The Power Sector’s Ransomware Nightmare: Why Essential Infrastructure Can’t Catch a Break
Power sector ransomware nightmare continued in 2025 however right here’s classes to be taught for crucial infrastructure safety in 2026.
Let’s speak in regards to the sector that retains our lights on, water working, and industries buzzing—and why it’s grow to be ransomware’s favourite goal.
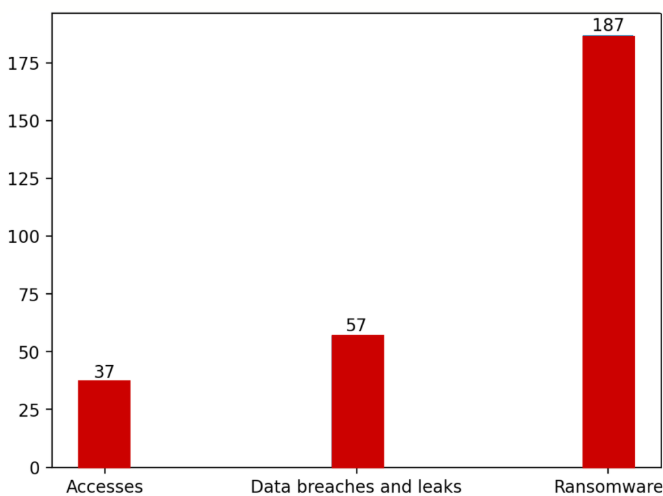
In 2025, the worldwide vitality and utilities sector confronted 187 confirmed ransomware assaults. Not makes an attempt. Confirmed, profitable intrusions the place attackers locked techniques, stole information, and demanded cost. And that’s simply what we find out about.
When you suppose that quantity sounds alarming, you’re paying consideration.
When Ransomware Hits The place It Hurts
Right here’s the factor about attacking vitality infrastructure: the influence cascades. When ransomware paralyzed Halliburton’s operations in August 2025, the corporate disclosed a $35 million loss. When hackers utilizing FrostyGoop malware hit a Ukrainian municipal vitality firm, residents in Lviv misplaced heating throughout sub-zero temperatures.
These aren’t summary information breaches. They’re disruptions that have an effect on hundreds of thousands of people that depend upon important companies. And attackers know this—which makes vitality firms prime targets for extortion.
The ransomware teams main this assault? RansomHub tops the record with 24 incidents (12.8% of the entire), adopted intently by Akira with 20 assaults (10.7%) and Play with 18 (9.6%). Throw in Qilin and Hunters/Lynx, and you’ve received 5 crews chargeable for practically half of all ransomware incidents in opposition to vitality targets worldwide.
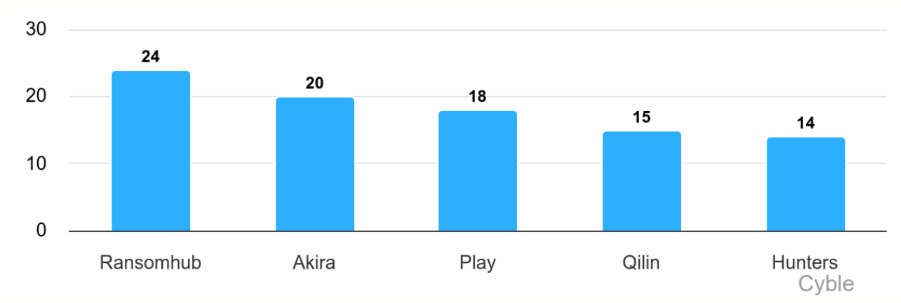
That’s not a various risk panorama—that’s concentrated, organized, industrial-scale cybercrime concentrating on crucial infrastructure.
Why Power? Comply with the Vulnerability
Power firms face an ideal storm of assault vectors that the majority sectors don’t cope with.
Legacy Infrastructure
Many energy crops, refineries, and water remedy services run on operational expertise (OT) techniques which can be a long time outdated. We’re speaking about industrial management techniques working outdated protocols like Modbus and DNP3—designed in an period when “cybersecurity” wasn’t even an idea. These techniques had been constructed for reliability and uptime, not community protection.
IT-OT Convergence
As vitality firms digitized operations for effectivity, they related beforehand remoted industrial techniques to company IT networks. That convergence created pathways for attackers to maneuver from phishing an worker’s laptop computer to accessing SCADA techniques controlling bodily infrastructure.
Distributed Assault Floor
Not like a financial institution with centralized information facilities, vitality infrastructure is geographically dispersed. Photo voltaic farms, wind installations, substations, pipeline monitoring stations—every represents a possible entry level. And managing safety throughout lots of or hundreds of distant websites? That’s a nightmare.
The Numbers Inform a Grim Story
Between July 2024 and June 2025, the vitality sector didn’t simply face ransomware. It received hit from each angle:
- 37 incidents of compromised community entry marketed on the market on legal boards
- 57 information breach and leak occasions exposing delicate operational information
- 187 ransomware assaults encrypting techniques and exfiltrating recordsdata
- Over 39,000 hacktivist posts concentrating on vitality infrastructure
To get the entire evaluation on information breaches, ransomware assaults and attackers, hacktivists, and vulnerabilities plaguing the vitality and utilities sector worldwide, obtain Cyble’s full report now!
North America bore the brunt of ransomware assaults, accounting for over one-third of incidents. However Asia and Europe weren’t far behind, every absorbing important parts of compromised entry gross sales and information breaches.
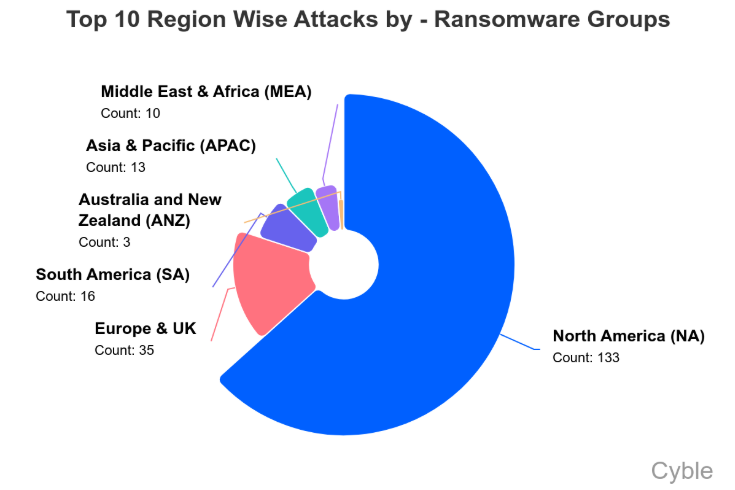
This geographic distribution tells us one thing necessary: attackers aren’t centered on one area. They’re systematically concentrating on vitality infrastructure globally, exploiting whichever networks supply the best entry.
The Dealer Economic system Feeding the Fireplace
Right here’s a disturbing pattern: preliminary entry brokers are specializing in vitality targets.
Through the reporting interval, Zerosevengroup, mommy, and miyako led gross sales of compromised vitality sector credentials. Collectively, they posted about 27% of noticed entry choices. That may not sound like a lot till you notice the remaining 73% was cut up amongst dozens of one-time sellers.
What this fragmentation means: obstacles to entry for attacking vitality infrastructure are low. You don’t have to be an elite hacker anymore. Simply purchase credentials from a dealer for a couple of thousand {dollars}, and you’ve received a foothold in an influence firm’s community.
One notably alarming itemizing? In March 2025, ZeroSevenGroup marketed admin-level entry to a UAE water and energy holding firm, claiming attain over 5,000 community hosts. One other dealer provided entry to an Indonesian energy plant operations subsidiary. A 3rd claimed control-level entry to a French wastewater remedy platform.
These aren’t theoretical vulnerabilities. They’re lively legal ads providing patrons the keys to crucial infrastructure.
When Hacktivists Goal the Grid
Geopolitical hacktivist teams added one other dimension to the risk panorama in 2025—and a few crossed strains that genuinely matter.
Professional-Russian teams like Sector 16 didn’t simply deface web sites or leak stolen paperwork. They claimed—and offered video proof of—precise manipulation of operational expertise at US oil and gasoline services. We’re speaking about interfaces controlling shutdown techniques, manufacturing monitoring, gas-lift controls, and valve actuation.
Whether or not they may have brought on bodily injury is debatable. That they’d entry to attempt? Plain.
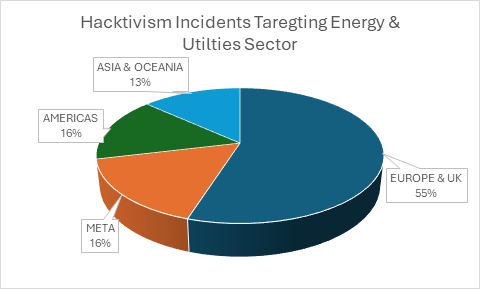
Equally, the Golden Falcon Workforce claimed breach of a French wastewater monitoring platform with entry to pH controls, temperature settings, and water distribution parameters. Once more, the claimed stage of entry would enable manipulation of real-world bodily processes.
Most hacktivist exercise in 2025 consisted of low-level DDoS assaults and propaganda—extra noise than real risk. However when teams begin demonstrating OT entry? That’s crossing from nuisance into harmful territory.
The Colonial Pipeline Echo
Bear in mind Could 2021? The Colonial Pipeline ransomware assault that brought on gas shortages throughout the US East Coast?
That incident was speculated to be a wake-up name. Colonial provides 45% of gas for the East Coast. The assault compelled them to pay $5 million in ransom simply to renew operations. Panic shopping for. Gasoline station shortages. Financial disruption.
4 years later, we’re seeing related assaults globally however with quicker execution. The median time from breach to encryption has collapsed. Trendy ransomware teams transfer by way of networks in hours, not weeks. They know precisely which techniques to focus on for optimum leverage.
And right here’s the kicker: many of those assaults succeed utilizing identified vulnerabilities that victims merely hadn’t patched.
Vulnerabilities: The Similar Previous Story
All through 2025, attackers exploited crucial flaws in techniques that vitality firms depend upon day by day:
- ABB ASPECT techniques utilized in substations
- Siemens SENTRON PAC3200 energy meters
- Mass-deployed photo voltaic inverter platforms
- Schneider Electrical Jira situations
- Numerous VMware, Ivanti, and Fortinet merchandise
What’s irritating is that patches existed for many of those. The median remediation time throughout vitality enterprises exceeded 21 days—whereas attackers had been weaponizing exploits inside 72 hours of public disclosure.
That 18-day hole? That’s your publicity window. That’s when you’re weak to assaults utilizing publicly documented strategies that everybody is aware of about.
What Protection Appears Like
So what truly works when you’re defending vitality infrastructure in opposition to this onslaught?
Section All the things
Your OT networks shouldn’t be reachable from company IT. Interval. Air-gap the place potential. When connection is important, lock it down with rigorous entry controls, monitoring, and authentication. Each pathway between IT and OT is a possible assault vector.
Hunt the Dealer Market
Steady monitoring of legal boards isn’t only for intelligence companies anymore. Organizations want visibility into whether or not their credentials or community entry is being marketed on the market. Discovering out after an assault that your entry was bought three months earlier? That’s too late.
Patch with Urgency
I do know, I do know—patching OT techniques is advanced. Downtime is dear. Testing is gradual. However you recognize what’s dearer? Halliburton’s $35 million ransomware loss. Or NovaScotia Energy coping with 280,000 clients’ uncovered information.
Create aggressive patch timelines. Take a look at in parallel. Prioritize internet-facing techniques and identified exploited vulnerabilities. Transfer quick.
Put together for the Worst
Each vitality firm ought to have examined incident response playbooks that assume profitable breach. Are you able to isolate compromised techniques? Do you may have offline backups they can’t encrypt? Can you turn to guide operations if SCADA goes down? Have you ever drilled these situations?
As a result of when ransomware locks your techniques at 3 AM on a Sunday, you gained’t have time to determine it out.
The Sincere Reality
Right here’s what no person needs to say out loud: good safety for vitality infrastructure is inconceivable.
The assault floor is just too massive. The techniques are too outdated. The connectivity necessities are too advanced. The attacker economics favor offense.
However good safety isn’t the objective. Resilience is.
Resilient organizations detect breaches rapidly. They reply successfully. They recuperate with out paying ransoms. They be taught from incidents and enhance their defenses.
The vitality sector can’t eradicate ransomware danger. However it might probably cut back the window of publicity, restrict the blast radius, and guarantee continuity of crucial operations even underneath assault.
As a result of the subsequent assault isn’t coming sometime. It’s in all probability taking place proper now, someplace within the provide chain, and the query is whether or not defenses will catch it earlier than ransomware deploys.
For vitality and utilities operators navigating the 2026 risk panorama, the problem is obvious: defend infrastructure designed for a pre-internet period in opposition to adversaries armed with industrialized assault instruments. Resilience isn’t optionally available anymore—it’s survival.

