances, bridging crypto with real-world spending by present playing cards and digital purchases. This creates new assault surfaces, particularly inside provide chains that weren’t initially designed with adversarial risk fashions in thoughts.
The Playbook of Lazarus Group
The ways noticed on this breach are in line with the broader operational playbook of the Lazarus Group:
- Spearphishing and social engineering: Usually utilizing faux job affords or skilled outreach on platforms like LinkedIn
- Credential theft and reuse: Leveraging weak or outdated authentication practices
- Residing-off-the-land methods: Utilizing reputable system instruments to keep away from detection
- Customized malware deployment: Together with backdoors, loaders, and credential stealers
- Persistence mechanisms: Resembling scheduled duties and renamed administrative accounts
Their malware arsenal is intensive, starting from instruments like Mimikatz for credential extraction to damaging wipers like Destover. This versatility permits them to pivot between espionage, disruption, and monetary theft relying on mission goals.
Response and Restoration
Bitrefill has said that it’s going to take up the monetary losses by its operational capital. The corporate additionally engaged a number of cybersecurity companies and legislation enforcement businesses to analyze the breach and strengthen its defenses.
Publish-incident measures embody:
- Enhanced entry controls
- Expanded logging and monitoring capabilities
- Ongoing penetration testing
- Improved incident response procedures
Notably, the platform’s design, minimizing saved private knowledge and avoiding necessary KYC, helped restrict the potential influence on customers.
By March 5, the corporate had restored its methods, with funds, stock, and consumer accounts returning to regular operation.
Conclusion
The Bitrefill cyberattack exhibits how Lazarus Group, DPRK, and North Korean hackers’ cryptocurrency operations exploit human error, legacy credentials, and restricted visibility to entry methods and drain belongings. The incident highlights that defending towards Lazarus Group crypto assaults is dependent upon strict credential hygiene, behavioral monitoring, and fast anomaly detection somewhat than perimeter defenses alone.
It additionally reinforces that limiting knowledge publicity and entry scope reduces breach influence. Intelligence-led platforms like Cyble present real-time risk intelligence and visibility to detect and reply to such intrusions sooner. Organizations seeking to strengthen resilience towards North Korean hackers’ cryptocurrency threats can schedule a demo with Cyble to see how AI-native risk intelligence and real-time detection may help establish and cease assaults earlier than they escalate.


