In case you have ever acquired a boring electronic mail a few enterprise contract or a ‘request order,’ you may need clicked it with out considering twice. However a brand new report means that these routine messages are actually a part of a deliberate rip-off.
Cybersecurity researchers at Forcepoint have found a brand new phishing rip-off by which attackers are utilizing a “multi-stage” course of to remain invisible and obtain their true purpose of stealing your login particulars.
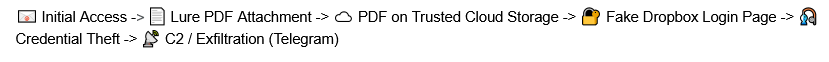
Most electronic mail scams are caught by filters as a result of they comprise malicious hyperlinks or viruses. This one is totally different. It begins with a professional-looking electronic mail, often a few “tender” or “procurement” deal. The e-mail itself is totally clear. It depends on a PDF attachment to do the soiled work.
In response to X-Labs’ investigation, shared with Hackread.com, these PDFs use technical settings like AcroForms and FlateDecode. Merely put, this enables the scammers to cover clickable buttons inside a doc that appears like a traditional workplace file. As a result of we usually belief PDFs greater than hyperlinks in an electronic mail, the attackers are banking on that.
A well-coordinated rip-off
As soon as a person clicks the hyperlink contained in the PDF, they’re despatched to a second doc. This second file is hosted on Vercel Blob storage, a legit cloud service. Kumar notes within the weblog publish that through the use of a “trusted cloud infrastructure,” the scammers handle to bypass safety software program that often blocks unknown or suspicious web sites.
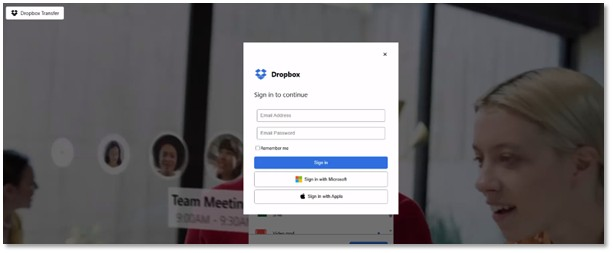
This cloud-hosted file lastly leads victims to a pretend Dropbox login web page, which is designed to look precisely like the actual factor. Nonetheless, behind the scenes, a script is working to steal your electronic mail, password, and your precise IP deal with. It even logs your location, together with your metropolis and nation, and the kind of gadget you’re utilizing.
The place the Knowledge Goes
So, what occurs to your password? The analysis reveals that the stolen knowledge is shipped on to a personal channel on Telegram.
“The script is designed to seize person credentials,” Kumar explains, earlier than sending them to a “hardcoded” Telegram bot managed by the hackers. To maintain the sufferer in the dead of night, the pretend website is ready as much as all the time present an error message, making you assume you simply typed your password flawed whereas the hackers are already strolling away together with your knowledge.
Whereas Forcepoint has up to date its programs to dam these recordsdata, it’s reminder for the remainder of us: if a enterprise doc instantly asks for a login, it is likely to be time to double-check the sender.