SloppyLemming, an India-linked espionage group also referred to as Outrider Tiger and Fishing Elephant, has run a year-long cyber marketing campaign towards excessive‑worth targets in Pakistan and Bangladesh utilizing a brand new BurrowShell backdoor and a Rust-based distant entry software (RAT).
This exercise builds straight on earlier operations uncovered by Cloudflare’s CloudForce One in 2024. Nonetheless, it exhibits clear enlargement in each tooling and infrastructure scale.
Arctic Wolf hyperlinks this marketing campaign to SloppyLemming with average confidence, citing a constant South Asia sufferer profile, reuse of Cloudflare Staff infrastructure, acquainted area typosquatting patterns, and continued reliance on frameworks like Havoc alongside customized malware.
Arctic Wolf noticed SloppyLemming focusing on authorities businesses and important infrastructure operators in Pakistan and Bangladesh, together with protection, telecom, power, monetary, and nuclear regulatory organizations.
Twin Assault Chains
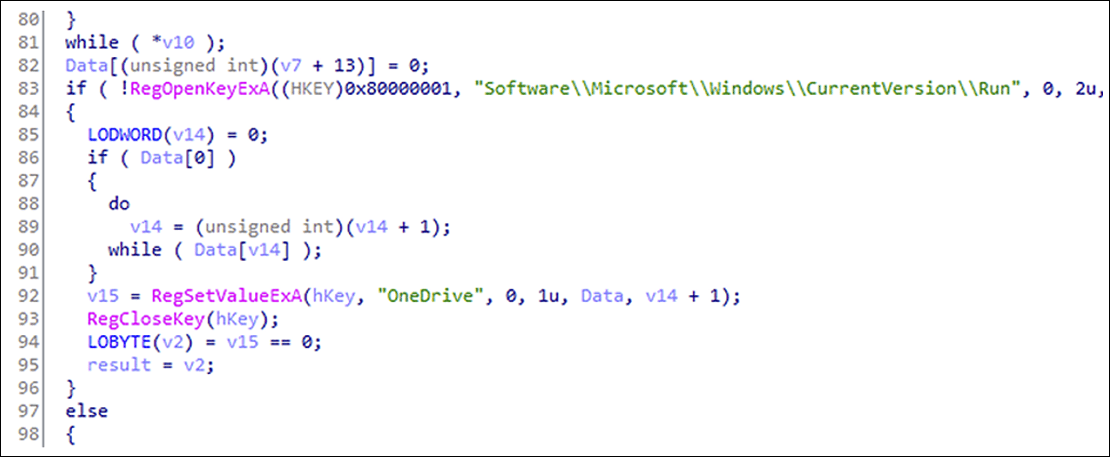
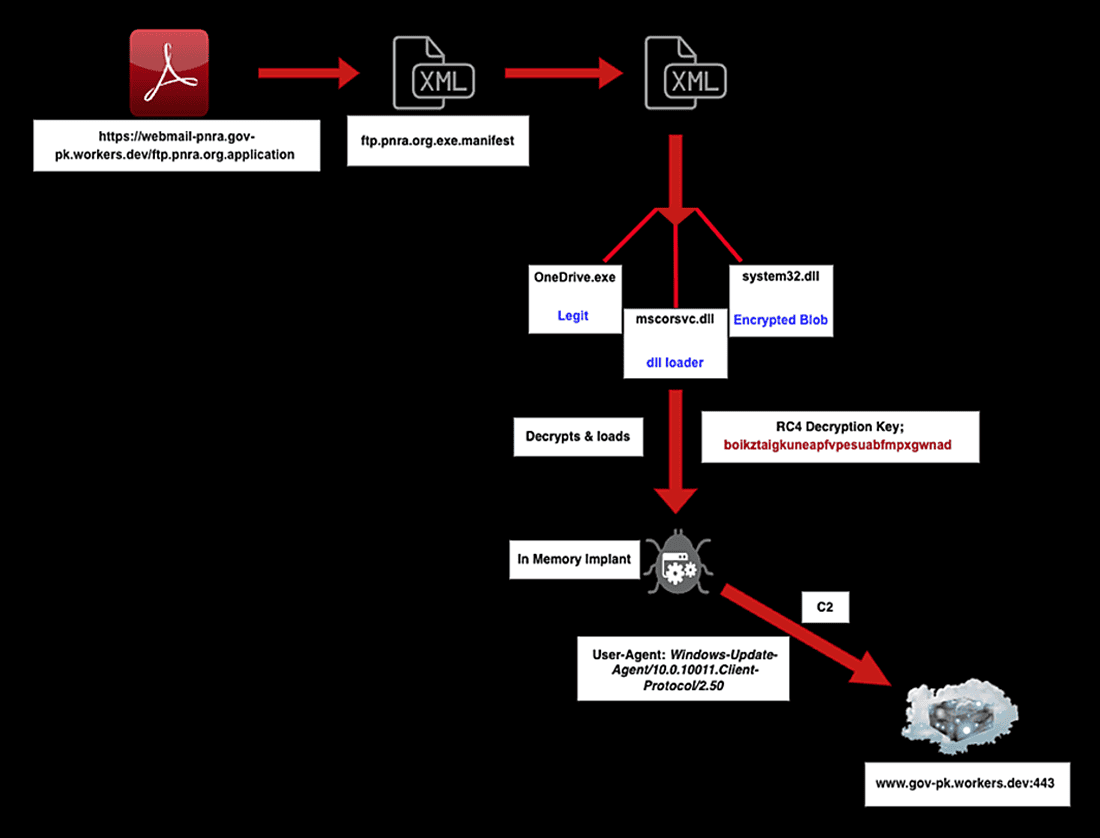
SloppyLemming now makes use of two most important spear‑phishing chains to deploy its malware. The first chain sends PDF lures that push victims to ClickOnce software manifests, which then ship a DLL sideloading bundle abusing respectable Microsoft binaries equivalent to NGenTask.exe to load a malicious mscorsvc.dll loader and an encrypted shellcode blob.
As soon as decrypted, that shellcode runs BurrowShell, an in‑reminiscence backdoor that helps file operations, screenshot seize, distant command execution, and SOCKS proxy tunneling whereas disguising its command‑and‑management visitors as Home windows Replace over HTTPS.
The secondary chain depends on macro‑enabled Excel information to obtain and execute a renamed Microsoft binary that sideloads sppc.dll, a Rust‑based mostly keylogger and RAT.
This Rust implant logs keystrokes, runs instructions, performs file manipulation, conducts port scanning and community reconnaissance, and captures screenshots, marking a shift from SloppyLemming’s earlier dependence on solely conventional compiled malware and off‑the‑shelf emulation frameworks like Cobalt Strike and Havoc.
Infrastructure evaluation exhibits SloppyLemming has tremendously scaled its use of Cloudflare Staff, registering 112 employees.dev subdomains between January 2025 and January 2026, in comparison with simply 13 such domains beforehand documented by Cloudflare in 2024.
These domains intently mimic Pakistani and Bangladeshi authorities and important infrastructure entities and are used for each payload supply and C2 visitors.
Regardless of this superior setup, a number of Staff situations had been left as open directories, unintentionally exposing staged malware, together with BurrowShell parts and Havoc loaders secured with distinct RC4 keys.
This operational safety lapse allowed researchers to recuperate extra tooling and make sure SloppyLemming’s continued reliance on the Havoc framework in parallel with its new customized implants.
Affect, Attribution, and Protection
The marketing campaign’s focusing on of Pakistani nuclear regulation, protection logistics, and telecom, alongside Bangladeshi energy and monetary establishments, aligns with strategic intelligence assortment priorities in South Asia and reinforces assessments that SloppyLemming operates in help of India‑nexus pursuits.
The implant contains an inside occasion messaging mechanism known as “OneCollector” within the code, doubtless designed to imitate respectable Microsoft telemetry endpoints.
Extra protections embody blocking identified malicious employees.dev hostnames, inspecting outbound HTTPS visitors that imitates Home windows Replace or customized Rust‑tooling person‑brokers, and deploying detection content material equivalent to YARA guidelines particularly tuned for BurrowShell and the Rust keylogger implants.
Arctic Wolf maps the exercise throughout a large span of MITRE ATT&CK strategies, together with spear‑phishing, DLL search order hijacking, encrypted internet C2, keylogging, and inside proxying utilizing SOCKS tunnels.
To counter this risk, defenders are suggested to tightly management macros, scrutinize PDFs and embedded URLs pointing to employees.dev domains, monitor for suspicious ClickOnce deployments, and hunt for DLL sideloading involving NGenTask.exe or phoneactivate.exe in non‑normal paths.
Comply with us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most well-liked Supply in Google.

